Tuesday, February 02. 2010
Microsofts Tag Links the Physical World To the Internet
 Paper publications have a problem: they want to link to the Internet, but in order to reach the destination, the reader must type the link into his browser manually, which is slow and awkward.
Paper publications have a problem: they want to link to the Internet, but in order to reach the destination, the reader must type the link into his browser manually, which is slow and awkward.
Microsoft now offers a solution, called Tag. It’s essentially a barcode – an optical machine-readable representation of data – and it lets paper magazines create visual links to content which can be “opened” simply by pointing your smartphone’s camera at them. In today’s world of iPhones, iPads, Nexus Ones and other smart mobile gadgetry, this actually makes more sense than forcing the reader/user to type in a link, no matter how short.
Of course, the possible uses of Tag go far beyond paper magazines; you can put a tag almost anywhere: on a wall, a product, or a giant outdoor sign.
To be able to “read” tags with your phone, you need to download a piece of software; luckily enough, Microsoft has supported most modern smartphone operating systems, including several varieties of Symbian, the iPhone OS, Android, BlackBerry and others.
Check out CNET’s video about Tag below.
Personal comment:
Nothing new at all as this type of tag is existing for years now (see previous post about it or this link from a previous blog and research project ), but MIcrosoft is now entering the business too.
Monday, January 11. 2010
Charting the Real-Time Web
Now social media has the equivalent of the Times Square "deficit clock."
Today the Web is bursting with social media content and a burgeoning supply of (and demand for) "real-time" information. This information is created as people open new Facebook and other social media accounts, churn out Tweets and other microblogs, post photos and videos, and tirelessly text one another. But getting a grip on exactly how much is happening--and what the primary sources are--is a slippery task, especially since web companies often jealously guard their metrics.
The new social media counter. Credit: Gary Hayes.
Now there's a social-media "clock" of sorts, which you can check out here. It charts the second-by-second accumulation of social-media accounts, blogs, Tweets, photo uploadings, status updates, and the like. Consider it the social-media equivalent of that national-deficit "clock" in Times Square.
The effort does require a reality check. It's not actually an accurate rendering of the real-time Web. Rather, it's a counter, created by an Australia-based virtual-world entepreneur named Gary Hayes. Hayes set the various rates of increase according to various estimates culled from disparate sources such as analysts, company blogs, and news media accounts. Some of the estimates are several months old and may not actually be accurate or complete.
But, while it may not provide any new primary information, or be accurate in all categories, Hayes' social-media clock is nevertheless an excellent visualization of where much of the Web's growth is coming from these days.
Via Technology Review (David Talbot)
***
The social web has exploded in the last year and below are some of the key data points that the ‘Gary’s Social Media Count’ is based on :
- 20 hours of video uploaded every minute onto YouTube (source YouTube blog Aug 09)
- Facebook 600k new members per day, and photos, videos per month, 700mill & 4 mill respectively (source Inside Facebook Feb 09)
- Twitter 18 million new users per year & 4 million tweets sent daily (source TechCrunch Apr 09)
- iPolicy UK – SMS messaging has a bright future (Aug 09)
- 900 000 blogs posts put up every day (source Technorati State of the Blogosphere 2008)
- YouTube daily, 96 million videos watched, $1mill bandwidth costs (source Comscore Jul 06 !)
- UPDATE: YouTube 1Billion watched per day SMH (2009)- counter updated!
- Second Life 250k virtual goods made daily, text messages 1250 per second (source Linden Lab release Sep 09)
- Money – $5.5 billion on virtual goods (casual & game worlds) even Facebooks gifts make $70 million annually (source Viximo Aug 09)
- Flickr has 73 million visitors a month who upload 700 million photos (source Yahoo Mar 09)
- Mobile social network subscribers – 92.5 million at the end of 2008, by end of 2013 rising to between 641.6-873.1 million or 132 mill annually (source Informa PDF)
- SMS – Over 2.3 trillion messages will be sent across major markets worldwide in 2008 (source Everysingleoneofus sms statistics)
Friday, December 04. 2009
The Next Phase of Googles Internet: Google Public DNS
Remember that rumor a while back that Google was going to build its own version of the Internet? It turns out that the idea might not be so far-fetched after all.
 Last month, Google revealed that it was working on its own protocol that could perhaps one day replace HTTP, dubbed SPDY. Today, Google announced that it’s going after another fundamental piece of the Internet: DNS.
Last month, Google revealed that it was working on its own protocol that could perhaps one day replace HTTP, dubbed SPDY. Today, Google announced that it’s going after another fundamental piece of the Internet: DNS.
Google has launched what they’re calling Google Public DNS. Here’s how and why Google says they’re attacking the issue:
“You could think of it as the switchboard of the Internet, converting easy-to-remember domain names — e.g., www.google.com — into the unique Internet Protocol (IP) numbers — e.g., 74.125.45.100 — that computers use to communicate with one another.
Our research has shown that speed matters to Internet users, so over the past several months our engineers have been working to make improvements to our public DNS resolver to make users’ web-surfing experiences faster, safer and more reliable.
As people begin to use Google Public DNS, we plan to share what we learn with the broader web community and other DNS providers, to improve the browsing experience for Internet users globally. The goal of Google Public DNS is to benefit users worldwide while also helping the tens of thousands of DNS resolvers improve their services, ultimately making the web faster for everyone.”
While “speed” might indeed be the end result for users, the data could be immensely valuable to Google as a company that is increasingly all about gathering more and more information from multiple channels in order to serve better advertising. Here’s what Google does have to say about the new DNS service and data collection:
“In the permanent logs, we don’t keep personally identifiable information or IP information. We do keep some location information (at the city/metro level) so that we can conduct debugging, analyze abuse phenomena and improve the Google Public DNS prefetching feature. We don’t correlate or combine your information from these logs with any other log data that Google might have about your use of other services, such as data from Web Search and data from advertising on the Google content network. After keeping this data for two weeks, we randomly sample a small subset for permanent storage.”
If you want to try Google DNS for yourself, there’s already a site that will tell you how to do it, complete with toll-free telephone support.
Like many Google projects, this one will likely take many months if not years to gain traction with users, but nonetheless, it’s going to be yet another interesting piece of the Google puzzle to keep an eye on.
-----
Via Mashable
Personal comment:
Quite worrying I think...
Tuesday, September 29. 2009
Idaho: The Unlikely Spam Capital
 Ever wondered which US state receives the most spam? According to Symantec’s MessageLabs, it’s Idaho, where 93.8 percent of all email is spam, followed by Kentucky, New Jersey, Alabama, Illinois, Indiana, Massachussetts, Pennsylvania, Arizona and Maryland.
Ever wondered which US state receives the most spam? According to Symantec’s MessageLabs, it’s Idaho, where 93.8 percent of all email is spam, followed by Kentucky, New Jersey, Alabama, Illinois, Indiana, Massachussetts, Pennsylvania, Arizona and Maryland.
Don’t get us wrong, there’s spam everywhere; the global spam rate for September 2009 is 86.4 percent. But Idaho’s eerily high rate is also a surprise because it jumped 43 spots since 2008; back then it was ranked the 44th most spammed state. We can only guess as to whether spammers have developed some special relationship with Idaho, or it’s all pure coincidence.
If spam drives you mad, the best US state to be living in is the US territory of Puerto Rico, with (just?) 83.1 percent of spam, followed by Montana, Alaska, Kansas, South Dakota, Tennessee, Vermont, Rhode Island, Wisconsin and Florida.
As far as the global spam numbers go, they’re flabbergasting as usual. Four to six million computers accross the globe are parts of botnets that spew out some 151 billion emails a day. Remind me again, why do we still use email?
-----
Via Mashable
Personal comment:
Facts & figures... Affligeant de constater que de façon globale, la moyenne du spam est de 86.4% et curieux de constater que le spam n'affecte pas de façon égale les différentes régions.
Friday, July 10. 2009
Hadopi : Où sarrêtera la surveillance ?
Les agents assermentés de l’Hadopi pourront-ils accuser deux internautes pour avoir échangé, via mail, un fichier protégé par le droit d’auteur ? Et donc pourront-ils surveiller ce type d’échange ? La question est d’importance, et soulève les limites du contrôle et de la surveillance des communications sur Internet par la haute autorité administrative, ceci à la demande des ayants-droit.
Lors de la publication du projet de loi relatif « à la protection pénale de la propriété littéraire et artistique sur Internet », on soulignait que l’article 3 prévoit de punir les infractions de contrefaçon commises « au moyen d’un service de communication au public en ligne ou de communications électroniques ». Or dans le Code des postes et communications électroniques, les « communications électroniques » sont décrites comme « les émissions, transmissions ou réceptions de signes, de signaux, d’écrits, d’images ou de sons, par voie électromagnétique ». En clair, cela peut concerner des échanges par mail, mais aussi par Skype ou MSN.
Cette idée a déjà avancée par l’UMP Franck Riester dans le projet de loi Création et Internet. Mais, finalement Christine Albanel et Riester lui-même avaient donné un avis favorable aux amendements demandant sa suppression. Mais comme une mauvaise télénovela, la série Hadopi se répéte, l’idée est réapparue dans le nouveau texte adopté hier au Sénat. Et les sénateurs communistes de déposer un amendement, le 17, pour demander sa suppression, estimant que « cette disposition constitue une atteinte à la vie privée ».
La sénatrice Brigitte Gonthier-Maurin (PC) a expliqué « que dans la mesure où les échanges de mails ont le statut de correspondance privée, comme la jurisprudence l’a établi, cet élargissement constitue une atteinte à la vie privée, atteinte interdite par l’article 9 du code civil français et l’article 12 de la Déclaration universelle des droits de l’homme de 1948 ». Le sénateur UMP Michel Thiollière, faisant référence à la loi Davdsi, a répondu que « dans sa décision du 27 juillet 2006, le Conseil constitutionnel a considéré qu’il ne pouvait y avoir de rupture d’égalité injustifiée entre les auteurs d’atteintes à la propriété intellectuelle selon que ces atteintes seraient commises au moyen d’un logiciel de pair à pair ou un autre moyen de communication en ligne. ». En clair, que selon cette décision il serait contraire au principe d’égalité qu’un échange via les réseaux p2p soit sanctionné par une (simple) contravention, alors que les autres supports relèveraient eux du délit de contrefaçon.
Le débat reprendra d’ici dix jours à l’Assemblée nationale. Ce matin, le député UMP Lionel Tardy a en effet annoncé qu’il déposera un amendement visant à son tour à faire supprimer l’expression de « communication électronique ». L’exposé des motifs de l’amendement, rapporté par PC Inpact, explique : « Ce texte vise les violations du droit d’auteur opérées par le biais des services de communications électroniques, c’est-à-dire par la messagerie. Cela implique, pour les détecter, d’ouvrir des correspondances privées, ce qui serait assurément inconstitutionnel. » Face à Lionel Tardy, ce matin, sur BFM, le rapporteur Franck Riester a répliqué que le téléchargement illégal ne se pratiquant pas uniquement par p2p : « on doit regarder sur Internet toutes ces techniques-là ».
-----
Via Libération
Personal comment:
Dans le cadre du projet Globale Surveillance, intéressant de suivre le feuilleton de l'élaboration de la loi Hadopi en France. Evidemment, il est difficile de "surveiller" sans atteindre aux libertés individuelles...
Monday, June 22. 2009
The Tree Museum
Note: This is a guest post by Nicola Twilley.
Every tree is a living archive, its rings a record of rainfall, temperature, atmosphere, fire, volcanic eruption, and even solar activity. These arboreal archives together reach back in time over centuries, sometimes millennia. We can even map human history through them—and onto them—tracing famines, plagues, and the passing of our own lives.
 [Image: A scene from Alfred Hitchcock's film Vertigo, with Jimmy Stewart and Kim Novak in Muir Woods, outside San Francisco, where Novak points to the concentric rings of the redwood trunk and says, "Here I was born... and here I died"].
[Image: A scene from Alfred Hitchcock's film Vertigo, with Jimmy Stewart and Kim Novak in Muir Woods, outside San Francisco, where Novak points to the concentric rings of the redwood trunk and says, "Here I was born... and here I died"].
For artist Katie Holten, trees were thus the natural starting point for an oral history of a city street in the Bronx. To mark the 100th anniversary of the Grand Concourse, a four-mile-long boulevard that connects Manhattan to the parks of the Northern Bronx, Holten has created the Tree Museum: 100 specially-chosen trees between 138th Street and Mosholu Parkway, each of which has a story to tell if you dial the number at its base.
The museum opens today, June 21, with a parade and street fair: for those of us not in New York, a podcast and brochure will be available for download, and you also can view each of the tree locations on Google Maps.
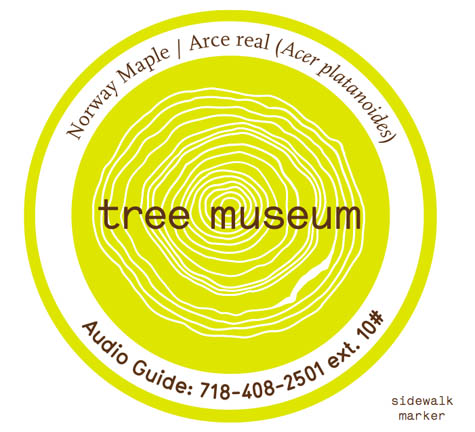 [Image: Trees in the museum each have their own sidewalk marker, which gives their name and extension number].
[Image: Trees in the museum each have their own sidewalk marker, which gives their name and extension number].
Only a handful of the one hundred "story-trees" date from the Concourse's construction, when an avenue of Norwegian maples was planted to shade carriages and pedestrians strolling along the broad boulevard. In an email conversation, Holten explained to BLDGBLOG that most of these original trees were moved to Pelham Bay Park when the B/D subway line was built in the early '30s. Twelve of the surviving maples are joined in the Tree Museum by representatives of fifty-nine other tree species, from an Amur Corktree in Joyce Kilmer park to a Kentucky Coffeetree just south of Tremont Avenue.
In fact, each tree is carefully identified by its species name, in Spanish, English, and Latin, to draw museum visitors' attention to their variety. Holten told me that, early on in her community outreach, she realized how important naming the trees would be when a teacher in a local school confessed, incredibly, that it was only after he heard about the Tree Museum idea that "he noticed the next time he was walking that there were different kinds of trees. Before that he'd thought they were just 'trees'."
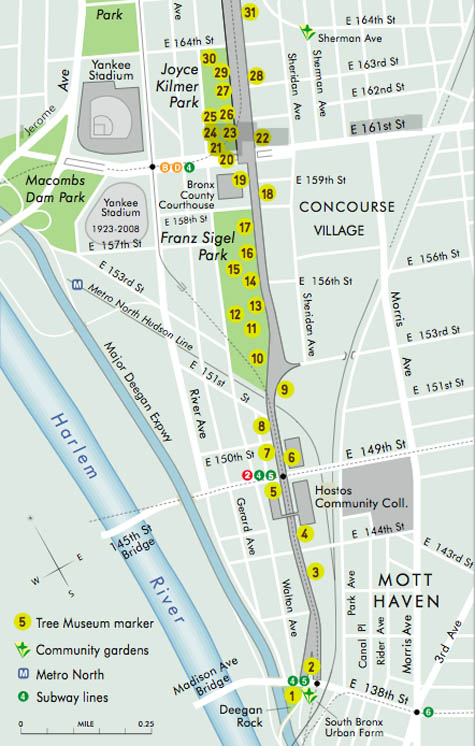 [Image: A section of the Tree Museum map; a much larger version can be seen here].
[Image: A section of the Tree Museum map; a much larger version can be seen here].
The trees were chosen for their variety, Holten says, but also for "location, age, and connection to a particular person or story." Holten acted as matchmaker, pairing trees with former and current Bronx residents, as well as scientists, authors, and activists who have worked in the area. Among the 100 participants are well-known former Bronxites DJ Jazzy Jay and Daniel Libeskind, students at the Bronx Writing Academy, and Jonathan Pywell, Bronx Senior Forester, who helped Holten identify all the trees (not an easy task in mid-winter). Each has used their tree as the starting point for a personal anecdote, snippet of neighborhood history, song, or even a digital sound recording.
Taken together, the tree stories are part shared history, part personal memory, part science lesson—they form what Holten describes as "the whole ecosystem of the street."
 [Image: A computer-generated image of Klaus Lackner's prototype "synthetic tree," which would remove carbon dioxide directly from the air; image courtesy of Columbia University].
[Image: A computer-generated image of Klaus Lackner's prototype "synthetic tree," which would remove carbon dioxide directly from the air; image courtesy of Columbia University].
In her email, Holten went into some detail describing the range of stories you can hear as you dial each tree's extension, from the sound of a Puerto Rican tree frog (No.73, a Gingko) to a local preservationist describing how he fought to turn an abandoned lot into the park that now surrounds No. 100, a Cottonwood. From her email:
- Klaus Lackner (professor in the Department of Earth and Environmental Engineering at Columbia University and director of the Lenfest Center for Sustainable Energy) tells the story of the carbon cycle and his attempt to create a "fake plastic tree," or air extractor, that would suck the CO2 out of the air and convert it into something we can put in a safe place. Eric Sanderson (a landscape ecologist based at the Bronx Zoo, and author of Mannahatta) needed a really old, native tree to talk about projecting the landscape backwards. I gave him No. 9, a beautiful American Elm outside Cardinal Hayes High School.
At the northern end of the Concourse, at 206th St, there's a huge chunk of rock between two buildings; it's like the side of a cliff. I had to give the tree there, No. 95, to Sid Horenstein, a geologist who recently retired from the American Museum of Natural History. He's able to use the rock outcrop to explain the story of what the Concourse lies above—it was built on a ridge and that's one of the main reasons the street was constructed here, because it was elevated and offered spectacular views of the countryside all around.
And Tree No. 45, a Little Leaf Linden, has a story told by Patricia Foody, a 95-year-old Bronxite. She remembers her dad bringing her for a walk to the Concourse to visit his brother's tree in just this location—it was one of the original maples, and many of them had plaques for soldiers who had died in World War I.
Some of the stories come from people who work with the trees directly: Jennifer Greenfeld, director of Street Tree Planting for the Parks and Recreation department, uses No. 66, a Chinese Elm, to provide an overview of street trees throughout New York City and the policy battles they sometimes cause. Barbara Barnes, a landscape architect also with the Parks department, puts her tree in the context of the historic street tree canopy project she's working on, to replant Joyce Kilmer and Franz Sigel parks as they were originally laid out.
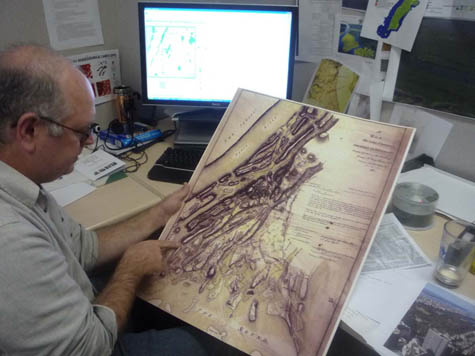 [Image: Eric Sanderson pointing at a map of the Bronx; photo by Katie Holten].
[Image: Eric Sanderson pointing at a map of the Bronx; photo by Katie Holten].
For other participants, the trees function as more of a backdrop for personal history and community activism. Sabrina Cardenales is the real-life model for the character Mercedes in Adrian Nicole LeBlanc's Random Family: Love, Drugs, Trouble, and Coming of Age in the Bronx, which documents extreme urban poverty in New York: both Sabrina and Adrian introduce themselves and read a passage from the book as part of the Tree Museum. Meanwhile, Majora Carter, an environmental justice activist and MacArthur fellow from the south Bronx, uses tree No. 6, a honey locust, to tell people: "You don't have to leave your neighborhood to live in a better one, and trees are an important part of making that happen."
The variety of voices and stories Holten describes accumulate into a sense that plenty of people really do care about these trees, this street, and the Bronx in general. They also act as a series of nudges to look at the urban landscape in a new light. The result is that the Tree Museum, at least in theory, will recreate some of the optimism of the Grand Concourse's roots in the City Beautiful movement, while not glossing over the struggles and setbacks faced by the "Champs-Élysées of the Bronx" ever since.
 [Image: The Bronx Grand Concourse, looking north from 161st Street; photo by Katie Holten].
[Image: The Bronx Grand Concourse, looking north from 161st Street; photo by Katie Holten].
As part of the Concourse's centenary celebrations, the Bronx Museum and New York's Design Trust For Public Space are running a competition called Intersections: Grand Concourse Beyond 100, to gather new proposals for regenerating the street. Although the call for entries period is now closed, Katie Holten has set up a community forum for the Tree Museum, and clearly hopes the project will prompt action, as well as reflection.
Holten explains her most basic hope, which is that the Museum will encourage people to start using and enjoying their shared public space again:
- One hundred years ago the Concourse was built for people to stroll along, under the shade of the trees, but in 2009 it takes quite an effort to get people out for a walk—hopefully we’ll get them strolling! There are a number of individuals who I met because they are interested in trees, or in "green" issues, and we've tried to use the momentum of the Tree Museum to help them make differences. For example, Fernando Tirado (tree No. 88) is district manager for Bronx Community Board #7 and he's been prompted to establish a "Greening the Concourse" project. He's organizing summer internships for youth in the area: giving them a job and training, and at the same time actually greening the street.
Perhaps more importantly, Holten's Tree Museum (which she describes as "practically invisible—it's part of the urban fabric") demonstrates an intriguing way to re-imagine the landscape: finding ways to make the hidden layers and connections of a street's story visible (or audible) might ultimately be as, if not more, important than installing a new swing set in the park.
-----
Via BLDBLOG
Personal comment:
Les arbres comme "disque dur" et "capteurs" d'information climatiques. Un des partcipants pour le concours "Climate Clock - San Jose" s'était servi d'arbres en tant que "capteurs durables" (l'installation devant servir une centaine d'années). S'était une approche intéressante. Ici, le mélnage de télécommunications (appeler les arbres), de développement durable, de monitoring et de narration (une histoire par arbre) est également une approche suprenante et intéressante.
Dans un même ordre d'idée, on sait que la glace (on voulait en utiliser pour un projet) et les dépots de neige aux pôles constituent la même source d'information. Beaucoup plus vielle pour les carottes de glace tirées de l'Antarctique par exemple et qui donnent peut-être encore d'autres éléments (bulles d'air prisonnières, etc.)
Thursday, June 18. 2009
The Web vs. the Republic of Iran
 |
| Tweet: Mousavi1388's Twitter feed allows the opposition party to share information. Credit: Technology Review |
Attempts to censor the press have increased significantly since last Friday's disputed election. Yesterday, press credentials for foreign journalists were revoked, and many were told via phone and fax not to report from the streets. Other journalists have been injured, detained, or arrested by the authorities.
Yet despite the media crackdown, information continues to leak out of Iran via social networking, microblogging, and photo- and video-hosting websites. These resources have been used before to organize during political crises--in Georgia and Russia, Burma and Kenya--but the sheer scale and scope are striking in Iran's case.
Ethan Zuckerman, of the Berkman Center for Internet and Society, at Harvard University, and cofounder of the blogger advocacy group Global Voices, says that people inside Iran who are blogging, Tweeting, and sharing photos are "doing an amazing job of making this political movement visible to the world." Photo and video sharing, in particular, have brought the situation home to foreign observers and have made it "much more real, and much more real time," Zuckerman says.
Zuckerman attributes the continued information flow in part to "latent capability": savvy Internet users in Iran already know how to circumvent blocking measures, so in a political upheaval they don't have to relearn the process. "The longer a country censors and the more aggressively it censors," says Zuckerman, "the more incentive it gives citizens to learn how to get around that." Because Iran has been filtering since at least 2004, says Zuckerman, a lot of Iranians already know how to use proxies--computers that route traffic around a government-imposed block. So even if you're just using a proxy to surf porn, says Zuckerman, suddenly, a political crisis hits and you already have the means to communicate.
Normally, Iran's government maintains a tight grip on Internet use. Because Iran is economically ostracized, the government doesn't have many business relationships that it can leverage to prompt censorship from the outside--unlike China, for example, which runs a censored version of Google (and its ads) through its state-controlled filters. But communications from Iranian ISPs serving the public, rather than academic institutions or private businesses, are all routed through the state-controlled Telecommunication Company of Iran (TCI), allowing for easy filtering. Blogs and websites dedicated to anti-Islamic and anti-government content are routinely blocked. Facebook was blocked sporadically in the months leading up to Friday's election and during the election itself, as were websites for the major opposition candidates and several pro-reform sites. Facebook and YouTube are still blocked in response to the post-election protests.
Having reportedly purchased an electronic surveillance system for Internet monitoring in 2008, the Iranian government is well equipped to handle tracking and recording through its centralized system. According to a just-released report from the Open Net Initiative (ONI)--a project involving researchers from Harvard University, the University of Toronto, the University of Cambridge, and the University of Oxford--this has already occurred with women's-rights activists who were arrested and reportedly shown transcripts of their IM sessions.
In the past, the Iranian government has used the U.S. product SmartFilter to block offensive websites, but the ONI reports that it now has a homegrown system for searching the Internet for objectionable content and keywords. This makes Iran and China the only two countries that "aggressively filter" Internet content using their own technology.
Faced with similar unrest, other governments have pulled the plug on Internet communications entirely. Iran's authorities appear to have chosen to begin "bandwidth throttling" instead. By limiting the amount of information that gets through every second, the government can effectively slow down the Internet so that the average Internet user has to wait several minutes to add a post to Twitter or upload an image to Flickr. With reduced bandwidth, Zuckerman says, "it's harder to access Internet content from the outside, and it's really hard to upload content."
Some analysts suggest it is unlikely that Iran's Internet connectivity would ever be turned off completely. "It's one thing to anger a group of protesting rioters," says Hal Roberts, also of Harvard's Berkman Center. "It's another to hurt the whole population" by shutting off Internet connection. With around 23 million Internet users in Iran, or about 35 percent of the population, Iran has far more Internet users than its Middle Eastern neighbors.
Andrew Lewman, a member of the team behind Tor--software that routes Internet traffic around government filters anonymously--says that he's surprised by how little the Iranian government has blocked the Internet in recent days, given the attention that the current political unrest has received. He attributes the continuing flow of information out of Iran to two possibilities: either there are people in the government who want to see it disseminated, or the government is tracking and recording everything that's happened in order to round up the perpetrators later. The government's main focus right now, Lewman says, is most likely dealing with the actual protestors on the streets.
Rob Faris, who contributed to the ONI report, is less optimistic about communication flow in Iran. The government has "ramped up filtering in a big way," he says. Even though Twitter remains accessible--through third party apps that don't access Twitter.com for example--"let's not kid ourselves," Faris says. "Access to Twitter, without all the other things you can do with the web, isn't a good deal." Meanwhile, the other measures Iran has taken have "significantly impacted" the communications infrastructure. "They've gone from a repressive regime to a more repressive regime," Faris says.
Still Roberts believes that the Iranian government will likely crack down on the rioters first, and deal with the bloggers later. He suggests that government agencies may be tracking users via their Internet protocol addresses and planning to follow up with arrests.
The most difficult question regarding the Web's involvement in the current situation, Zuckerman says, is to what extent these tools are helping to organize actual protests. "This is a legitimate street protest; people are extremely upset about their voting rights," he says. Zuckerman senses that the technology isn't helping opposition supporters as much as are traditional organizing methods like phone calls and word of mouth.
According to Stephen Murdoch, a computer security researcher at the University of Cambridge, it's hard to tell how many people are actually involved with Web-based protests inside Iran because what we see outside the country is a "biased" sample. Twitter and Facebook are popular in the United States, but there are likely other social-networking sites geared toward Iranians that we can't monitor as closely. So the extent--and reach--of Web activity in Iran is hard to judge.
But the effect on the global community is clear, Roberts says: "The press is driven by [Iran's] Twitter stream."
Copyright Technology Review 2009.
-----
fabric | rblg
This blog is the survey website of fabric | ch - studio for architecture, interaction and research.
We curate and reblog articles, researches, writings, exhibitions and projects that we notice and find interesting during our everyday practice and readings.
Most articles concern the intertwined fields of architecture, territory, art, interaction design, thinking and science. From time to time, we also publish documentation about our own work and research, immersed among these related resources and inspirations.
This website is used by fabric | ch as archive, references and resources. It is shared with all those interested in the same topics as we are, in the hope that they will also find valuable references and content in it.
Quicksearch
Categories
Calendar
|
|
May '24 | |||||
| Mon | Tue | Wed | Thu | Fri | Sat | Sun |
| 1 | 2 | 3 | 4 | 5 | ||
| 6 | 7 | 8 | 9 | 10 | 11 | 12 |
| 13 | 14 | 15 | 16 | 17 | 18 | 19 |
| 20 | 21 | 22 | 23 | 24 | 25 | 26 |
| 27 | 28 | 29 | 30 | 31 | ||
