Tuesday, November 04. 2008
Epoq Sugar Cube EPP-HH01 claims World's smallest Video Projector

Epoq unveils the EPP-HH01 Pico Sugar Cube projector, claiming that it is the world's smallest video projector. The Pico Sugar Cube measures 39.6x56.7x57.5 mm, which makes it indeed very small. We have seen smaller Pico Projector prototypes though at the CES 2008. If the EPP-HH01 Pico Sugar Cube is really shipping this month than it is most likely the smallest projector you can buy right now.
Specifications of the Epoq Sugar Cube EPP-HH01 include VGA resolution, 7-10 ANSI Lumen Brightness, 80:1 Contrast Ratio, 3W Cree TM high power LED light source, and 25,000 hours lamp life time.
These specifications are of course very underwhelming, but it makes for a fun geek joke to appear at a business meeting with this tiny projector.
The bigger trend is though to have projection feature integrated in mobile phones.
The GadgetCraver store sells the Epoq EPP-HH01 for $229.95.

Related Links:
Monday, November 03. 2008
Microsoft Adds SecondLight to its 'Surface'
Over the past couple of years, gadgets have become much more touchy-feely. Apple's iPhone and Microsoft's Surface (an interactive table) are two of the most celebrated examples. Now, Microsoft has added a twist to Surface that makes for an impressive demo.
Microsoft announced the upgrade to Surface, called SecondLight, at the company's Professional Developers Conference in Los Angeles on Wednesday. . As the video above demonstrates, in this new version of Surface, a secondary image is projected above the main display. A person views the second image by holding a semi-opaque object, such as a piece of paper above the display. The idea is to provide a second layer of information: labeled constellations on top of photographs of stars or street names on top of maps, for instance.
SecondLight uses a neat trick to produce this second layer. The original Surface used a projector below a glass tabletop to create an image and infrared cameras underneath to detect fingers and objects in contact with the surface. With SecondLight, Microsoft has replaced the glass top with a liquid crystal display (LCD), but kept the projector underneath. The LCD flickers on an off and, during alternate frames the projector sends the secondary image through the display. This happens too fast for your eyes to catch it unless you hold up an opaque object, like a piece of paper.
The Bullet Ultra-Tiny Wi-Fi Router Works with Any Antenna
Talk about a great way to fill dead spots in your wireless network coverage: The Bullet, from Ubiquiti Networks, is a bullet-size (okay, shotgun shell-size) router that plugs into a network on one end and an external, omni-directional antenna on the other. Point it where you want, and you've got instant 802.11a/b/g broadcasting.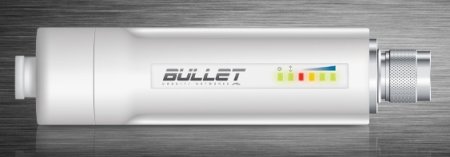
It's not going to work on just any network. The 10/100 Ethernet port requires Power over Ethernet (PoE) to get juice, and PoE is something you'll typically find on a corporate network. The other end of the Bullet has an N-Type Connector for antennas, complete with a custom gasket to keep out water. Inside is an Atheros chip, 16MB of RAM, and 4MB of Flash memory to hold the AirOS software that runs it (AirOS is Ubiquiti's own, but open source). With it, you get the full complement of typical router features.
Once it's plugged into PoE, the Bullet's output power goes as high as 1000mW. Coupled with the right kind of antenna, it's going to blast through a lot of walls to give you a nice range. That's pretty good, since the Bullet itself is only $39, but not surprising since Ubiquiti equipment was used last year to set the Wi-Fi distance record of 188.9 miles (350 KM) from the island of Sardinia to the summit of Monte Amita in mainland Italy.
Related Links:
Keys Can be Copied From Afar, Jacobs School Computer Scientists Show
San Diego, CA, October 30, 2008--UC San Diego computer scientists have built a software program that can perform key duplication without having the key. Instead, the computer scientists only need a photograph of the key.
“We built our key duplication software system to show people that their keys are not inherently secret,” said Stefan Savage, the computer science professor from UC San Diego’s Jacobs School of Engineering who led the student-run project. “Perhaps this was once a reasonable assumption, but advances in digital imaging and optics have made it easy to duplicate someone’s keys from a distance without them even noticing.”
Professor Savage presents this work on October 30 at ACM’s Conference on Communications and Computer Security (CCS) 2008, one of the premier academic computer security conferences.
 |
|
Scenes from one of the proof-of-concept telephoto experiments. The computer scientists successfully decoded this key image, captured at a distance of 195 feet. |
The bumps and valleys on your house or office keys represent a numeric code that completely describes how to open your particular lock. If a key doesn’t encode this precise “bitting code,” then it won’t open your door.
In one demonstration of the new software system, the computer scientists took pictures of common residential house keys with a cell phone camera, fed the image into their software which then produced the information needed to create identical copies. In another example, they used a five inch telephoto lens to capture images from the roof of a campus building and duplicate keys sitting on a café table about 200 feet away.
“This idea should come as little surprise to locksmiths or lock vendors,” said Savage. “There are experts who have been able to copy keys by hand from high-resolution photographs for some time. However, we argue that the threat has turned a corner—cheap image sensors have made digital cameras pervasive and basic computer vision techniques can automatically extract a key’s information without requiring any expertise.”
Professor Savage notes, however, that the idea that one’s keys are sensitive visual information is not widely appreciated in the general public.
“If you go onto a photo-sharing site such as Flickr, you will find many photos of people’s keys that can be used to easily make duplicates. While people generally blur out the numbers on their credit cards and driver's licenses before putting those photos on-line, they don’t realize that they should take the same precautions with their keys,” said Savage.
As for what to do about the key duplication threat, Savage says that companies are actively developing and marketing new locking systems that encode electromagnetic secrets as well as a physical code. “Many car keys, for example, have RFID immobilizer chips that prevent duplicated keys from turning the car on,” he says. In the meantime, he suggests that you treat your keys like you treat your credit card and “keep it in your pocket unless you need to use it.”
How it works
The keys used in the most common residential locks in the United States have a series of 5 or 6 cuts, spaced out at regular intervals. The computer scientists created a program in MatLab that can process photos of keys from nearly any angle and measure the depth of each cut. String together the depth of each cut and you have a key’s bitting code, which together with basic information on the brand and type of key you have, is what you need to make a duplicate key.
The chief challenge for the software system, called “Sneakey,” is to adjust for a wide range of different angles and distances between the camera and the key being captured. To do so, the researchers relied on a classic computer vision technique for normalizing an object’s orientation and size in three dimensions by matching control points from a reference image to equivalent points in the target image.
“The program is simple. You only need to click a few control points in the image of the key and the ‘Sneakey’ program does the rest. It normalizes the key’s size and position so that each pixel then corresponds to a known distance. From this information, the height of each of the key cuts can easily be computed and likewise the bitting code can be extracted,” explained Benjamin Laxton, the first author on the paper who wrote the Sneakey program and recently earned his Master’s degree in computer science from UC San Diego.
The researchers have not released their code to the public, but they acknowledge that it would not be terribly difficult for someone with basic knowledge of MatLab and computer vision techniques to build a similar system.
“Technology trends in computer vision are at a point where we need to consider new risks for physical security systems,” said Kai Wang, a UC San Diego computer science graduate student and author on the new paper. Wang is a computer vision researcher working on the creating systems capable of reading text on product packaging. This is part of a larger project on creating a computerized personal shopping assistant for the visually impaired from the lab of computer science professor Serge Belongie.
As a computer security expert, Savage said he particularly enjoyed working on a project with computer vision students.
“UC San Diego is very supportive of interdisciplinary work. There are many opportunities for students and faculty to get their hands dirty in fields they may not know much about a lot at first,” said Savage.
Paper citation:
“Reconsidering Physical Key Secrecy: Teleduplication via Optical Decoding ,” by Benjamin Laxton, Kai Wang, and Stefan Savage from the Department of Computer Science and Engineering at UC San Diego’s Jacobs School of Engineering.
ACM CCS 2008, Alexandria, VA, October 2008.
Related Links:
Thursday, October 30. 2008
Translucent OLED Panels can use as panes of Window Glass
You wouldn’t find these windows at your local Home Depot Window and Sliding department; it’s made of a translucent OLED panel by the Korean Electronics Giant, Samsung. The company has showcased a prototype of four 12.1-inch OLED panels as a window display at FPD International 2008; it’s also its first exhibition of OLED panel with a transmittance of 30 percent at Japan.

Back side of the window

Each panel has a resolution of 840×504 and is capable of 200cd/m2 luminance, extremely fast 0.01 ms panel response rate, and can achieve 100% coverage of NTSC color gamut.
Nikkei said the manufacturer has declined to disclose the technicality behind the four panes of glass. But like the flapping 0.05mm OLED panel, the drive element was formed by a low temperature polysilicon TFTs and “The device structure is a top emission type, and organic EL materials for RBG colors are separately applied by using a metal mask”.
Wednesday, October 29. 2008
Cloud/Grid computing or Quake-Catcher Network
Distributed computing among volunteers’ laptops is proving effective in detecting earthquakes. The Wired Campus reports the project today, explaining the laptops used are taking advantage of the fact that: “Laptop manufacturers have been adding motion sensors — accelerometers — that protect data by turning off machines’ hard drives in case the machines are dropped.” The homepage of the Quake-Catcher Network invites volunteers and provides downloads of the software required:
The Quake-Catcher Network is a collaborative initiative for developing the world’s largest, low-cost strong-motion seismic network by utilizing sensors in and attached to internet-connected computers.
With your help, the Quake-Catcher Network can provide better understanding of earthquakes, give early warning to schools, emergency response systems, and others. The Quake-Catcher Network also provides educational software designed to help teach about earthquakes and earthquake hazards.
Related Links:
Color E-Paper Debuts
A waterproof MP3 player built for bright beach days is the first device with a color "e-paper" display, meaning it has no backlighting and thus can be read in direct sunlight. The display, from Qualcomm, consists of two layers of a reflective material. Some wavelengths of light bounce off the first layer; some pass through and bounce off the second. Interference between the two beams creates the color, and electrostatic forces control the distance between the layers.
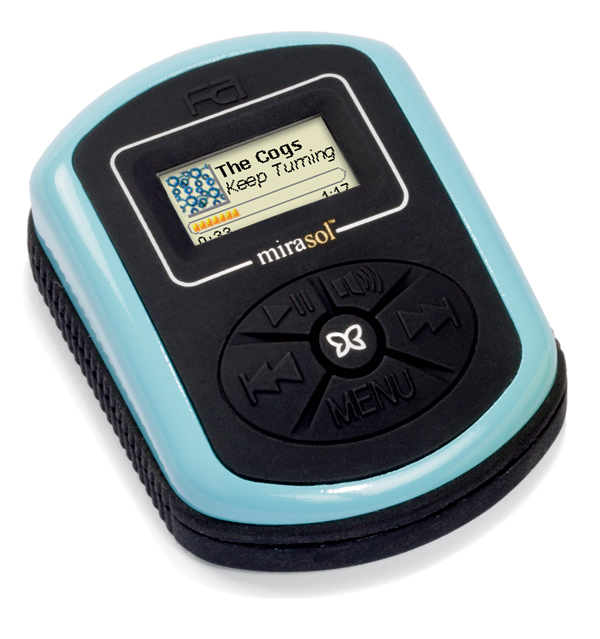
Credit: Courtesy of Qualcomm
Related Links:
Monday, October 27. 2008
Betting on Android (?)

Rich Miner speaking at eComm2008. Credit: James Duncan Davidson
-
There's a lot of talk at Mobile Internet World 2008, in Boston, about how great applications for mobile devices die all the time because it's so hard to get through all the negotiation that stands in the way of real people using the software. A startup often has to work deals with carriers, device manufacturers, and the company that controls a device's operating system before having any hope that people might one day be able to buy or use any software that the company intends to build.
But while insider woes may not matter to the average person, the goals described by Rich Miner, group manager of mobile platforms for Google and one of the visionaries behind the company's open Android platform, could vastly change how large numbers of people access the Internet--if Android succeeds. Google is supporting Android for a long-term reason, Miner said. The company's products are all Web services, and, after having successfully won the hearts and minds of many people using laptops and desktops, one way the company hopes to grow is by convincing more users to access its services through mobile phones. That requires making it possible for them to do so.
Miner described Google's frustrations building a Maps application for mobile phones. Miner said that after having established itself by building on open-source software in most cases--using the Linux operating system, for example--the company was shocked at the closed, serpentine processes typical of building mobile applications. The company wants to change what is now often an expensive, 18-month process into a matter of days and a $25 application fee. The company has successfully pushed industry giants to talk the same talk. Yesterday at the conference, Verizon Wireless director of open development Anthony Lewis spoke about his company's efforts to reduce the application approval process to only four weeks.
If these types of efforts succeed, people will see many more applications available through mobile phones. It will be easier to access Web pages and services familiar from the larger Internet, and devices will stop existing as separate animals. And presumably, Google will continue to rake in money through advertisements as more people access the Internet more often.
The vision that Miner described is in line with other things that I've heard from Google, particularly in relation to App Engine, its quick-start service designed to help Web application developers get going quickly and easily. The idea is that the easier it is for people to build software for the Web, the more reasons people will have to access the Web. The Web will become an ever-larger part of people's lives. In the end, this will be good for Google. In service to this strategy, the company has poured money and effort into shaking up the mobile industry.
Since the first phone running Android software came out this Tuesday, with many more to follow, it's time for users to put Google's strategy to the test. I'm hoping that Android and other open efforts succeed. Google's profit motives aside, the mobile industry is clearly choked and stifled by the wrangling and politics associated with getting new software and hardware on the market. Breaking that block will bring better services to people using mobile devices.
Related Links:
Personal comment:
About how long it gets, and sometimes how impossible, to deliver an application on proprietary mobile phones. Which is why Google has launched Android (according to them, but with the idea in mind to first deliver their products!)
A Better Network for Outer Space
 |
| Networking space: Vint Cerf, cocreator of the Internet and a vice president at Google, is designing protocols for a robust space-communication network, modeled on the terrestrial Internet. Cerf is working with a team at NASA’s Jet Propulsion Laboratory (where he is also a visiting scientist) and at the MITRE Corporation, based in Washington, DC. Credit: Courtesy of Google |
Cerf, who is Google's vice president and chief Internet evangelist, is working with a team at NASA's Jet Propulsion Laboratory (JPL), where he is also a visiting scientist, and at the MITRE Corporation, based in Washington, DC, to design and implement a revolutionary new scheme for space communication. The project, dubbed the Interplanetary Internet, will be tested aboard the International Space Station (ISS) in 2009, and Cerf hopes that by 2010, new space missions will be designed to use the protocols.
Ultimately, the network could interconnect manned and robotic spacecraft, forming the backbone of a communications system that reaches across the solar system.
Technology Review's Brittany Sauser caught up with Cerf to discuss the details of the project.
Technology Review: What's the purpose of the Interplanetary Internet?
Vint Cerf:The project started 10 years ago as an attempt to figure out what kind of technical networking standards would be useful to support interplanetary communication. Bear in mind, we have been flying robotic equipment to the inner and outer planets, asteroids, comets, and such since the 1960s. We have been able to communicate with those robotic devices and with manned missions using point-to-point radio communications. In fact, for many of these missions, we used a dedicated communications system called the Deep Space Network (DSN), built by JPL in 1964.
But one problem with space communication has been the limited use of standards. When we launch a spacecraft with a unique set of sensors onboard, we often end up writing special communication and application software that is adapted to that spacecraft's sensor systems and manipulators. In the Internet world, we use standards called the TCP/IP protocol suite--packet switching and store-and-forward methods--to allow a lot of different devices, billions of things, to interact compatibly with each other. The team set out to develop a suite of protocols that would allow us to have the kind of network flexibility in space that we have on Earth. The Interplanetary Internet project is primarily about developing a set of communication standards and technical specifications to support rich networking in space environments.
TR:What are the challenges of building such a network in space?
VC:We started by working on a set of protocols that could deal with two very important properties of space communication. The first is delay. The distances between the planets are very large. For example, when Earth and Mars are closest together, it still takes 3.5 minutes for a radio signal moving at the speed of light to propagate. If I were on Mars and you were on Earth, it would take seven minutes at best before you heard a response. When Earth and Mars are farthest apart, the round trip takes 40 minutes! The reason we can talk back and forth on Earth so easily is that propagation times are very short by comparison.
The other problem is that the planets and their satellites are in motion, and most are rotating. The rotation of the planets means that if you are talking to something that is on the surface of the planet, it may rotate out of the line of sight so you cannot talk to it anymore, until the device on the surface rotates into view again. The same could be said for some orbiting satellites. You have to develop protocols that will deal with the fact that you cannot always communicate with the other party: the communication is both delayed and potentially disrupted. So that is what we designed: a delay- and disruption-tolerant networking system [DTN]. It will allow us to maintain communications more effectively, getting much more data because we don't have to be in direct line of sight with the ultimate recipient in order to transfer data. The new protocols will be proposed to serve as a potential international standard for space networking.
TR:How does this new protocol, the delay- and disruption-tolerant networking system, work?
VC: We are using store-and-forward methods [routing information through hosts that hold on to it until a communications link can be established] similar to the TCP/IP design in order to service space-communication requirements. But our new bundle protocol is based on DTN principles. We have to cope with the fact that there is a really high potential for delay and disruption in the system. For example, Pluto is a long ways away, on the order of three to five billion miles and about 12 hours round-trip time. Using the DTN bundle protocol allows us to design more-complex mission configurations involving many devices on the surface of planets and in orbit around them. At Mars, for example, there are four orbiters and three landed and operational spacecraft. We expect to be able to use the standard TCP/IP protocols on the surface of planets and inside spacecraft, but we will use the DTN protocols for interplanetary distance communications.
TR: Is this going to require putting new infrastructure in space?
VC: The answer is yes and no. For example, the Deep Impact spacecraft [now called EPOXI] is already in orbit around the sun. It was used to launch a probe into a comet to examine its interior. EPOXI is being temporarily repurposed to test the new DTN protocols. The spacecraft has processing, memory, radio equipment, and solar panels for power so we don't have to put new hardware up. We just have to upload new software. We are lucky to not have to field any new equipment yet, but the DTN protocols eventually have to show up in a fairly significant number of devices in the system to create the kind of network that can serve space-communication needs. Some specialized spacecraft could become store-and-forward routers. Each time a new mission is launched, using the standard bundle protocol, previous mission assets that are still in operation could be used to support the communication requirements of the new mission. In this way, we hope to accrete a kind of interplanetary backbone network.
TR: How are you handling security issues?
VC: There are security concerns, and we have been very careful to build defenses into the basic design. Each bundle-aware node will verify the identity of any other nodes that it is communicating with, and it will refuse to forward data from any nodes that it does not recognize. We will be using strong authentication methods, cryptographic communication methods, to ensure that the parties that are using the resources are authorized to do so.
TR: What is the biggest advantage of building new protocols for space communication?
VC: The important part here is that we have standardized protocols that will allow internetworking of various spacecraft launched by all the spacefaring nations. Over time, as new missions are launched, you start to build up a backbone capability. Every time you put up a new mission, you basically are putting up another potential node in the network. Our hope in the near term is to start putting DTN/bundle-protocol applications up on the Internet terrestrially, and also put them up on the International Space Station for testing. Eventually, we hope to have this capability running all the time, and then, when new deep-space missions are launched using these standard protocols, they will become part of the interplanetary communications system.
Copyright Technology Review 2008.
Related Links:
Tiny spycam hidden in a tradeshow badge secretly shoots video and stills

The Spy Pass Card Micro Camera looks like a standard ID card, but it has a hidden spy camera for all your covert missions.
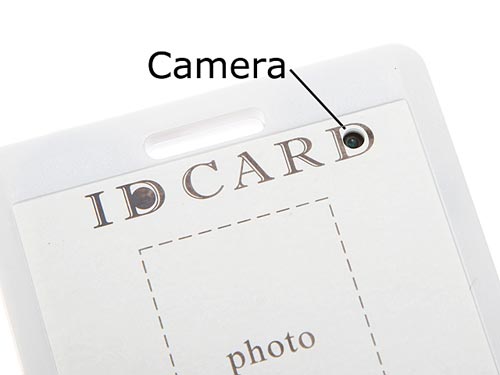
The card measures 8.5 x 5.2 cm and can either bee worn around your neck or clipped to your shirt.
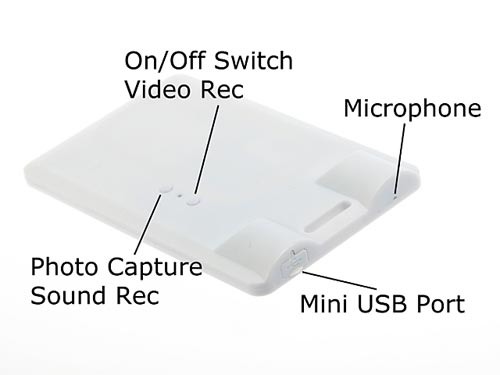
It is capable of recording video at a resolution of 352 x 288 or taking still pictures at a resolution of 1280 x 1024.
Here’s the specs.
- Spy Pass Card Micro Camera
- Come with neckstrap and name card clip
- Card size: 8.5 x 5.2 cm
- Built-in Camera, Rechargeable Battery and 4GB Memory
- Video Resolutions: 352 x 288 pixels
- Video Format: AVI
- Still Photo Resolutions: 1280 x 1024 pixels
- Still Photo Format: JPG
- Audio Format: WAV
- Charging Interface: USB cable via adaptor or computer
Related Links:
fabric | rblg
This blog is the survey website of fabric | ch - studio for architecture, interaction and research.
We curate and reblog articles, researches, writings, exhibitions and projects that we notice and find interesting during our everyday practice and readings.
Most articles concern the intertwined fields of architecture, territory, art, interaction design, thinking and science. From time to time, we also publish documentation about our own work and research, immersed among these related resources and inspirations.
This website is used by fabric | ch as archive, references and resources. It is shared with all those interested in the same topics as we are, in the hope that they will also find valuable references and content in it.
Quicksearch
Categories
Calendar
|
|
April '24 | |||||
| Mon | Tue | Wed | Thu | Fri | Sat | Sun |
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 | |||||
