Thursday, April 21. 2011
Via Libération
-----
par Alexandre Hervaud

Capture Ecrans
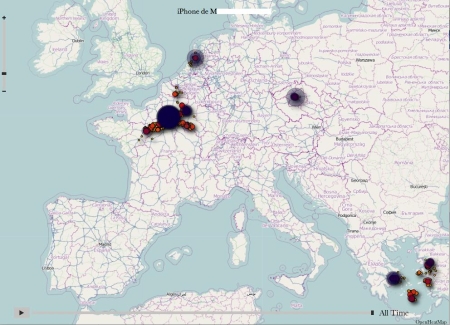
Dire où l’on se trouve en permanence via son smartphone, c’est simple comme bonjour : on peut le déclamer à qui ça intéresse (indice : personne) via les versions mobiles des réseaux sociaux type Facebook ou Twitter, ou check-iné comme un fou sur les appli spécifiques de géolocalisation comme Foursquare. Mais il y a un autre moyen, d’autant plus simple qu’il est automatique : avoir un iPhone et permettre sans le savoir à Apple de pister nos moindres déplacements.
La découverte est signée Alasdair Allan et Pete Warden, deux spécialistes qui l’ont annoncé aujourd’hui à la conférence Where 2.0 après l’avoir explicité sur le site Radar. Leur trouvaille peut être résumée ainsi : les iPhone et iPad 3G fonctionnant sous le système d’exploitation iOS4 (disponible depuis juin 2010) enregistrent régulièrement la localisation des produits dans un fichier caché, dont le contenu est restauré à chaque sauvegarde ou migration d’appareil.
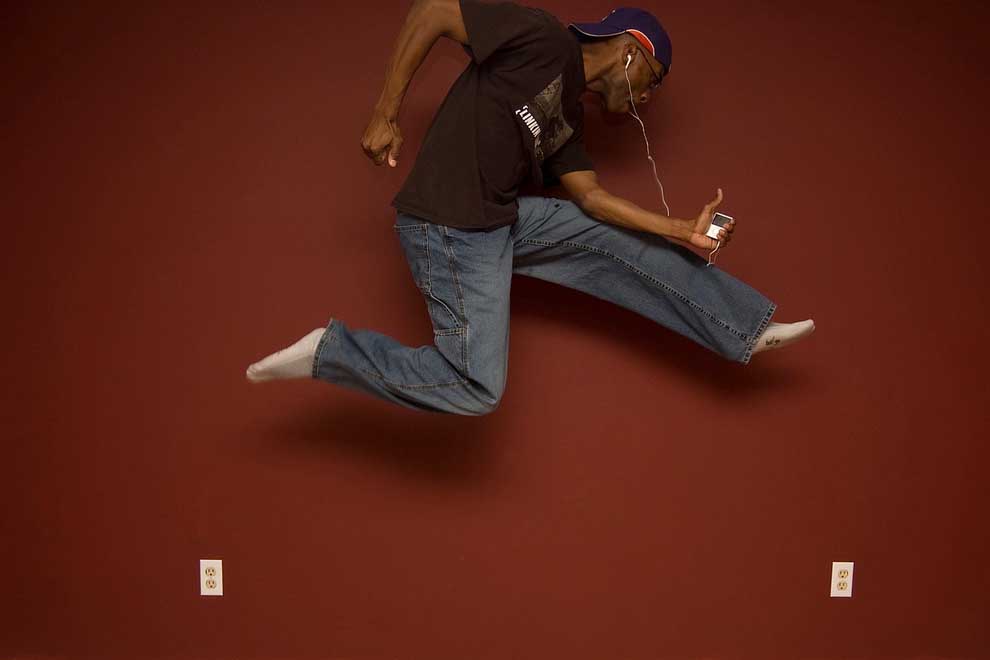
Concrètement, d’après Radar, les localisations sont stockées dans un fichier appelé consolidated.db, avec coordonnées géographiques évoluant en fonction de la date d’enregistrement. La chose n’est pas toujours archi précise, triangularisation oblige, mais un test auprès des collègues de Liberation.fr montre le genre de données ainsi enregistrées :
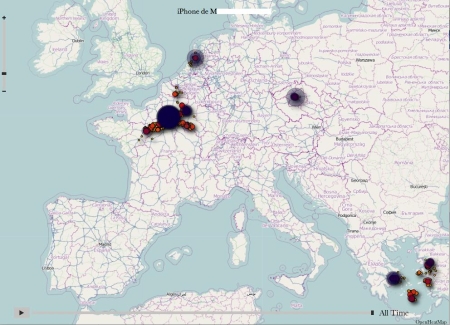
Un logiciel baptisé iPhone Tracker est disponible pour lire à son tour ce genre de traces. En mouvement (soit en faisant évoluer la chronologie), ça donne ça :
Washington DC to New York from Alasdair Allan on Vimeo.

Radar précise qu’à ce stade, rien ne prouve que ces données puissent échapper au contrôle de l’utilisateur (comprendre : être envoyées via le Net à des serveurs cachés contrôlés par de maléfiques Big Brother en puissance suivant la moindre de nos traces). De même, l’existence même de ce type d’informations n’est pas en soi une nouvelle : les opérateurs téléphoniques en disposent et peuvent les transmettre aux autorités dans certaines circonstances (enquêtes, etc.), mais uniquement sur demande en bonne et due forme (mandat, par exemple). Le problème ici soulevé est que le fichier en question n’est pas du tout crypté, donc facilement accessible en cas de vol ou d’emprunt de téléphone, par exemple. Des fonctionnalités permises par l’iOS4, comme la classification automatiques des photos prises par l’iPhone en fonction du lieu de la prise de vue (cf capture à droite), peuvent éventuellement constituer une piste d’explication quant à la présence d’un tel fichier dans le téléphone.
Parmi les pistes suggérées par Radar pour éviter ce genre de désagrément, on peut citer l’option « Encrypt iPhone Backup » accessibles via les paramètres d’iTunes une fois l’appareil connecté à l’ordinateur. Alasdair Allan et Pete Warden expliquent en détail leur trouvaille dans la vidéo ci-dessous (en anglais, 20 minutes) :
Pour la petite histoire, Peter Warden a travaillé durant cinq ans pour Apple (mais jamais directement sur l’avancée de l’iPhone), avant de quitter l’entreprise « en bons termes » il y a trois ans. Sur la page permettant de télécharger iPhone Tracker, qu’ils ont conçus eux-même, les deux geeks semblent presque déçus de leur découverte : « on est tous les deux de grands fans des produits Apple, et on ne prend vraiment aucun plaisir à mettre en avant ce problème ».
Monday, April 11. 2011
Via information aesthetics
-----
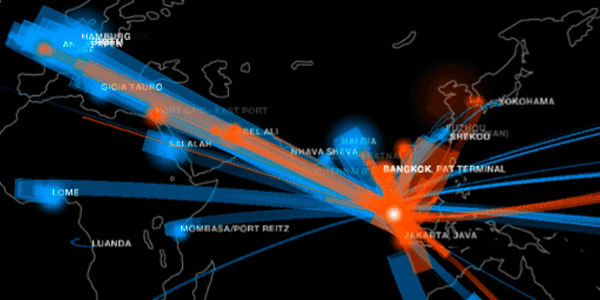
Next to their established offices in Boston and Milan, MIT Senseable Lab is now also active in Singapore, where they just launched an impressive exhibition [senseable.mit.edu] with five different graphical perspectives into Singapore's social, economic and mobility patterns. The five visualizations are all based on real-time data recorded and captured by a vast system of communication devices, microcontrollers and sensors.
What seems to be in the pipeline is an open API to allow others access to the rich data streams: "The exhibition is just the beginning of something that aims to develop into an open platform for the management of urban real-time data and the engagement of developer communities in writing innovative applications for the city."
"Hub of the World" shows the ships and containers arriving and leaving Singapore. "Isochronic Singapore" deformes a street map of the city proportional to its travel time. "Raining Taxis" combines taxi and rainfall data to establish the experience of not finding any taxis when it rains. "Urban Heat Islands" combines ambient temperature and energy usage to investigate whether cities are indeed warmer than the surrounding environment. "Formula One City" conveys the impact of the sports competition, for instance in terms of geo-located text messaging behavior. Lastly, "Real Time Talk" indicates the level of cellphone network usage throughout the city.
The exhibition runs from April 8th until May 1st at Singapore Art Museum.
Monday, April 04. 2011
Via OWNI
-----
by Marie D. Martel
Nous dirigeons-nous vers une technoculture du prêt, du partage, du streaming ?
Trop d’objets autour de nous, trop de bruit dans notre champ visuel, dans nos agrégateurs, dans nos résultats de recherche, trop de super-butinage (power-browsing), trop consommer, accumuler, remplir, excéder, évaluer, élaguer, se débarrasser, recycler-réduire-réutiliser, ouvrir la fenêtre, pas quinze fenêtres, respirer, relaxer, se vider l’esprit. C’est le printemps et une saison nouvelle qui s’annonce aux teintes discrètes (chromophobes ?) du néominimalisme.
After the bacchanal of post-modernism, the time has again come for neo-minimalism, neo-ascetism, neo-denial and sublime poverty. (Juhani Pallasmaa, cité dans Wikipedia)
ou encore :
By definition, « neo-minimalists » don’t have an overabundance of things in their lives. But one thing they tend to have more and more of these days is visibility. Recently, The New York Times talked to some people participating in the 100 Thing Challenge about how it has affected their lives; The BBC looked into the « Cult of Less; » and here on Boing Boing, Mark has beengetting down to the nitty-gritty of what the « lifestyle hack » involves. The common thread here is a growing number of people are realizing that our mountains of physical stuff are actually cluttering up more than just our houses. »
Cet extrait provient d’un article publié sur Boing Boing (traduit dans Le Courrier International), dans lequel Sean Bonner explore la dématérialisation ou la décroissance matérielle comme une possibilité issue des technologies actuelles et qui nous permet de reconsidérer nos interactions avec le monde et les autres en favorisant l’expérience plutôt que la consommation. À Toronto, le même auteur a aussi animé une présentation [en] sur le courant des technomades.
L’usage de circonstance par le prêt, le partage, le streaming
D’autres journalistes, comme Ramon Munez d’El Païs ont, dans la même perspective, élaboré l’idée que la propriété est un fardeau et que l’avenir de la consommation de la culture n’est plus lié à la propriété mais à l’usage de circonstance par le prêt, le partage, le streaming :
Après avoir été pendant trois siècles la valeur suprême de la civilisation occidentale, la propriété cesse d’être à la mode. Ne vous y trompez pas : il ne s’agit pas d’un retour du communisme ou d’une vague de ferveur qui nous ramènerait au détachement matériel des premières communautés chrétiennes. Ce sont le capitalisme lui-même, son incitation permanente à consommer et les technologies liées à Internet qui viennent bousculer des habitudes que l’on croyait bien enracinées. À quoi bon posséder des biens, les stocker, les entretenir, les protéger des voleurs, lorsqu’on dispose d’une offre illimitée de produits et de services accessibles en quelques clics ou moyennant la signature d’un contrat de location ?
Si cette tendance ne se limite pas au numérique, c’est sur Internet que la révolution est le plus avancée. Le téléchargement de contenus cède du terrain au streaming [diffusion en continu], c’est-à-dire à la reproduction instantanée de musique et de vidéos sans qu’il soit besoin de les conserver sur le disque dur de l’ordinateur. Des milliers de sites, légaux et illégaux, proposent un catalogue illimité de logiciels, films, morceaux de musique et jeux vidéo. Le succès du site de musique suédois Spotify ou du portail espagnol de séries télévisées Seriesyonkis vient bousculer les habitudes des consommateurs.
YouTube, le célèbre portail de vidéos en ligne de Google, est le symbole de la révolution en marche. Ses chiffres laissent pantois. Sur toutes les vidéos regardées chaque mois aux États-Unis, 43% (14,63 milliards) sont diffusées par YouTube, selon la société d’études de marché comScore. YouTube est suivi de près par Hulu, un site de streaming qui propose gratuitement des films et des séries télévisées. Avec 1,2 milliard de vidéos regardées, Hulu dépasse non seulement des monstres d’Internet comme Yahoo! ou Microsoft, mais aussi les portails de chaînes et de studios comme Viacom, CBS ou Fox.
D’après une étude sur le paysage audiovisuel espagnol réalisée en 2010 pour le compte de l’opérateur Telefónica et de la chaîne de télévision privée Antena, 3, 30% des internautes espagnols déclarent télécharger moins de fichiers, tandis que la moitié d’entre eux assurent que le streaming est leur manière habituelle de consommer des contenus audiovisuels sur Internet. “On constate un essor du streaming depuis au moins le printemps 2009”, assure Felipe Romero, l’un des auteurs de l’étude. “À court terme, les deux méthodes – téléchargement et streaming – vont coexister, mais il est clair que la seconde va prendre de plus en plus d’ampleur.”
Sur le blog Agnostic, May Be, on mentionne également cet article qui témoigne de l’émergence de la culture du partage dans le Time [en] :
[T]he ownership society was rotting from the inside out. Its demise began with Napster. The digitalization of music and the ability to share it made owning CDs superfluous. Then Napsterization spread to nearly all other media, and by 2008 the financial architecture that had been built to support all that ownership — the subprime mortgages and the credit-default swaps — had collapsed on top of us. Ownership hadn’t made the U.S. vital; it had just about ruined the country.
L’étape suivante franchie par le blogueur Andy Woodworth [en] (incidemment élu dans le palmarès 2010 des Shakers and Movers [en]) m’intéresse tout particulièrement. Il fait l’hypothèse qu’en ce moment l’attrait pour les bibliothèques reposerait peut-être moins sur la récession économique que sur l’accroissement du nombre de gens qui préfèrent emprunter plutôt que posséder.
L’émergence de cette culture suggère des possibilités et des tendances sur lesquelles les bibliothèques pourraient largement capitaliser, dit-il. Comment ? Pas seulement en incarnant elles-mêmes les instances équipées pour prêter des documents à partir de leurs collections mais peut-être surtout en se positionnant comme des facilitateurs, ou des médiateurs, capables de négocier et de supporter les citoyens en vue d’accéder aux ressources disponibles dans la déferlante du web.
Mais la question la plus évidente est la suivante : est-ce que les bibliothèques seront en mesure de profiter de l’apparition de cette société du prêt et du partage ? Elles apparaissent elles-mêmes souvent éreintées par les résistances, trop déboussolées pour servir de guide à qui ce soit, sans vision, sans plan pour penser la culture numérique au-delà de cet effort qui les amène à prononcer et à servir à toutes les sauces, le mot magique de la « bibliothèque numérique ».
Monday, January 31. 2011
Via BLDGBLOG
-----
by noreply@blogger.com (Geoff Manaugh)
 [Image: Courtesy of Terremark, via the Atlantic]. [Image: Courtesy of Terremark, via the Atlantic].
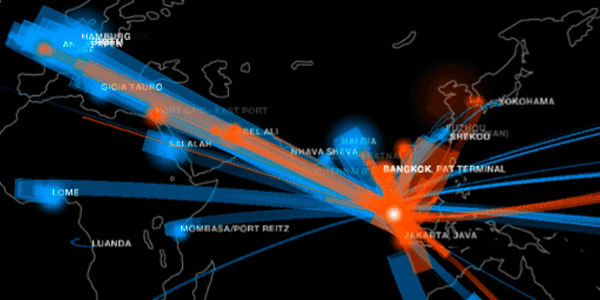
Andrew Blum has a short piece up at the Atlantic today about the geography of "internet choke points," and the threat of a "kill switch" that would allow countries (like Egypt) to turn off the internet on a national scale.
After all, Blum writes, "it's worth remembering that the Internet is a physical network," with physical vulnerabilities. "It matters who controls the nodes." Indeed, he adds, "what's often forgotten is that those networks actually have to physically connect—one router to another—often through something as simple and tangible as a yellow-jacketed fiber-optic cable. It's safe to suspect a network engineer in Egypt had a few of them dangling in his hands last night.
Blum specifically refers to a high-security building in Miami owned by Terremark; it is "the physical meeting point for more than 160 networks from around the world," and thus just one example of what Blum calls an internet "choke point." These international networks "meet there because of the building's excellent security, its redundant power systems, and its thick concrete walls, designed to survive a category 5 hurricane. But above all, they meet there because the building is 'carrier-neutral.' It's a Switzerland of the Internet, an unallied territory where competing networks can connect to each other."
But, as he points out, this neutrality is by no means guaranteed—and is even now subject to change.
Monday, January 17. 2011
Via L'Hebdo, Christophe Schenk
---
Invité à Genève dans le cadre de Lift Conference, l’artiste américain Hasan Elahi a fait de sa vie une œuvre d’art afin d’échapper au FBI. Portrait d’un précurseur de l’ère des réseaux sociaux.
Bien avant Facebook ou Twitter, Hasan Elahi a pris l’habitude de partager sur le Net ses allées et venues, ses faits et gestes.
Artiste et professeur à l’Université du Maryland, l’Américain de 38 ans se met en scène à travers un work in progress original, intitulé Tracking Transience: The Orwell Project.
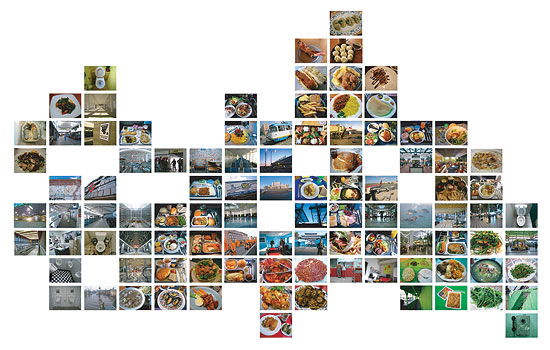
Sur son site internet, des milliers de photographies apparaissent, sous la forme de mosaïques thématiques, instants quotidiens accumulés depuis plus de sept ans. Panneaux autoroutiers, assiettes remplies de nourritures variées, urinoirs et toilettes publics, rien n’est oublié pour façonner un carnet intime au format numérique, plus provocateur qu’égocentrique, moins geek que citoyen.
Démarche artistique et acte politique, le travail de Hasan Elahi trouve en effet son origine en juin 2002, à l’aéroport de Detroit. De retour d’un séjour au Sénégal, où il exposait ses œuvres, l’artiste – Américain, mais originaire du Bangladesh – est arrêté à la douane et interrogé par des agents du FBI. On le soupçonne de cacher des armes dans un entrepôt et de collaborer avec des réseaux terroristes.
Parmi les questions qui lui sont posées, l’une va déterminer son action future: où était-il le 12 septembre 2001, au lendemain des attentats contre les Twin Towers? «J’ai pu répondre grâce à mon Palm, raconte Hasan Elahi, dont l’agenda avait conservé mon emploi du temps.» Si elles lui ont sauvé la mise une fois, les nouvelles technologies pourraient bien lui servir à nouveau.
Offre et demande. Interrogé fréquemment durant six mois, puis blanchi après s’être soumis au détecteur de mensonge durant trois heures, Hasan Elahi n’est pas rassuré pour autant.
«Je parcours plus de 100 000 kilomètres par année et prends souvent l’avion, explique-t-il. Je leur ai donc demandé de me fournir un document officiel, qui me laverait de tout soupçon. Ils ont refusé, mais m’ont répondu que je pouvais leur téléphoner la veille de mon voyage et qu’ils feraient le nécessaire pour que je n’aie pas de problèmes.»
Prenant les agents du FBI au mot, il décide de les appeler avant chacun de ses déplacements à l’étranger. Avant de choisir d’aller plus loin encore et de mettre sa vie en ligne au jour le jour, via un site internet dédié.
Grâce au GPS intégré dans son téléphone portable, Hasan Elahi est localisable en temps réel, tandis que des photos ajoutées chaque heure documentent ses actions, de ses repas à ses activités professionnelles, en passant par ses rencontres.
«Quand j’ai constaté que le FBI avait un dossier sur moi, j’ai choisi d’appliquer un principe économique simple, explique-t-il, à savoir la loi de l’offre et de la demande. En inondant le marché d’informations à mon sujet, celles relevées par le FBI perdraient irrémédiablement de leur valeur.»
Une démarche à laquelle s’ajoute un second principe, toujours plus en vogue à l’heure du règne de Google et de l’impossible anonymat: c’est quand on en dit le plus qu’on en révèle le moins.
«Sur mon site, on trouve des tas de petites informations sur moi, mais aucune qui ait vraiment de l’importance ou de la valeur. Jusqu’à il y a peu, certaines des organisations qui m’invitaient pour des conférences ne parvenaient même pas à trouver mon âge.»
Contrôler son identité. Si certains de ses proches ont accueilli ce projet avec un brin de nervosité – Hasan Elahi prend également des photos lorsqu’il est invité chez des amis, tout en prenant soin de ne pas dévoiler d’éléments qui permettraient de les reconnaître – ils ont rapidement cessé d’y prêter attention.
«Depuis le début de mes travaux, la culture a beaucoup changé, observe l’artiste. Par exemple, mes parents sont aujourd’hui mes visiteurs les plus réguliers, tout heureux de pouvoir savoir où je suis en continu. D’une certaine manière, ce type de documentation est peut-être le rêve de nombreux parents aujourd’hui.»
Une démarche qui ne diffère finalement guère des habitudes apparues ces dernières années avec l’avènement des blogs puis des réseaux sociaux.
Des sites qui permettent de suivre à la trace ceux qui s’y inscrivent et semblent sonner le glas des secrets, à la manière de Wikileaks. A moins que ce ne soit le contraire.
«Il ne faut pas oublier qu’avec ces sites, nous sommes désormais à la fois producteurs et consommateurs d’informations, note Hasan Elahi. On peut donc prendre le contrôle du système dans le même temps que l’on s’y intègre.»
Ainsi, il ne s’agit plus d’être la simple victime des systèmes de surveillance, mais de rediriger ceux-ci, par les moyens qui nous sont donnés. «Aujourd’hui, il suffit d’avoir un téléphone portable pour pouvoir prendre des photos ou filmer des séquences. Big Brother a été supplanté par des millions de Little Brothers. Et je ne suis pas sûr qu’il apprécie vraiment.»
Un peu plus de huit ans après sa première confrontation avec le FBI, Hasan Elahi poursuit toujours son œuvre via son site web. Sans même s’en rendre compte.
«C’est devenu une habitude, au même titre que consulter mes mails, les messages sur mon répondeur ou les réactions sur ma page Facebook, observe-t-il. Surtout, j’ai pu mettre en place des mécanismes automatiques au point que je ne me rends même plus compte que j’alimente mon site.»
Relayé dans les circuits artistiques, médiatiques ou technologiques, Tracking Transience a fait la renommée de Hasan Elahi, le posant en analyste confirmé des mutations que connaissent nos identités sur le Net. Le FBI pensait tenir un dangereux terroriste, il a donné naissance à un activiste de l’ère numérique.
Wednesday, December 22. 2010
Via MIT Technology Review
-----
A router that runs the Tor software prevents Web tracking.
By Tom Simonite
 |
| Credit: Technology Review |
Many political activists, nonprofits, and businesses use an anonymity system called Tor to encrypt and obscure what they do on the Internet. Now the U.S.-based nonprofit that distributes Tor is developing a low-cost home router with the same privacy protection built in.
The Tor software masks Web traffic by encrypting network messages and passing them through a series of relays (each Tor client can also become a relay for other users' messages). But using Tor has typically meant installing the software on a computer and then tweaking its operating system to ensure that all traffic is routed correctly through the program.
"We want to make anonymity something that can happen everywhere, all the time," says Jacob Appelbaum, a Tor project developer. "When you are connected to a router with Tor inside, all your traffic goes through Tor without you changing your system at all. It makes it simple to use."
Appelbaum says volunteers are already testing a small number of modified routers with Tor installed. The prototypes were made by installing new software onto a popular low-cost wireless router made by Buffalo Technology. The software was developed by Appelbaum and colleagues at Tor and is based on the work of the OpenWrt project, which offers open source code for networking equipment. The finished routers can be configured to pass all traffic through Tor, or only some kinds of communications. "You might want to run your VOIP device through Tor but not your other traffic," Appelbaum explains. They will also be capable of simultaneously offering Tor-protected and conventional wireless networks.
"If we find that these routers are useful [in the trials]," he says, "we could partner with OpenWrt and Buffalo to offer a version for sale that helps support the Tor and OpenWrt projects." The software will also be made available for people to install on routers they have bought themselves, Appelbaum says.
Besides serving as Tor clients, the new routers will help anonymize the traffic of other Tor users. This means that they could help boost the performance the Tor network.
When a person uses Tor to bring up a Web page, the request is encrypted and sent along a random path through other Tor computers that act as relays. This obscures the originating IP (Internet protocol) address—a unique code that can be used to track down a Web user, to filter access to certain sites or services, or to build up a profile of a person's Web use.
Generally, the process results in lag and restricts bandwidth, which deters some people from using Tor, says Chris Palmer, technology director at the Electronic Frontier Foundation. "The primary way to address that problem is to have more Tor relays in more places, connected to high-bandwidth, low-latency lines," he explains. "Wireless routers may fit the bill well, if they can be built with the computational resources necessary to run a Tor relay of decent capacity." Although consumer-grade routers are necessarily relatively low-powered, their capabilities have grown markedly in recent years, Palmer notes.
Tor routers could also make the entire Tor system better able to resist government attempts to block its use. An individual installation of Tor software hooks into the network by referring to a list of relays in a directory maintained by the Tor project. It is possible to block Tor by checking the same directory and preventing connections to the servers listed—a tactic apparently used by the Chinese authorities. It is possible to get around such a block, however, by configuring the Tor software to act as a "bridge," or a private relay, that can only be discovered by word of mouth. A Tor router can also act as a bridge, and Appelbaum is considering making that a default setting.
During the protests in Iran that followed the 2009 election, the EFF campaigned for more people to act as Tor bridges to keep the government from blocking the tool, and Palmer says increasing the supply of bridges remains important. "It makes the adversary's job more difficult when there are more possible bridges to advertise and use," he says.
Appelbaum says, "If you have 10,000 people using these little routers, then China would have a lot more difficulty blocking Tor."
Copyright Technology Review 2010.
Monday, October 04. 2010
-----
A Web startup demos a "predictive" search engine.
By Tom Simonite
 |
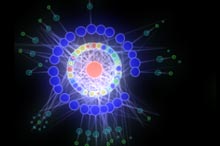
Eye candy: This visualization shows the connections between different places, companies, and people, following a search using Recorded Future.
Credit: Recorded Future |
A startup called Recorded Future has developed a tool that scrapes real-time data from the Internet to find hints of what will happen in the future. The company's search tool spits out results on a timeline that stretches into the future as well as the past.
The 18-month-old company gained attention earlier this year after receiving money from the venture capital arms of both Google and the CIA. Now the company has offered a glimpse of how its technology works.
Conventional search engines like Google use links to rank and connect different Web pages. Recorded Future's software goes a level deeper by analyzing the content of pages to track the "invisible" connections between people, places, and events described online.
"That makes it possible for me to look for specific patterns, like product releases expected from Apple in the near future, or to identify when a company plans to invest or expand into India," says Christopher Ahlberg, founder of the Boston-based firm.
A search for information about drug company Merck, for example, generates a timeline showing not only recent news on earnings but also when various drug trials registered with the website clinicaltrials.gov will end in coming years. Another search revealed when various news outlets predict that Facebook will make its initial public offering.
That is done using a constantly updated index of what Ahlberg calls "streaming data," including news articles, filings with government regulators, Twitter updates, and transcripts from earnings calls or political and economic speeches. Recorded Future uses linguistic algorithms to identify specific types of events, such as product releases, mergers, or natural disasters, the date when those events will happen, and related entities such as people, companies, and countries. The tool can also track the sentiment of news coverage about companies, classifying it as either good or bad.
Recorded Future's customer base is currently "sub-100," says Ahlberg. It includes a mix of financial firms, government analysts, and media analysts, who pay a monthly fee to access the online tools. "Government analysts are interested in tracking people and places, while financial services may want to reveal events coming up around particular companies," says Ahlberg.
As well as providing a slick online interface to perform searches that spit out timelines showing the results (see video), Recorded Future offers free e-mail newsletters that tip users off to predictions in specific areas. It also makes it possible for customers to write software that draws on the tool's data and analysis through application programming interfaces, or APIS.
In time, this may lead to the development of apps targeted at consumers, says Ahlberg. "If I'm about to buy an iPhone, I might want to know if I am going to look stupid because they'll launch a new one next week, or how long it usually takes for competitors to launch competing products after a new Apple launch." Financial analysts are already using the company's APIs to overlay or even integrate Recorded Future's data into their own models, he says.
"We have proven out that our data can make strong predictions," says Ahlberg, citing studies that compared Recorded Future's output with changes in the volume of activity around particular financial stocks. "We found that our momentum metric, which indicates the strength of activity around an event or entity, and our future events correlate with the volume of market activity," says Ahlberg.
His company's tools can also be used to work out which sources of information give the best clues as to future events. A recent analysis showed that the posts on one of the Financial Times's blogs were better than other news sources at predicting the performance of companies on the S&P 500 share index. Negative posts about a company correlated with below-market performance a week later, while positive ones correlated with above-market performance.
"What they're really doing here is identifying and collating statements that have been made about the future," says Steven Skiena at the State University of New York at Stony Brook. Skiena developed similar technology used by another startup, General Sentiment, to mine material from news and blogs. "An analyst can use those to inform their own predictions, less risky than Recorded Future actually making predictions themselves."
Various tools are capable of extracting events, people, and companies from text, but aligning that information in time is a trickier task, says Panagiotis Ipeirotis, at New York University's Leonard Stern School of Business. Ipeirotis researches how economically important data can be mined from online news sources and social media. "Analysis of sequences of events is very interesting, and underexploited in the research literature," he says. "Even getting decently timed data of news articles in order to properly generate event sequences is a hard problem."
This focus on the timeline sets Recorded Future apart from other firms trying to gain insights by mining news and other data, says Ipeirotis. "I'm curious to see when other text analytics firms will jump into the trend."
Recorded Future is about to expand its service to cover Arabic and Chinese sources. Making its indexes bigger is a major priority. "I'd like to be able to get in front of every piece of streaming data on the planet," says Ahlberg.
As the databases covered by Recorded Future, General Sentiment, and others grow, more powerful types of analysis will become possible, says Skiena. "I'm currently working with social scientists on models to predict what the probability is that a person that gets few mentions today suddenly becomes very famous in the future, by looking back at years of past data," he says.
Copyright Technology Review 2010.
Personal comment:
This has to be related to this sentence by Google CEO, Eric Schmidt: "I ACTUALLY think most people dont want Google to answer their questions, they want Google to tell them what they should be doing next." (taken from this article/post by William Gibson fro the New York Times).
Oh, really?
Wednesday, August 25. 2010
-----
The way privacy is encoded into software doesn't match the way we handle it in real life.
By Danah Boyd
 |
| Credit: Nick Reddyhoff |
Each time Facebook's privacy settings change or a technology makes personal information available to new audiences, people scream foul. Each time, their cries seem to fall on deaf ears.
The reason for this disconnect is that in a computational world, privacy is often implemented through access control. Yet privacy is not simply about controlling access. It's about understanding a social context, having a sense of how our information is passed around by others, and sharing accordingly. As social media mature, we must rethink how we encode privacy into our systems.
Privacy is not in opposition to speaking in public. We speak privately in public all the time. Sitting in a restaurant, we have intimate conversations knowing that the waitress may overhear. We count on what Erving Goffman called "civil inattention": people will politely ignore us, and even if they listen they won't join in, because doing so violates social norms. Of course, if a close friend sits at the neighboring table, everything changes. Whether an environment is public or not is beside the point. It's the situation that matters.
Whenever we speak in face-to-face settings, we modify our communication on the basis of cues like who's present and how far our voices carry. We negotiate privacy explicitly--"Please don't tell anyone"--or through tacit understanding. Sometimes, this fails. A friend might gossip behind our back or fail to understand what we thought was implied. Such incidents make us question our interpretation of the situation or the trustworthiness of the friend.
All this also applies online, but with additional complications. Digital walls do almost have ears; they listen, record, and share our messages. Before we can communicate appropriately in a social environment like Facebook or Twitter, we must develop a sense for how and what people share.
When the privacy options available to us change, we are more likely to question the system than to alter our own behavior. But such changes strain our relationships and undermine our ability to navigate broad social norms. People who can be whoever they want, wherever they want, are a privileged minority.
As social media become more embedded in everyday society, the mismatch between the rule-based privacy that software offers and the subtler, intuitive ways that humans understand the concept will increasingly cause cultural collisions and social slips. But people will not abandon social media, nor will privacy disappear. They will simply work harder to carve out a space for privacy as they understand it and to maintain control, whether by using pseudonyms or speaking in code.
Instead of forcing users to do that, why not make our social software support the way we naturally handle privacy? There is much to be said for allowing the sunlight of diversity to shine. But too much sunlight scorches the earth. Let's create a forest, not a desert.
Danah Boyd is a social-media researcher at Microsoft Research New England, a fellow at Harvard University's Berkman Center for Internet and Society, and a member of the 2010 TR35.
Copyright Technology Review 2010.
Personal comment:
In connection to this post, you can look a this picture from Mashable site.
Thursday, August 19. 2010
-----
Security legend Paul Kocher talks about the attitudes shaping Congress's latest tech misstep.
If the Internet ever does something unfriendly to the national security interests of the United States, what if the president of said Union could pick up a cold war-era style phone - or maybe whip out an iPhone pre-loaded with a custom "kill the internet" app - and order that it be shut down?
That's what activists are saying is one potential outcome of the Protecting Cyberspace as a National Asset Act. The so-called "Internet Kill Switch" is not actually an outcome of that bill, by the way - some commentators have compared this meme to the "death panels" myth that almost derailed the healthcare bill.
But the fact remains that the president has broad power under the 1934 Telecommunications Act to restrict "wire communications" during a time of war - and that includes the Internet. So even under existing laws, an off switch for the United States' most important information conduit is, in theory at least, only one over-eager lawmaker in chief away from reality.
Paul Kocher, current CEO of Cryptography Research, is a legend in the field of security - one of the engineers behind SSL 3.0 and an innovator in a host of other areas. Recently I interviewed him on the subject; here's what he had to say about the so-called "Internet Kill Switch."
"It's a Rorschach blot."
"On one level it's, absurd, and on others it's impractical and frightening. It's a Rorschach blot.
When you build something that will shut down a massively critical piece of infrastructure that people have tried to make reliable, that's a more frightening prospect than anything that could have inspired such a defense."
"It's a very blunt weapon."
"Networks like internet are critical for a lot of tasks - if you ever flipped a switch on that, you'd cause tremendous amounts of harm. It's unclear you'd get any particular benefit from doing that."
"Maybe I'm being cynical, but my read on the rationale [for the Internet Kill Switch] is that it's a fear of technology."
"The idea that people can kill the technology if they wish to makes people feel reassured that the technology won't go rogue in some way. If you had an army of robots walking around you'd like to have switch to turn them off - people still have that concept of the Internet."
"I can guarantee every teenage hacker will try to figure out how to trigger it."
[Ed. It goes without saying that Paul was once one of those teenage hackers, and knows whereof he speaks.]
"If I want my name in the paper, or to have an effect that's bad on the world, it's hard to think of something more perfectly designed for that kind of use."
Attemps to degrade the quality of civilian GPS signals shows that disabling communications networks hurts the good guys more than it hurts the bad guys.
"The whole GPS infrastructure is built with a mechanism where they can degrade the quality of location measurements. It's designed so they could have the military have more accurate GPS units than civilians.
But it turned out the military ended up using civilain GPS receivers because they're cheaper. They ended up disabling the degradation capability because the harm caused to the U.S. military exceeds the benefit to the folks they're fighting."
"Stopping a Denial of Service attack by shutting down the Internet is like trying to stop a small explosion by triggering a much larger one."
"You could conceivably come up with ways to bring down the entire Internet, by playing games with BGP protocol or bringing down the entire DNS archicecture. But you can't stop a pinpointed attack with this.... If you had a kill switch you'd either shut down entire internet or achieve nothing.
"The question this comes down to is, 'Is there some scenario where one would really want to bring the entire internet down?'"
"Everybody working from home: gone. Everybody's [VoIP] phone connection: gone. Everybody's website: gone. That's the only binary choice you can really achieve with this."
For technical as well as political reasons, no bill with anything resembling an "Internet Kill Switch" will ever be signed into law.
"If Congress decrees electrons have positive charge and gravity goes in the other direction, it doesn't mean it's possible to achieve those things.... But the reality is that if something like that came close to passing there would be a tremendous outcry.
"The government has had some misleading experience with this area, with telephone switches where there are requirements that there be backdoors so law enforcement can do wiretaps and eavesdrop on calls. But there's a lot more homogeneity in telephone infrastructure than within the packet-switched internet infrastructure.
 Follow Mims on Twitter or contact him via email. Follow Mims on Twitter or contact him via email.
Wednesday, August 11. 2010
Via NextNature
-----

At Tokyo’s Shinagawa Station visitors can now select beverages from a 47-inch touch panel.
An embedded camera will recognize your gender and age, allowing the machine to recommend a beverage suitable to whatever stereotype is attached to your particular circumstances. It will store your purchasing history too, so you can be freaked out by tailored ads every time you use it. 500 more of these units are planned to be installed in and around Tokyo over the next two years, with operating company JR East expecting them to tally up 30 percent more sales than their analog brethren. Via engadget.com

Smart vending machines in the streets show that Big Brother is being naturally accepted in a pixel consuming society.
|



 [Image: Courtesy of
[Image: Courtesy of