Sticky Postings
All 242 fabric | rblg updated tags | #fabric|ch #wandering #reading
By fabric | ch
-----
As we continue to lack a decent search engine on this blog and as we don't use a "tag cloud" ... This post could help navigate through the updated content on | rblg (as of 09.2023), via all its tags!
FIND BELOW ALL THE TAGS THAT CAN BE USED TO NAVIGATE IN THE CONTENTS OF | RBLG BLOG:
(to be seen just below if you're navigating on the blog's html pages or here for rss readers)
--
Note that we had to hit the "pause" button on our reblogging activities a while ago (mainly because we ran out of time, but also because we received complaints from a major image stock company about some images that were displayed on | rblg, an activity that we felt was still "fair use" - we've never made any money or advertised on this site).
Nevertheless, we continue to publish from time to time information on the activities of fabric | ch, or content directly related to its work (documentation).
Monday, February 22. 2016
A computer trying to order a pizza (and having a hard time), back in 1974 | #computing #txt2speech #history
Note: can a computer "fake" a human? (hmmm, sounds a bit like Mr. Turing test isn't it?) Or at least be credible enough --because it sounds pretty clear in this video, at that time, that it cannot fake a human and that it is m ore about voice than "intelligence"-- so that the person on the other side of the phone doesn't hang up? This is a funny/uncanny experiment involving D. Sherman at Michigan State University, dating back 1974 and certainly one of the first public trial (or rather social experiment) of a text to speech/voice synthesizer.
Beyond the technical performance, it is the social experiment that is probably even more interesting. It's intertwined and odd nature. You can feel in the voice of the person on the other side of the phone (at the pizza factory --Domino's pizza--) that he really doesn't know how to take it and that the voice sounds like something not heard before. A few trials were necessary before somebody took it "seriously".
Via @toxi
-----
By John Eulenberg (publication on Youtube)
Every year, the researchers, students, and technology users who make up the community of the Michigan State University Artificial Language Laboratory celebrate the anniversary of the first use of a speech prosthesis in history: the use by a man with a communication disorder to order a pizza over the telephone using a voice synthesizer. This high-tech sociolinguistic experiment was conducted at the Lab on the evening of December 4, 1974. Donald Sherman, who has Moebius Syndrome and had never ordered a pizza over the phone before, used a system designed by John Eulenberg and J. J. Jackson incorporating a Votrax voice synthesizer, a product of the Federal Screw Works Co. of Troy, Michigan. The inventor of the Votrax voice synthesizer was Richard Gagnon from Birmingham, MI.
The event was covered at the time by the local East Lansing cable news reporter and by a reporter from the State News. About seven years later, in 1981, a BBC production team produced a documentary about the work of the Artificial Language Laboratory and included a scene of a man with cerebral palsy, Michael Williams, ordering a pizza with a newer version of the Lab's speech system. This second pizza order became a part of the documentary, which was broadcast throughout the U.S. as part of the "Nova" science series and internationally as part of the BBC's "Horizon" series.
In January, 1982, the Nova show on the Artificial Language Lab was shown for the first time. The Artificial Language Lab held a premiere party in the Communication Arts and Sciences Building for all the persons who appeared in the program plus all faculty members of the College of Communication Arts and Sciences and their families. The Domino's company generously provided free pizzas for all the guests.
The following December, Domino's again provided pizzas for a party, again held at the Communication Arts building, to commemorate the first ordering of a pizza eight years earlier. The Convocation was held thereafter every year through 1988, each year receiving pizzas through the generous gift of Domino's.
A Communication Enhancement Convocation was held in 1999, celebrating the 25th anniversary of the first pizza order.In addition to Dominos's contribution of pizzas, the Canada Dry Bottling Co. of Lansing provided drinks.The Convocations resumed in 2010 through 2012, when Dr. John Eulenberg advanced to Professor Emeritus status.
At each event, in addition to faculty and students, the convocation guests included local dignitaries from the MSU board of trustees and from the Michigan state legislature. Stevie Wonder, whose first talking computer and first singing computer were designed at the Artificial Language Lab, made telephone appearances and spoke with the youngsters using Artificial Language Lab technology through their
school district special education programs. MSU icons such as the football team, Sparty, and cheer leaders made appearances as well.
Now, through YouTube, we can relive this historical moment and take a thoughtful look back at 40 years of progress in the delivery of augmentative communication technology to persons with disabilities.
Tuesday, April 28. 2015
Signal-Blocking Architecture and the Faraday Home | #faraday
Via BLDGBLOG
-----
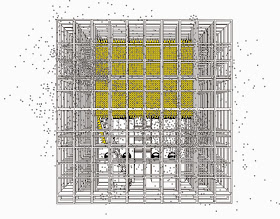
Image: "RAM House" by Space Caviar].
An interesting new project by Space Caviar asks, "Does your home have an airplane mode?"
Exploring what it could mean to design future homes so that they offer an optional state of complete electromagnetic privacy, they have put together a "domestic prototype" in which the signal-blocking capabilities of new architectural materials are heavily emphasized, becoming a structural component of the house itself.
[Image: "RAM House" by Space Caviar].
In other words, why just rely on aftermarket home alterations such as WiFi-blocking paint, when you can actually factor the transmission of signals through architectural space into the design of your home in the first place?
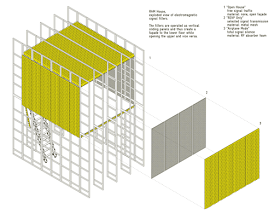
[Image: "RAM House" by Space Caviar].
Space Caviar call this "a new definition of privacy in the age of sentient appliances and signal-based communication," in the process turning the home into "a space of selective electromagnetic autonomy."
As the space of the home becomes saturated by “smart” devices capable of monitoring their surroundings, the role of the domestic envelope as a shield from an external gaze becomes less relevant: it is the home itself that is observing us. The RAM House responds to this near-future scenario by proposing a space of selective electromagnetic autonomy. Within the space’s core, Wi-Fi, cellphone and other radio signals are filtered by various movable shields of radar-absorbent material (RAM) and faraday meshing, preventing signals from entering and—more importantly—escaping. Just as a curtain can be drawn to visually expose the domestic interior of a traditional home, panels can be slid open to allow radio waves to enter and exit, when so desired.
The result is the so-called "RAM House," named for those "movable shields of radar-absorbent material," and it will be on display at the Atelier Clerici in Milan from April 14-19.
Thursday, July 03. 2014
The Emerging Threat from Twitter's Social Capitalists | #social #networks
Note: I'm happy to learn that I'm not a "social capitalist"! I am not a "regular capitalist" either...
Via MIT Technology
-----
Social capitalists on Twitter are inadvertently ruining the network for ordinary users, say network scientists.

A couple of years, ago, network scientists began to study the phenomenon of “link farming” on Twitter and other social networks. This is the process in which spammers gather as many links or followers as possible to help spread their messages.
What these researchers discovered on Twitter was curious. They found that link farming was common among spammers. However, most of the people who followed the spam accounts came from a relatively small pool of human users on Twitter.
These people turn out to be individuals who are themselves trying to amass social capital by gathering as many followers as possible. The researchers called these people social capitalists.
That raises an interesting question: how do social capitalists emerge and what kind of influence do they have on the network? Today we get an answer of sorts, thanks to the work of Vincent Labatut at Galatasaray University in Turkey and a couple of pals who have carried out the first detailed study of social capitalists and how they behave.
These guys say that social capitalists fall into at least two different categories that reflect their success and the roles they play in linking together diverse communities. But they warn that social capitalists have a dark side too.
First, a bit of background. Twitter has around 600 million users who send 60 million tweets every day. On average, each Twitter user has around 200 followers and follows a similar number, creating a dynamic social network in which messages percolate through the network of links.
Many of these people use Twitter to connect with friends, family, news organizations, and so on. But a few, the social capitalists, use the network purely to maximize their own number of followers.
Social capitalists essentially rely on two kinds of reciprocity to amass followers. The first is to reassure other users that if they follow this user, then he or she will follow them back, a process called Follow Me and I Follow You or FMIFY. The second is to follow anybody and hope they follow back, a process called I Follow You, Follow Me or IFYFM.
This process takes place regardless of the content of messages, which is how they get mixed up with spammers, a point that turns out to be significant later.
Clearly, social capitalists are different from Twitter users who choose to follow people based on the content they tweet. The question that Labatut and co set out to answer is how to automatically identify social capitalists in Twitter and to work out how they sit within the Twitter network.
A clear feature of the reciprocity mechanism is that there will be a large overlap between the friends and followers of social capitalists. It’s possible to measure this overlap and categorize users accordingly. Social capitalists tend to have an overlap much closer to 100 percent than ordinary users.
Having identified social capitalists, another important measure is the ratio of friends to followers. Labatut and co say that those using the FMIFY strategy have a ratio smaller than 1 while those using the IFYFM will have a ration greater than 1 (because the number of followers is always greater than the number of friends).
One final way to categorize them is by their level of success. Here, Labatut and others set an arbitrary threshold of 10,000 followers. Social capitalists with more than this are obviously more successful than those with less.
To study these groups, Labatut and coanalyze an anonymized dataset of 55 million Twitter users with two billion links between them. And they find some 160,000 users who fit the description of social capitalist.
In particular, the team is interested in how social capitalists are linked to communities within Twitter, that is groups of users who are more strongly interlinked than average.
It turns out that there is a surprisingly large variety of social capitalists playing different roles. “We find out the different kinds of social capitalists occupy very specific roles,” say Labatut and co.
For example, social capitalists with fewer than 10,000 followers tend not to have large numbers of links within a single community but links to lots of different communities. By contrast, those with more than 10,000 followers can have a strong presence in single communities as well as link disparate communities together. In both cases, social capitalists are significant because their messages travel widely across the entire Twitter network.
That has important consequences for the Twitter network. Labatut and co say there is a clear dark side to the role of social capitalists. “Because of this lack of interest in the content produced by the users they follow, social capitalists are not healthy for a service such as Twitter,” they say.
That’s because they provide an indiscriminate conduit for spammers to peddle their wares. “[Social capitalists’] behavior helps spammers gain influence, and more generally makes the task of finding relevant information harder for regular users,” say Labatut and co.
That’s an interesting insight that raises a tricky question for Twitter and other social networks. Finding social capitalists should now be straightforward now that Labatut and others have found a way to spot them automatically. But if social capitalists are detrimental, should their activities be restricted?
Ref:
http://arxiv.org/abs/1406.6611 : Identifying the Community Roles of Social Capitalists in the Twitter Network.
http://www.mpi-sws.org/~farshad/TwitterLinkfarming.pdf : Understanding and Combating Link Farming in the Twitter Social Network
Monday, June 30. 2014
Balloon-Powered Internet For Everyone | #atmosphere #network
Note: I've already collected articles about this project, which interestingly, would add a permanent human presence in a layer of the atmosphere (the statosphere) where humans were not or very rarely present up to now. We also have to underline the fact that this will be an additionnal move toward the "brandification/privatization" (of the upper levels of our atmosphere --stratosphere, thermosphere-- and outer space).
It is interesting indeed, with clever worlds like "bringing the internet to million of people". Yet some other ones have a more critical view upon this strategic move by corporate interests: read Google Eyes in the Sky (by Will Oremus on Slate)
Via Next Nature
-----

Balloon-Powered Internet For Everyone
Both Google and Facebook have challenging intentions to bring the Internet to the next billion people, and while Zuckerberg’s dream involves drones with lasers, Google is planning to create a hot air balloon network.
With a system of balloons traveling on the edge of space, Project Loon will attempt to connect to internet the two-thirds of the world’s population that doesn’t have access to the Net. The balloons will float in the stratosphere, twice as high as airplanes and the weather. Users can connect to the network using a specific Internet antenna attached to their building.
“Project Loon uses software algorithms to determine where its balloons need to go, then moves each one into a layer of wind blowing in the right direction. By moving with the wind, the balloons can be arranged to form one large communications network” is explained on Project Loon website.
Currently, Google is still in the testing phase to learn more about wind patterns, and improve the balloons design. A step toward universal Internet connection?
Find more at Project Loon
Related Links:
Monday, May 19. 2014
The internet will have almost 3 billion users by the end of the year, UN report says | #infrastructure #global
Via The Verge (via Computed·Blg)
-----

The internet will have nearly 3 billion users, about 40 percent of the world's population, by the end of 2014, according to a new report from the United Nations International Telecommunications Union. Two-thirds of those users will be in developing countries.
Those numbers refer to people who have used the internet in the last three months, not just those who have access to it.
Internet penetration is reaching saturation in developed countries, while it's growing rapidly in developing countries. Three out of four people in Europe will be using the internet by the end of the year, compared to two out of three in the Americas and one in three in Asia and the Pacific. In Africa, nearly one in five people will be online by the end of the year.
Mobile phone subscriptions will reach almost 7 billion. That growth rate is slowing, suggesting that the number will plateau soon. Mobile internet subscriptions are still growing rapidly, however, and are expected to reach 2.3 billion by the end of 2014.
These numbers make it easy to imagine a future in which every human on Earth is using the internet. The number of people online will still be dwarfed by the number of things, however. Cisco estimates the internet already has 10 billion connected devices and is expected to hit 50 billion by 2020.
Thursday, April 24. 2014
Les-tuh skwair | #algorithm
-----
“As algorithmic systems become more prevalent, I’ve begun to notice of a variety of emergent behaviors evolving to work around these constraints, to deal with the insufficiency of these black box systems…The first behavior is adaptation. These are situations where I bend to the system’s will. For example, adaptations to the shortcomings of voice UI systems — mispronouncing a friend’s name to get my phone to call them; overenunciating; or speaking in a different accent because of the cultural assumptions built into voice recognition. We see people contort their behavior to perform for the system so that it responds optimally.”
Alexis Lloyd (NYTimes R&D) shares some interesting views under the title In the Loop: Designing Conversations with Algorithms.
Wednesday, February 26. 2014
Picture Piece: Cybersyn, Chile 1971-73 | #cybernetic #history
Three years ago we published a post by Nicolas Nova about Salvator Allende's project Cybersyn. A trial to build a cybernetic society (including feedbacks from the chilean population) back in the early 70ies.
Here is another article and picture piece about this amazing projetc on Frieze. You'll need to buy the magazione to see the pictures, though!
-----
Via Frieze
Phograph of Cybersyn, Salvador Allende's attempt to create a 'socialist internet, decades ahead of its time'

This is a tantalizing glimpse of a world that could have been our world. What we are looking at is the heart of the Cybersyn system, created for Salvador Allende’s socialist Chilean government by the British cybernetician Stafford Beer. Beer’s ambition was to ‘implant an electronic nervous system’ into Chile. With its network of telex machines and other communication devices, Cybersyn was to be – in the words of Andy Beckett, author of Pinochet in Piccadilly (2003) – a ‘socialist internet, decades ahead of its time’.
Capitalist propagandists claimed that this was a Big Brother-style surveillance system, but the aim was exactly the opposite: Beer and Allende wanted a network that would allow workers unprecedented levels of control over their own lives. Instead of commanding from on high, the government would be able to respond to up-to-the-minute information coming from factories. Yet Cybersyn was envisaged as much more than a system for relaying economic data: it was also hoped that it would eventually allow the population to instantaneously communicate its feelings about decisions the government had taken.
In 1973, General Pinochet’s cia-backed military coup brutally overthrew Allende’s government. The stakes couldn’t have been higher. It wasn’t only that a new model of socialism was defeated in Chile; the defeat immediately cleared the ground for Chile to become the testing-ground for the neoliberal version of capitalism. The military takeover was swiftly followed by the widespread torture and terrorization of Allende’s supporters, alongside a massive programme of privatization and de-regulation. One world was destroyed before it could really be born; another world – the world in which there is no alternative to capitalism, our world, the world of capitalist realism – started to emerge.
There’s an aching poignancy in this image of Cybersyn now, when the pathological effects of communicative capitalism’s always-on cyberblitz are becoming increasingly apparent. Cloaked in a rhetoric of inclusion and participation, semio-capitalism keeps us in a state of permanent anxiety. But Cybersyn reminds us that this is not an inherent feature of communications technology. A whole other use of cybernetic sytems is possible. Perhaps, rather than being some fragment of a lost world, Cybersyn is a glimpse of a future that can still happen.
Tuesday, February 04. 2014
Appropriating Interaction Technologies (Social Hacking) at ITP | #code
-----
By Lauren McCarthy & Kyle McDonald
AIT (“Social Hacking”), taught for the first time this semester by Lauren McCarthy and Kyle McDonald at NYU’s ITP, explored the structures and systems of social interactions, identity, and self representation as mediated by technology. The semester was spent developing projects that altered or disrupted social space in an attempt to reveal existing patterns or truths about our experiences and technologies, and possibilities for richer interactions.
The class began by exploring the idea of “social glitch”, drawing on ideas from glitch theory, social psychology, and sociology, including Harold Garfinkel’s breaching experiments, Stanley Milgram’s subway experiments, and Erving Goffman’s dramaturgical analysis of social interaction. If “glitch” describes when a system breaks down and reveals something about its structure or self in the process, what might this look like in the context of social space?
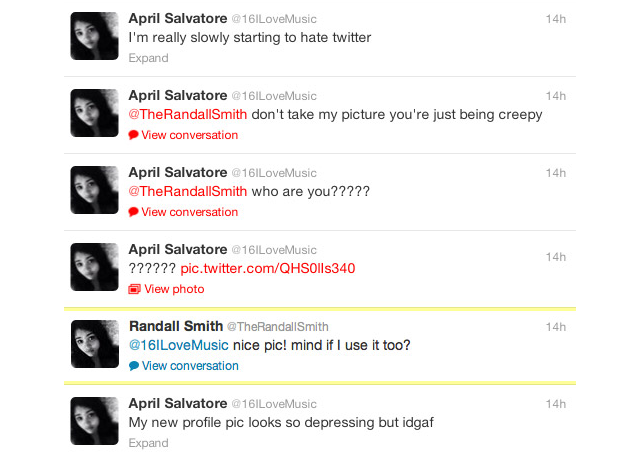
Bill Lindmeier wrote a Ruby script using the Twitter Stream API to listen for any Tweets containing “new profile pic.” When a Tweet was posted the script would download the user’s profile image, upload it to his own account and then reply to the user with a randomly selected Tweet, like “awesome pic!”. The reactions ranged from humored to furious.
Along similar lines, Ilwon Yoon implemented a script that searched for Tweets containing “I am all alone” and replied with cute images obtained from a Google image search and “you are not alone” text.
Mack Howell built on the in-class exercise of asking strangers to borrow their phone then doing something unexpected with it, asking to take pictures of strangers’ browsing history.
The class next turned it’s attention to social automation and APIs, and the potential for their creative misuse.
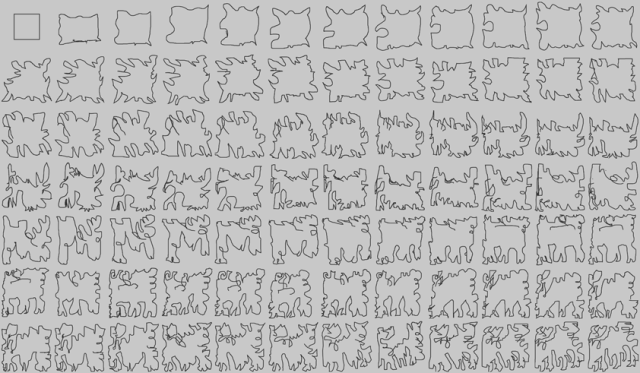
Gal Sasson used the Amazon Mechanical Turk API to create collaborative noise, creating a chain where each turker was prompted to replicate a drawing from the previous turker, seeding the first turker with a perfect square.
Mack Howell used the Google Street View Image API to map out the traceroutes from his location to the data centers of the his most frequently visited IPs.
In another assignment, students were prompted to create an “HPI” (human programming interface) that allowed others to control some aspect of their lives, and perform the experiment for one full week.
Anytime an email or Twitter direct message was sent to Ben Kauffman with the hashtag #brainstamp and a mailing address, he would get an SMS with the information and promptly right down on a postcard whatever was in his head at that exact moment. He would then mail the thoughts, at turns surreal and mundane, to the awaiting recipient. An alternative to normal social media, Ben challenged us to find ways to be more present while documenting our lives.
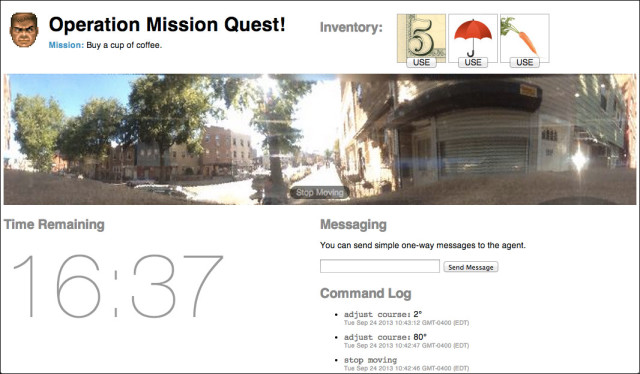
Bill Lindmeier invited his friends to control his movements in realtime through a Google-street-view-esque video interface, and asked them to complete a simple mission: Buy some coffee in under 20 minutes. The tools at their disposal: $5, an umbrella and a carrot.
Mack Howell created a journal written by Amazon Mechanical Turk workers, asking them to generate diary entries based on OpenPaths data sent automatically as he moved around.
In a project called My Friends Complete Me, Su Hyun Kim posted binary questions on Facebook, Twitter and Instagram, and let her friends collective opinion determine her life choices, including deciding whether to change her last name when she got married.
A couple weeks were spent having focused discussions about security, privacy, and surveillance, including topics like quantified self, government surveillance and historical regimes of naming, and readings from Bruce Schneier, Evgeny Morozov and Steve Mann. In parallel, students were asked to examine their own social lives and compulsively document, share, intercept, impersonate, anonymize and misinterpret.
Mike Allison explored our voyeuristic nature and cultural craving for surveillance, allowing users to watch someone watch someone who may be watching them. In order to watch, users must lend their own camera to the system.
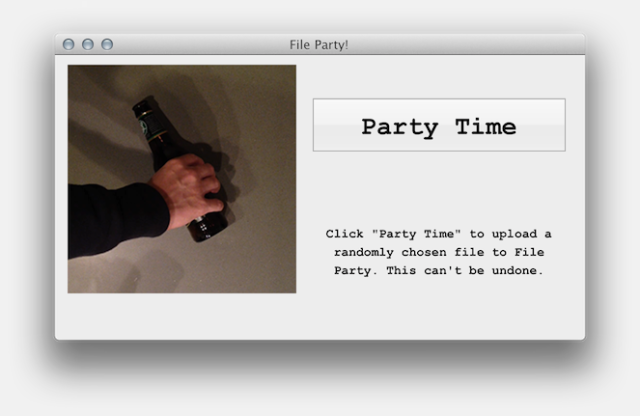
Bill Lindmeier created an app called File Party, a repository of files that have been randomly selected and uploaded from peoples’ hard-drive. In order to view the files, you have to upload one yourself.
In a unit on computer vision and linguistic analysis, students were paired up and asked to create a chat application that provided a filter or adapter that improved their interaction.
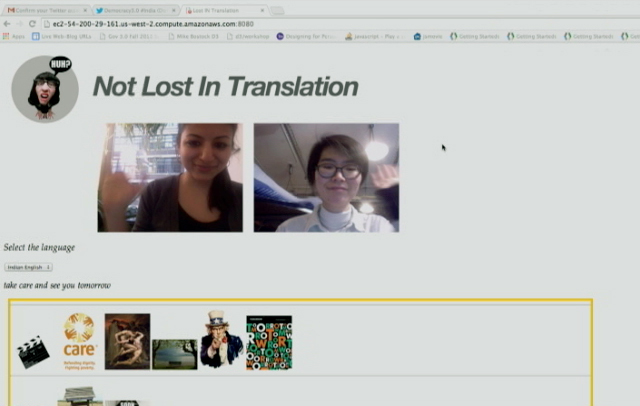
Realizing how much is lost in translation and accents, Tarana Gupta and Hanbyul Jo developed a video chat tool which allows users to talk in their respective language and and displays in real-time text and images corresponding to what is being said.
In FlapChat, Su Hyun Kim and Gal Sasson rethought the way we interact with the web camera, allowing users to flap their arms to fly around a virtual environment while chatting.
Overall, the most successful moments in the class were the ones where students had an opportunity to examine an otherwise common technology or interaction from a new perspective. Short in-class exercises like “ask a stranger to use their phone, and do something unexpected” gave students a reference point for discussion. The “HPI” assignment gave students an unusual challenge of “performing” something for a week, lead to its own set of difficulties and realizations that are distinct from purely technical or aesthetic exercises. On the first day of class a contract was handed out requiring that students respect others’ positions in class, and take responsibility for any actions outside of class. This created a unfamiliar atmosphere and opened up the students to question their freedoms and responsibilities towards each other.
In the future, each two- or three-week section might be expanded to fit a whole semester. Of particular interest were the computer vision, security and surveillance, and mobile platforms sections. Leftover discussion from security and surveillance spilled into the next week, and assignments for mobile platforms could have been taken far beyond the proof-of-concept or design-only stages.
More information about the class, including the complete syllabus, reading lists, and some example code, is available on GitHub.
A condensed version of this class will be taught in January at GAFFTA in San Francisco, details will be announced soon with more information here.
About the Tutors:
Kyle McDonald is a media artist who works with code, with a background in philosophy and computer science. He creates intricate systems with playful realizations, sharing the source and challenging others to create and contribute. Kyle is a regular collaborator on arts-engineering initiatives such as openFrameworks, having developed a number of extensions which provide connectivity to powerful image processing and computer vision libraries. For the past few years, Kyle has applied these techniques to problems in 3D sensing, for interaction and visualization, starting with structured light techniques, and later the Kinect. Kyle’s work ranges from hyper-formal glitch experiments to tactical and interrogative installations and performance. He was recently Guest Researcher in residence at the Yamaguchi Center for Arts and Media, Japan, and is currently adjunct professor at ITP.
Lauren McCarthy is an artist and programmer based in Brooklyn, NY. She is adjunct faculty at RISD and NYU ITP, and a current resident at Eyebeam. She holds an MFA from UCLA and a BS Computer Science and BS Art and Design from MIT. Her work explores the structures and systems of social interactions, identity, and self-representation, and the potential for technology to mediate, manipulate, and evolve these interactions. She is fascinated by the slightly uncomfortable moments when patterns are shifted, expectations are broken, and participants become aware of the system. Her artwork has been shown in a variety of contexts, including the Conflux Festival, SIGGRAPH, LACMA, the Japan Media Arts Festival, the File Festival, the WIRED Store, and probably to you without you knowing it at some point while interacting with her.
Related Links:
fabric | rblg
This blog is the survey website of fabric | ch - studio for architecture, interaction and research.
We curate and reblog articles, researches, writings, exhibitions and projects that we notice and find interesting during our everyday practice and readings.
Most articles concern the intertwined fields of architecture, territory, art, interaction design, thinking and science. From time to time, we also publish documentation about our own work and research, immersed among these related resources and inspirations.
This website is used by fabric | ch as archive, references and resources. It is shared with all those interested in the same topics as we are, in the hope that they will also find valuable references and content in it.
Quicksearch
Categories
Calendar
|
|
April '24 | |||||
| Mon | Tue | Wed | Thu | Fri | Sat | Sun |
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 | |||||