Tuesday, May 29. 2012
By fabric | ch
-----
I wasn't aware of this feature in recent browsers and Christophe Guignard just pointed out to me: Do Not Track!
As stated on Wikipedia: "The do not track header is a proposed HTTP header field that would request a web application to disable their tracking of a user. The "Do Not Track" header was originally proposed in 2009 by researchers Christopher Soghoian, Sid Stamm, and Dan Kaminsky.[1] It is currently being standardized by the W3C.[2]
In December 2010, Microsoft announced support for the DNT mechanism in its Internet Explorer 9 web browser.[3] Followed by Mozilla's Firefox,[4]Apple's Safari[5] and Opera all later added support.[6] It is not currently supported by Google Chrome, but will be incorporated by the end of 2012.[7][8]
The header currently accepts three values, 1 in case the user does not wish to be tracked (opt out), 0 in case the user does (opt in), or null (no header sent) if the user has not expressed a preference. The default is to not send the header, until the user chooses to enable the setting via their browser."
So, for the ones who don't want to be tracked (filed, numbered, etc.), please activate and spread the word! You'll find information in the Help section of your regular browser (serach for DNT or Do Not Track). By default everything is "unset" (which means websites can track you if they desire), therefore if you want to be tracked, don't change anything, because this is the "default" configuratiobn of most websites. In some cases (IE), you can even precise which services can/cannot track you.
As an exemple read the Twitter support to DNT.
Wednesday, April 11. 2012
Via MIT Technology Review
-----
The chip achieves unprecedented accuracy by processing information from many different sensors.
By Christopher Mims
Broadcom has just rolled out a chip for smart phones that promises to indicate location ultra-precisely, possibly within a few centimeters, vertically and horizontally, indoors and out.
The unprecedented accuracy of the Broadcom 4752 chip results from the sheer breadth of sensors from which it can process information. It can receive signals from global navigation satellites, cell-phone towers, and Wi-Fi hot spots, and also input from gyroscopes, accelerometers, step counters, and altimeters.
The variety of location data available to mobile-device makers means that in our increasingly radio-frequency-dense world, location services will continue to become more refined.
In theory, the new chip can even determine what floor of a building you're on, thanks to its ability to integrate information from the atmospheric pressure sensor on many models of Android phones. The company calls abilities like this "ubiquitous navigation," and the idea is that it will enable a new kind of e-commerce predicated on the fact that shopkeepers will know the moment you walk by their front door, or when you are looking at a particular product, and can offer you coupons at that instant.
The integration of new kinds of location data opens up the possibility of navigating indoors, where GPS signals are weak or nonexistent.
Broadcom is already the largest provider of GPS chips to smart-phone makers. Its new integrated circuit relies on sensors that aren't present in every new smart phone, so it won't perform the same in all devices. The new chip, like a number of existing ones, has the ability to triangulate using Wi-Fi hot spots. Broadcom maintains a database of these hot spots for client use, but it says most of its clients maintain their own.
A company that pioneered the construction and maintenance of these kinds of Wi-Fi hot spot databases is SkyHook Wireless. Skyhook CEO Ted Morgan is skeptical that Broadcom can catch up to his company's software-based system allowing for precise indoor location. "Broadcom is just now talking about something we have been doing for seven to eight years, uncovering all the challenges," says Morgan. These include battery management and cataloging a new wave of mobile Wi-Fi hot spots. "Broadcom has never done major deployment," adds Morgan.
Scott Pomerantz, vice president of the GPS division at Broadcom, counters that "the big [mobile] operating systems all have a strategy in place" to create their own Wi-Fi databases. Pomerantz isn't allowed to name names, but one of Broadcom's biggest customers is Apple, which previously used Skyhook for location services in its iPhone but now employs its own, Apple-built location system.
At least one feature of Broadcom's new GPS chip is entirely forward-looking, and integrates data from a source that is not yet commercially deployed: Bluetooth beacons. (Bluetooth is the wireless standard used for short-range communications in devices like wireless keyboards and phone headsets.)
"The use case [for Bluetooth beacons] might be malls," says Pomerantz. "It would be a good investment for a mall to put up a deployment—perhaps put them up every 100 yards, and then unlock the ability for people walking around mall to get very precise couponing information."
"The density of these sensors will give you even finer location," says Charlie Abraham, vice president of engineering at Broadcom. "It could show you where the bananas are within a store—even on which shelf there's a specific brand."
Copyright Technology Review 2012.
Wednesday, April 04. 2012
By fabric | ch
-----



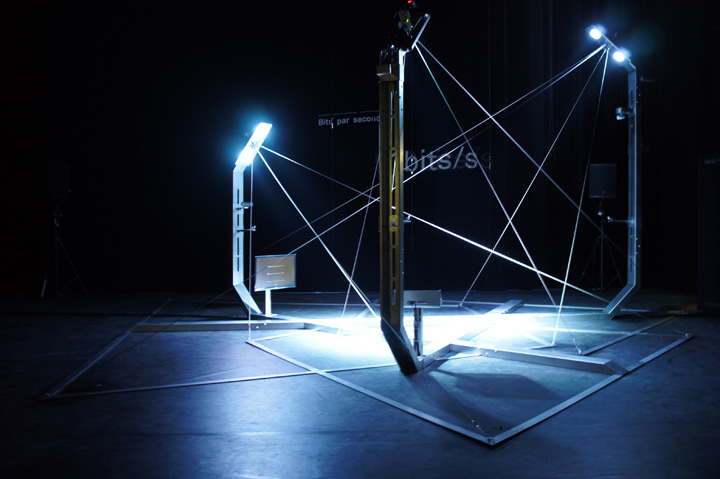
Paranoid Shelter, beta testing, residency at the EPFL-ECAL Lab (late summer and winter 2011)
PARANOID SHELTER
Paranoid Shelter is a recent installation / architectural device that fabric | ch finalized later in 2011 after a 6 months residency at the EPFL-ECAL Lab in Renens (Switzerland). It was realized with the support of Pro Helvetia, the OFC, the City of Lausanne and the State of Vaud. It was initiated and first presented as sketches back in 2008 (!), in the context of a colloquium about surveillance at the Palais de Tokyo in Paris.
Being created in the context of a theatrical collaboration with french writer and essayist Eric Sadin around his books about contemporary surveillance ( Surveillance globale and Globale paranoïa --both published back in 2009--), Paranoid Shelter revisits the old figure/myth of the architectural shelter, articulated by the use of surveillance technologies as building blocks
Doing so, it states that contemporary surveillance is in a “de facto” relation with the old myth of the shelter and that it can be considered as a contemporary way to build it, yet in a total different way, somehow problematic because it usually mixes public and private interests, freedom and penalty or censorship and remains unclear.
Therefore, filled with monitoring technologies and exploring their formal potential (the main formal aspects are “autological”: the materialisation of the cones of vision from the surveillance cameras fixed on a frame that evokes public infrastructure) as well as their functional incidence (a tele-"neo-nomad" condition?), the project also comments about "smartness" as Paranoid Shelter is composed of the same ingredients : active, mediated, monitored or scrutinized, possibly robotized and sometimes "intelligent". Consequently, it points out the links between “smartness” and surveillance that can’t be undervalued (what is the status of the data that are collected? what are the inner natures of codes and softwares that drive the behaviours of the architecture?)
"Smartness" is undoubtedly a coming way to architecture space largely debated in specialized circles. Will this be the work of the architect or the engineer is still to be decided (following the heritage of architectural critic from the 60ies Reyner Banham, we state it should mainly be designed by the architect and implemeted in close relation with the engineer). It is, along with parallel questions about sustainability, digital design & fabrication, code, weather, robotics and possibly "geo-engineering", one of the hot topics within the recent architectural debate that will drive the evolution of the discipline.
As with surveillance, "smartness" will generate data, it will leave "traces" and "tracks". This latter inevitably led to raise the same issues as those related to the privacy (or not) of personal data. The statuses of data, codes and technologies are, in fact, a real issue for society in general and for architecture in particular. To envision the question, just think about a public space monitored by a private company that owns and uses the data for marketing purposes (we all know this already) or a private home where all the data and images are openly released on the networks (next frontier for some hackers). Worse: a state that sells its monitored but non-nominal public information to companies for them to build commercial products. We are confronted to a confusion of gender, at best an hybridization.
Paranoid Shelter articulates and objectifies the idea of surveillance/smartness as one of the main vectors of transformation in our contemporary space: while responding to none of the traditional ways to describe a shelter (Paranoid Shelter doesn't protect you from rain or cold, it doesn't really protect you neither from any physical danger but can maybe anticipate it), while being nearly totally transparent and mostly immaterial, it is nonetheless totally different to stand inside its layered frames and limits than to stand outside them. If an outside does, indeed, still exist. The space is changed and architected by the means of invisible codes, behaviours and is mediated through the channels of technologies and networks.
With Paranoid Shelter, the code is obviously an integral part of the architecture and its status tries to be clear: custom created by the design team (architects and scientists) for the project along with its physical parts, the code is in this case part of the structure and the author’s work. The raw data, generated by the public and that drives the reactivity of the spatial device, are public and fully open to any other public use. It is a shared common space where the infrastructure is made available to the public but doesn’t belong to him, the space and data do.
Paranoid Shelter demonstrates the fact that a piece of code and technology should indeed be considered as architecture, that it transforms the nature of space and our experience of it, like previous technologies did (electricity, artificial lighting, heating, air conditioning, elevators, etc.), but also like walls and windows can do. It suggests new ways of living too, nearly tribal within an equally new, partly immaterial, open and mediated shelter.
Paranoid Shelter can be displayed either as an architectural installation of its own (museum), where its programs let it behave in an autonomous and "intelligent" way, or as a scenographic architecture, on stage (theatre) in the context of collaborations and where it is driven by different programs that are (mostly) remotely controlled.
Paranoid Shelter building blocks are (hardware):
- 3 network (surveillance) cameras, w. night shot functionalities
- 1 network (surveillance) PTZ (Pan Tilt Zoom) camera
- 3 embeded microphones
- 2 libellium wireless network sensors boards
- 3 temperature sensors
- 2 light sensors
- 1 humidity sensor
- 1 pressure sensor
- 1 CO2 level sensor
- 1 O2 level sensor
- 1 pollution sensor
- 1 dust sensor
- 1 dedicated wifi access point ("paranoid hotspot")
- 6 dmx controllable led lights
- 1 lcd led acreen (1920x1080), 2nd optional.
- (optional) 1 beamer 1280x800, 4000lm.
- 1 air conditioned servers' cabinet
- servers, lanboxes
- a set of inox cables
- an overall inox frame
- some books
- some blankets
Paranoid Shelter other building blocks are (custom softwares, codes & data):
- quantity of mouvement & camera tracking
- areas' occupation, heat zones
- moving objects' location
- presence/absence counting / per overall object and surrounding / per sub zones
- normal/abnormal behaviours
- sound patterns recognition, "gunshot tracking"
- noise level
- sound location
- atmosphere monitoring
- normal/abnormal atmosphere
- wifi monitoring ("snooping")
- "intelligent" behaviours, set of rules, scripts and codes
- spatial uses' data

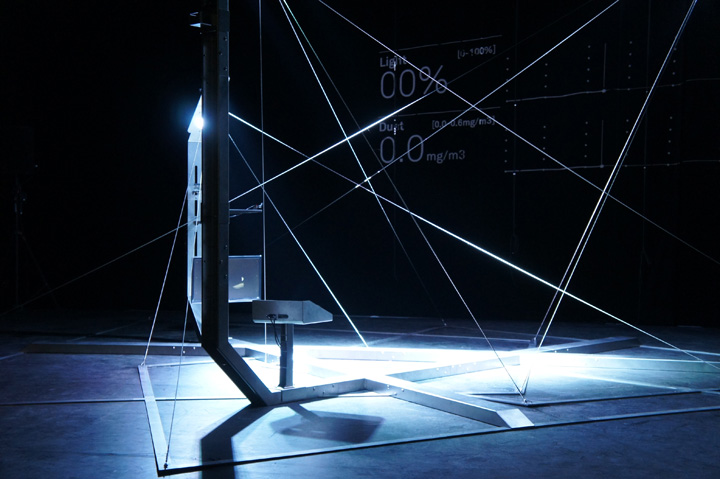
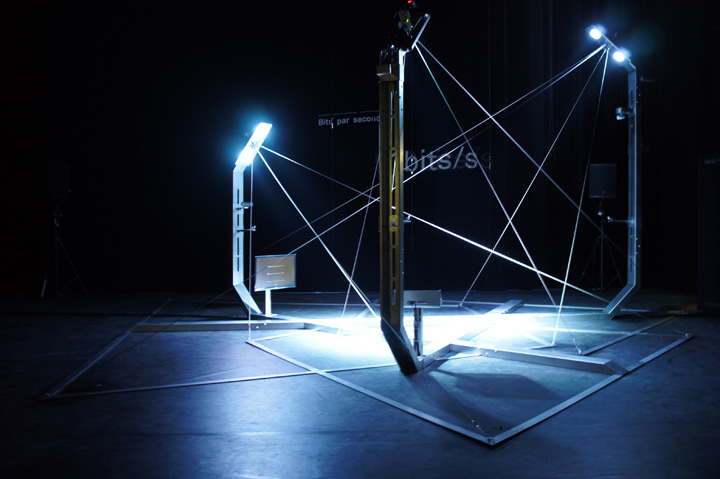

Pictures: Patrick Keller, Nicolas Besson, Alban Van Wassenhove
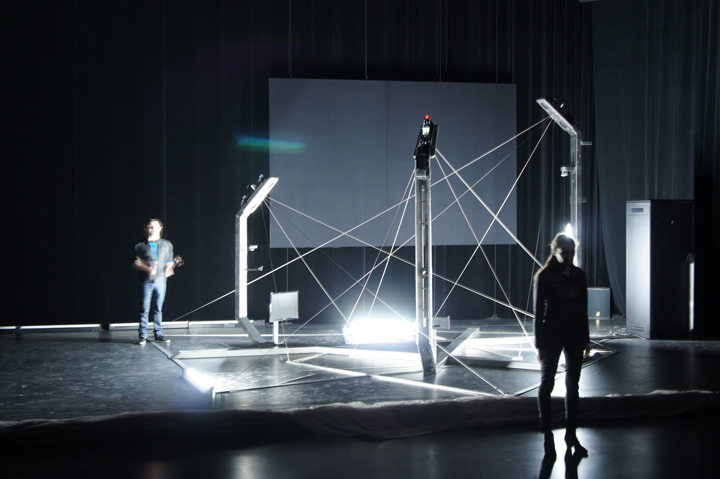
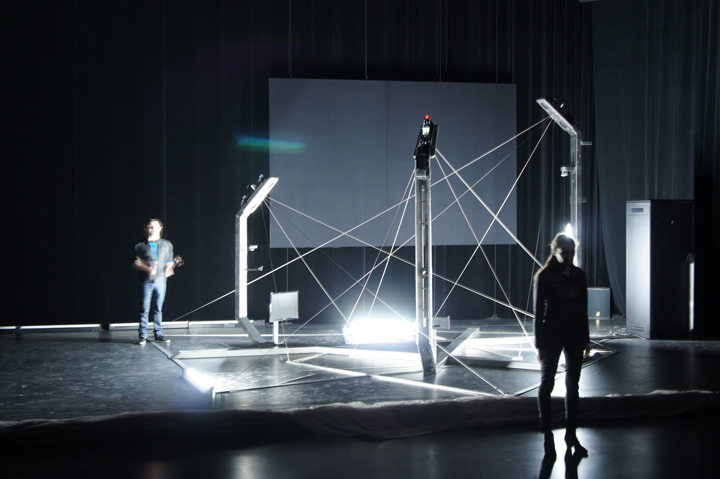
On stage with Laure Wolf + Gurshad Shaheman (actors). Used as a scenographic space/device, in the context of Eric Sadin's theatrical, Globale Surveillance. CDN (Centre Dramatique National) / ESAM of Caen in France. March 2012.
The theatrical deals with societal, spatial and theoretical questions within a "global surveillance" context (networks, communications, marketing, health, economy, (state) security).
-
Team:
Project: Patrick Keller, Christian Babski, Christophe Guignard, Stéphane Carion, Nicolas Besson, Leticia Carmo
Software development: fabric | ch, Computed·By
Digital fabrication, metal: Metoforme SA
Wednesday, October 12. 2011
Via The Funambulist
-----

The Trial by Orson Welles (adapted from Franz Kafka’s novel) 1962
The structuralist descriptions established by Michel Foucault about discipline are thought to be well known, especially by architects for who the book has been simplified with images that they can understand. The architectual paradigm of the panopticon (see previous essay) is quoted everywhere and became indissoluble from Foucault’s work despite its very large extents. What most people did not understand is that the panopticon as it has been thought by Jeremy Bentham is interpreted by Foucault as the paradigm of a society of discipline which does not apply anymore to the current organizational scheme of the Western world.
In the following text, Gilles Deleuze, his friend -and admirer-, summarizes the current paradigm as interpreted by Foucault as a society of control. His short essay, which is more developed in his book dedicated about Foucault’s work, insists on this shift from discipline to control. He uses The Trial (see previous essay) by Franz Kafka as a perfect example of this change of paradigm. In fact, Kafka introduced the choice to his charged character K between an apparent acquittal (between two incarcerations), symbol of the discipline, and limitless postponements that are proper to the society of control. As Deleuze puts it:
In the disciplinary societies one was always starting again (from school to the barracks, from the barracks to the factory), while in the societies of control one is never finished with anything–the corporation, the educational system, the armed services being metastable states coexisting in one and the same modulation, like a universal system of deformation.
A bit further in the text, he continues by giving an example invented by his friend Felix Guattari in order to illustrate how control exercises its power on the bodies:
Felix Guattari has imagined a city where one would be able to leave one’s apartment, one’s street, one’s neighborhood, thanks to one’s (dividual) electronic card that raises a given barrier; but the card could just as easily be rejected on a given day or between certain hours; what counts is not the barrier but the computer that tracks each person’s position–licit or illicit–and effects a universal modulation.
This very simple example carries some tremendous human implications when applied literally -with the dozens of Israeli checkpoints inside the West Bank for example- but also more figuratively in a society we are more used to in the Western World in which the concept of freedom cannot be understood outside of a policed capitalist system.
By his extremely precise description of this system’s mechanisms, Michel Foucault acts violently against it as numerous of those mechanisms are in fact decoy and camouflage apparatuses.
For the archive, here is Deleuze’s text:
Society of Control
by Gilles Deleuze
I. Historical
Foucault located the disciplinary societies in the eighteenth and nineteenth centuries; they reach their height at the outset of the twentieth. They initiate the organization of vast spaces of enclosure. The individual never ceases passing from one closed environment to another, each having its own laws: first the family; then the school (“you are no longer in your family”); then the barracks (“you are no longer at school”); then the factory; from time to time the hospital; possibly the prison, the preeminent instance of the enclosed environment. It’s the prison that serves as the analogical model: at the sight of some laborers, the heroine of Rossellini’s Europa ’51 could exclaim, “I thought I was seeing convicts.”
Foucault has brilliantly analyzed the ideal project of these environments of enclosure, particularly visible within the factory: to concentrate; to distribute in space; to order in time; to compose a productive force within the dimension of space-time whose effect will be greater than the sum of its component forces. But what Foucault recognized as well was the transience of this model: it succeeded that of the societies of sovereignty, the goal and functions of which were something quite different (to tax rather than to organize production, to rule on death rather than to administer life); the transition took place over time, and Napoleon seemed to effect the large-scale conversion from one society to the other. But in their turn the disciplines underwent a crisis to the benefit of new forces that were gradually instituted and which accelerated after World War II: a disciplinary society was what we already no longer were, what we had ceased to be.
We are in a generalized crisis in relation to all the environments of enclosure–prison, hospital, factory, school, family. The family is an “interior,” in crisis like all other interiors–scholarly, professional, etc. The administrations in charge never cease announcing supposedly necessary reforms: to reform schools, to reform industries, hospitals, the armed forces, prisons. But everyone knows that these institutions are finished, whatever the length of their expiration periods. It’s only a matter of administering their last rites and of keeping people employed until the installation of the new forces knocking at the door. These are the societies of control, which are in the process of replacing disciplinary societies. “Control” is the name Burroughs proposes as a term for the new monster, one that Foucault recognizes as our immediate future. Paul Virilio also is continually analyzing the ultrarapid forms of free-floating control that replaced the old disciplines operating in the time frame of a closed system. There is no need to invoke the extraordinary pharmaceutical productions, the molecular engineering, the genetic manipulations, although these are slated to enter the new process. There is no need to ask which is the toughest regime, for it’s within each of them that liberating and enslaving forces confront one another. For example, in the crisis of the hospital as environment of enclosure, neighborhood clinics, hospices, and day care could at first express new freedom, but they could participate as well in mechanisms of control that are equal to the harshest of confinements. There is no need to fear or hope, but only to look for new weapons.
II. Logic
The different internments of spaces of enclosure through which the individual passes are independent variables: each time one us supposed to start from zero, and although a common language for all these places exists, it is analogical. One the other hand, the different control mechanisms are inseparable variations, forming a system of variable geometry the language of which is numerical (which doesn’t necessarily mean binary). Enclosures are molds, distinct castings, but controls are a modulation, like a self-deforming cast that will continuously change from one moment to the other, or like a sieve whose mesh will transmute from point to point.
This is obvious in the matter of salaries: the factory was a body that contained its internal forces at the level of equilibrium, the highest possible in terms of production, the lowest possible in terms of wages; but in a society of control, the corporation has replaced the factory, and the corporation is a spirit, a gas. Of course the factory was already familiar with the system of bonuses, but the corporation works more deeply to impose a modulation of each salary, in states of perpetual metastability that operate through challenges, contests, and highly comic group sessions. If the most idiotic television game shows are so successful, it’s because they express the corporate situation with great precision. The factory constituted individuals as a single body to the double advantage of the boss who surveyed each element within the mass and the unions who mobilized a mass resistance; but the corporation constantly presents the brashest rivalry as a healthy form of emulation, an excellent motivational force that opposes individuals against one another and runs through each, dividing each within. The modulating principle of “salary according to merit” has not failed to tempt national education itself. Indeed, just as the corporation replaces the factory, perpetual training tends to replace the school, and continuous control to replace the examination. Which is the surest way of delivering the school over to the corporation.
In the disciplinary societies one was always starting again (from school to the barracks, from the barracks to the factory), while in the societies of control one is never finished with anything–the corporation, the educational system, the armed services being metastable states coexisting in one and the same modulation, like a universal system of deformation. In The Trial, Kafka, who had already placed himself at the pivotal point between two types of social formation, described the most fearsome of judicial forms. The apparent acquittal of the disciplinary societies (between two incarcerations); and the limitless postponements of the societies of control (in continuous variation) are two very different modes of juridicial life, and if our law is hesitant, itself in crisis, it’s because we are leaving one in order to enter the other. The disciplinary societies have two poles: the signature that designates the individual, and the number or administrative numeration that indicates his or her position within a mass. This is because the disciplines never saw any incompatibility between these two, and because at the same time power individualizes and masses together, that is, constitutes those over whom it exercises power into a body and molds the individuality of each member of that body. (Foucault saw the origin of this double charge in the pastoral power of the priest–the flock and each of its animals–but civil power moves in turn and by other means to make itself lay “priest.”) In the societies of control, on the other hand, what is important is no longer either a signature or a number, but a code: the code is a password, while on the other hand disciplinary societies are regulated by watchwords (as much from the point of view of integration as from that of resistance). The numerical language of control is made of codes that mark access to information, or reject it. We no longer find ourselves dealing with the mass/individual pair. Individuals have become “dividuals,” and masses, samples, data, markets, or “banks.” Perhaps it is money that expresses the distinction between the two societies best, since discipline always referred back to minted money that locks gold as numerical standard, while control relates to floating rates of exchange, modulated according to a rate established by a set of standard currencies. The old monetary mole is the animal of the space of enclosure, but the serpent is that of the societies of control. We have passed from one animal to the other, from the mole to the serpent, in the system under which we live, but also in our manner of living and in our relations with others. The disciplinary man was a discontinuous producer of energy, but the man of control is undulatory, in orbit, in a continuous network. Everywhere surfing has already replaced the older sports.
Types of machines are easily matched with each type of society–not that machines are determining, but because they express those social forms capable of generating them and using them. The old societies of sovereignty made use of simple machines–levers, pulleys, clocks; but the recent disciplinary societies equipped themselves with machines involving energy, with the passive danger of entropy and the active danger of sabotage; the societies of control operate with machines of a third type, computers, whose passive danger is jamming and whose active one is piracy or the introduction of viruses. This technological evolution must be, even more profoundly, a mutation of capitalism, an already well-known or familiar mutation that can be summed up as follows: nineteenth-century capitalism is a capitalism of concentration, for production and for property. It therefore erects a factory as a space of enclosure, the capitalist being the owner of the means of production but also, progressively, the owner of other spaces conceived through analogy (the worker’s familial house, the school). As for markets, they are conquered sometimes by specialization, sometimes by colonization, sometimes by lowering the costs of production. But in the present situation, capitalism is no longer involved in production, which it often relegates to the Third World, even for the complex forms of textiles, metallurgy, or oil production. It’s a capitalism of higher-order production. It no-longer buys raw materials and no longer sells the finished products: it buys the finished products or assembles parts. What it wants to sell is services but what it wants to buy is stocks. This is no longer a capitalism for production but for the product, which is to say, for being sold or marketed. Thus is essentially dispersive, and the factory has given way to the corporation. The family, the school, the army, the factory are no longer the distinct analogical spaces that converge towards an owner–state or private power–but coded figures–deformable and transformable–of a single corporation that now has only stockholders. Even art has left the spaces of enclosure in order to enter into the open circuits of the bank. The conquests of the market are made by grabbing control and no longer by disciplinary training, by fixing the exchange rate much more than by lowering costs, by transformation of the product more than by specialization of production. Corruption thereby gains a new power. Marketing has become the center or the “soul” of the corporation. We are taught that corporations have a soul, which is the most terrifying news in the world. The operation of markets is now the instrument of social control and forms the impudent breed of our masters. Control is short-term and of rapid rates of turnover, but also continuous and without limit, while discipline was of long duration, infinite and discontinuous. Man is no longer man enclosed, but man in debt. It is true that capitalism has retained as a constant the extreme poverty of three-quarters of humanity, too poor for debt, too numerous for confinement: control will not only have to deal with erosions of frontiers but with the explosions within shanty towns or ghettos.
III. Program
The conception of a control mechanism, giving the position of any element within an open environment at any given instant (whether animal in a reserve or human in a corporation, as with an electronic collar), is not necessarily one of science fiction. Felix Guattari has imagined a city where one would be able to leave one’s apartment, one’s street, one’s neighborhood, thanks to one’s (dividual) electronic card that raises a given barrier; but the card could just as easily be rejected on a given day or between certain hours; what counts is not the barrier but the computer that tracks each person’s position–licit or illicit–and effects a universal modulation.
The socio-technological study of the mechanisms of control, grasped at their inception, would have to be categorical and to describe what is already in the process of substitution for the disciplinary sites of enclosure, whose crisis is everywhere proclaimed. It may be that older methods, borrowed from the former societies of sovereignty, will return to the fore, but with the necessary modifications. What counts is that we are at the beginning of something. In the prison system: the attempt to find penalties of “substitution,” at least for petty crimes, and the use of electronic collars that force the convicted person to stay at home during certain hours. For the school system: continuous forms of control, and the effect on the school of perpetual training, the corresponding abandonment of all university research, the introduction of the “corporation” at all levels of schooling. For the hospital system: the new medicine “without doctor or patient” that singles out potential sick people and subjects at risk, which in no way attests to individuation–as they say–but substitutes for the individual or numerical body the code of a “dividual” material to be controlled. In the corporate system: new ways of handling money, profits, and humans that no longer pass through the old factory form. These are very small examples, but ones that will allow for better understanding of what is meant by the crisis of the institutions, which is to say, the progressive and dispersed installation of a new system of domination. One of the most important questions will concern the ineptitude of the unions: tied to the whole of their history of struggle against the disciplines or within the spaces of enclosure, will they be able to adapt themselves or will they give way to new forms of resistance against the societies of control? Can we already grasp the rough outlines of the coming forms, capable of threatening the joys of marketing? Many young people strangely boast of being “motivated”; they re-request apprenticeships and permanent training. It’s up to them to discover what they’re being made to serve, just as their elders discovered, not without difficulty, the telos of the disciplines. The coils of a serpent are even more complex that the burrows of a molehill.
L’autre journal, Nr. I, Mai 1990.
Personal comment:
I keep this post in our | rblg survey because it is useful --even so partly questioned-- for us in the context of an ongoing project, Paranoid Shelter (an installation by fabric | ch that will be used in a joint theatrical project with french writer and essayist Eric Sadin, Globale Paranoia). It will be on stage next February at the Comédie de Caen in France.
Friday, September 02. 2011
Via Computed·Blg via big think
by Dominic Basulto
-----
At the Black Hat security conference in Las Vegas, researchers from Carnegie Mellon demonstrated how the same facial recognition technology used to tag Facebook photos could be used to identify random people on the street. This facial recognition technology, when combined with geo-location, could fundamentally change our notions of personal privacy. In Europe, facial recognition technology has already stirred up its share of controversy, with German regulators threatening to sue Facebook up to half-a-million dollars for violating European privacy rules. But it's not only Facebook - both Google (with PittPatt) and Apple (with Polar Rose) are also putting the finishing touches on new facial recognition technologies that could make it easier than ever before to connect our online and offline identities. If the eyes are the window to the soul, then your face is the window to your personal identity.
And it's for that reason that privacy advocates in both Europe and the USA are up in arms about the new facial recognition technology. What seems harmless at first - the ability to identify your friends in photos - could be something much more dangerous in the hands of anyone else other than your friends for one simple reason: your face is the key to linking your online and offline identities. It's one thing for law enforcement officials to have access to this technology, but what if your neighbor suddenly has the ability to snoop on you?
The researchers at Carnegie Mellon showed how a combination of simple technologies - a smart phone, a webcam and a Facebook account - were enough to identify people after only a three-second visual search. Hackers - once they can put together a face and the basics of a personal profile - like a birthday and hometown - they can start piecing together details like your Social Security Number and bank account information.
 And the Carnegie Mellon technology used to show this? You guessed it - it's based on PittPatt (for Pittsburgh Pattern Recognition Technology), which was acquired by Google, meaning that you may soon be hearing the Pitter Patter of small facial recogntion bots following you around any of Google's Web properties. The photo in your Google+ Profile, connected seamlessly to video clips of you from YouTube, effortlessly linked to photos of your family and friends in a Picasa album - all of these could be used to identify you and uncover your private identity. Thankfully, Google is not evil. And the Carnegie Mellon technology used to show this? You guessed it - it's based on PittPatt (for Pittsburgh Pattern Recognition Technology), which was acquired by Google, meaning that you may soon be hearing the Pitter Patter of small facial recogntion bots following you around any of Google's Web properties. The photo in your Google+ Profile, connected seamlessly to video clips of you from YouTube, effortlessly linked to photos of your family and friends in a Picasa album - all of these could be used to identify you and uncover your private identity. Thankfully, Google is not evil.
Forget being fingerprinted, it could be far worse to be Faceprinted. It's like the scene from The Terminator, where Arnold Schwarzenegger is able to identify his targets by employing a futuristic form of facial recognition technology. Well, the future is here.
Imagine a complete stranger taking a photo of you and immediately connecting that photo to every element of your personal identity and using that to stalk you (or your wife or your daughter). It happened to reality TV star Adam Savage - when he uploaded a photo to his Twitter page of his SUV parked outside his home, he didn't realize that it included geo-tagging meta-data. Within hours, people knew the exact location of his home. Or, imagine walking into a store, and the sales floor staff doing a quick visual search using a smart phone camera, finding out what your likes and interests are via Facebook or Google, and then tailoring their sales pitch accordingly. It's targeted advertising, taken to the extreme.
 Which is not to say that everything about facial recognition technology is scary and creepy. Gizmodo ran a great piece explaining all the "advantages" of being recognize onlined. (Yet, two days later, Gizmodo also ran a piece explaining how military spies could track you down almost instantly with facial recognition technology, no matter where you are in the world). Which is not to say that everything about facial recognition technology is scary and creepy. Gizmodo ran a great piece explaining all the "advantages" of being recognize onlined. (Yet, two days later, Gizmodo also ran a piece explaining how military spies could track you down almost instantly with facial recognition technology, no matter where you are in the world).
Which raises the important question: Is Privacy a Right or a Privilege? Now that we're all celebrities in the Internet age, it doesn't take much to extrapolate that soon we'll all have the equivalent of Internet paparazzi incessantly snapping photos of us and intruding into our daily lives. Cookies, spiders, bots and spyware will seem positively Old School by then. The people with money and privilege and clout will be the people who will be able to erect barriers around their personal lives, living behind the digital equivalent of a gated community. The rest of us? We'll live our lives in public.
Personal comment:
Again, this reminds me of this previous "| rblg" post concerning "publicy". And as I mentioned at that time, it could also be useful in the context of a new work we are working on, Paranoid Shelter. There are .
Tuesday, June 21. 2011
Via @ptrckkllr
-----
The "Measured Life" on MIT Tech Review - Could we think of an architecture that "collaborates" with physiological and/or neurological inputs? http://bit.ly/kWL5D8
Personal comment:
Following this article by MIT Technology Review magazine and the previous post on | rblg about "Open Soure Architecture", considering also that architecture is always a way to negotiate/mitigate (a lot or a few) our relation to the now and here (in every sense, both physiological, neurological, visual, cultural, social, etc. --and so far that the "now" can become the "not now" and the "here" the "there"! (mediated experiences)), could we think of a data based architecture (open data from health and RL monitoring --in addition to environmental sensors and online data--) that would collaborate with those health inputs?
Friday, May 27. 2011
Via OWNI.eu
-----
by Yann Leroux
We, the digiboriginals, perceive a state of hostility towards cyberspace that reached a climax at the eG8. The neutrality on which our values are grounded have been strongly challenged under a false pretext. We have reached the point where the Internet must be protected from governments.
We have shaped a province far removed from culture into a vibrant city, whose wealth benefits all. We built cyberspace. We have built it bit after bit, manifesto after manifesto, lolcat after lolcat. There, we have our cathedrals and our bazaars. We have invented worlds, networks of social and informational systems that are second to none.
The cyberspace is not a new space to conquer. It does not exist to be colonized nor civilized.
The cyberspace is a space of civilization, and has been since its founding. This is an undeniable fact, because it is built and inhabited by men and women.
The Internet does not discriminate between Joe and Mark. It is not an egalitarian space. It breaks through barriers, yet these barriers were socially constructed. They are not in the network’s architecture.
We oppose the cyberspace changing into a space of surveillance.
We oppose states abandoning the protections they own their citizens.
We oppose states violating the right to privacy in the cyberspace.
We oppose modifying cyberspace’s architecture.
We oppose outdated copyright models becoming the norm for everything we share.
At a time when the end of humanity becomes a tangible hypothesis, more than ever we need a commons space where we can gather and solve the issues at hand. The cyberspace makes Tahrir squares and Puerta del Sol possible.
We cannot afford to lose our future – it is time to defend it.
Friday, May 06. 2011
Via MIT Technology Review
-----
The data entered by millions of social-network users could be turned into revealing infographics.
By Christopher Mims
Ever wondered just how much coffee you drank last year, or which movies you saw, and when? New Web and mobile apps make it possible to track, and visualize, this personal information graphically, and the trend could be set to expand dramatically.
This is because Facebook recently acquired one of the leading personal-data-tracking mobile apps and hired its creators. The social-networking giant could be gearing up to offer users ways to chart the minutiae of their lives with personalized infographics.
Nick Felton and Ryan Case, two New York-based designers, have pioneered turning the mundane contours of an everyday life into a kind of visual narrative. Each year, Felton publishes an "annual report" on his own life: an infographic that charts out his habits and lifestyle in great detail.
Felton and Case have also created a mobile app, called Daytum, that lets users gather personal data and represent it using infographics. Daytum already has 80,000 users, whose pages provide a detailed snapshot of everything from coffee drinking habits to baseball stadium visits. The app gives users the ability to easily record their own information, whatever it might be, and display it in an attractive manner, whether or not they are a designer.
Daytum is part of a larger trend in tracking personal information. But traditional personal tracking applications tend to revolve around medical data, sleep schedules, and the like. In Felton's creative visualizations, even something as mundane as how many concerts he attended in the past year becomes a kind of art. "I think there's storytelling potential in data," he says.
Felton says he can't talk about what he'll be doing at Facebook, but says, "Clearly, companies like Facebook recognize the value of the kind of work we were doing."
 |
This page from Felton's 2009 annual report shows every notable social encounter he had.
Credit: Nicholas Felton |
At Facebook, users already engage in countless acts of data entry, so it's possible that the data Felton will be visualizing will already be available. Automated data gathering through smart phones—especially location data—provides even more data to mine.
Eventually—with users' permission—this kind of personal information could be mined by marketers and advertisers. Ted Morgan, CEO of the geolocation software company Skyhook, compares the trend to the way advertisers currently track some TV viewers' watching habits. In the future, he says, tracking data will be "like a Nielsen rating box for your life. It will track where you go and what you do. [Advertisers are] going to pay people to do this."
One company is already exploring this possibility. Locately offers users promotions and discounts if they agree to opt in to its mobile data-gathering network. This lets the company gather data on where people go, what they do, and what they buy; the company sells that data to businesses who want to use it for market research and advertising.
Gathering detailed personal data can produce surprising insights, says Felton. "The way people describe themselves is not really in line with their true behavior," he notes. For example, users who track what TV shows they actually watch may find that they spend more time on shows they don't identify as their favorites.
Perhaps this could lead to a whole new kind of friend discovery, one based not on our expressed interests, but on our actual interests. Picture a beefed-up version of Facebook's "people you might also know" feature informed not just by who you're connected to, but what behavior you have in common.
"It could be shared affinities that are not recognized by either [party]," says Felton. The downside, of course, is that people who are a lot like us often drive us crazy. "You might hate them," says Felton. "Isn't that part of what annoys us about our families?"
Copyright Technology Review 2011.
Wednesday, April 27. 2011
Via The Funanbulist
-----
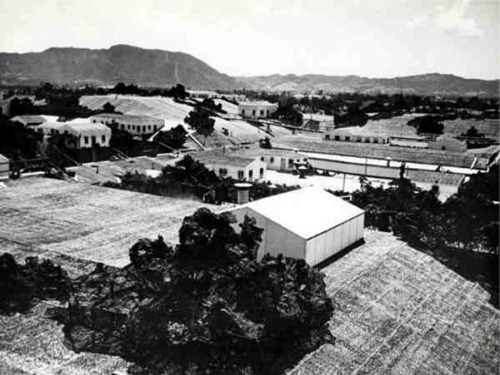
by Léopold Lambert
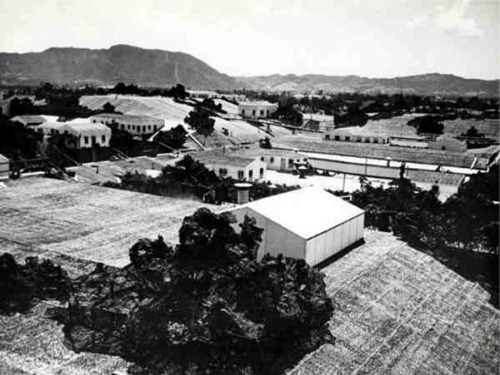
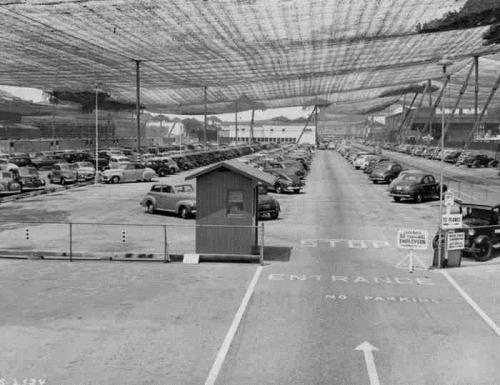
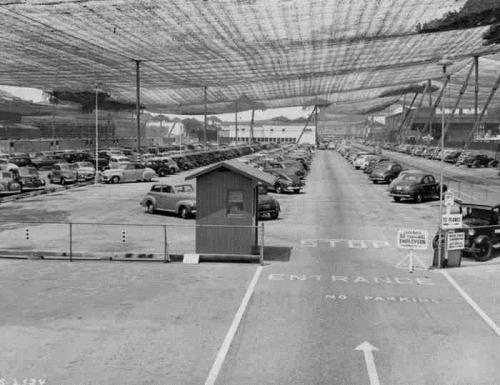
In 1942, after the United States entered the second world war and fearing the Japanese threat on the Pacific coast, an entire aircraft plant and airport -the Lockheed Burbank- has been camouflaged to escape from sight to potential Japanese airplanes. It is interesting to observe that, in order to do so, the US army had to ask for the help of Hollywood studios -WWII is probably the beginning of a long history of exchanges between Hollywood and the US Army- to make this industrial landscape appearing as a piece of suburbia. The very vast aircraft plant was therefore obliged to function under a porous canopy from which was emerging here and there, some chimneys disguised in trees or fountains.
Thanks Martial. (see more on amusingplanet)




Thursday, April 21. 2011
Via MIT Technology Review
-----
An experimental system would tighten the limits on information provided to websites.
By Erica Naone
 |
| Credit: iStockphoto |
Today, many websites ask users to take a devil's deal: share personal information in exchange for receiving useful personalized services. New research from Microsoft, which will be presented at the IEEE Symposium on Security and Privacy in May, suggests the development of a Web browser and associated protocols that could strengthen the user's hand in this exchange. Called RePriv, the system mines a user's behavior via a Web browser but controls how the resulting information is released to websites that want to offer personalized services, such as a shopping site that automatically knows users' interests.
"The browser knows more about the user's behavior than any individual site," says Ben Livshits, a researcher at Microsoft who was involved with the work. He and colleagues realized that the browser could therefore offer a better way to track user behavior, while it also protects the information that is collected, because users won't have to give away as much of their data to every site they visit.
The RePriv browser tracks a user's behavior to identify a list of his or her top interests, as well as the level of attention devoted to each. When the user visits a site that wants to offer personalization, a pop-up window will describe the type of information the site is asking for and give the user the option of allowing the exchange or not. Whatever the user decides, the site doesn't get specific information about what the user has been doing—instead, it sees the interest information RePriv has collected.
Livshits explains that a news site could use RePriv to personalize a user's view of the front page. The researchers built a demonstration based on the New York Times website. It reorders the home page to reflect the user's top interests, also taking into account data collected from social sites such as Digg that suggests which stories are most popular within different categories.
Livshits admits that RePriv still gives sites some data about users. But he maintains that the user remains aware and in control. He adds that cookies and other existing tracking techniques sites already collect far more user data than RePriv supplies.
The researchers also developed a way for third parties to extend RePriv's capabilities. They built a demonstration browser extension that tracks a user's interactions with Netflix to collect more detailed data about that person's movie preferences. The extension could be used by a site such as Fandango to personalize the movie information it presents—again, with user permission.
"There is a clear tension between privacy and personalized technologies, including recommendations and targeted ads," says Elie Bursztein, a researcher at the Stanford Security Laboratory, who is developing an extension for the Chrome Web browser that enables more private browsing. "Putting the user in control by moving personalization into the browser offers a new way forward," he says.
"In the medium term, RePriv could provide an attractive interface for service providers that will dissuade them from taking more abusive approaches to customization," says Ari Juels, chief scientist and director of RSA Laboratories, a corporate research center.
Juels says RePriv is generally well engineered and well thought out, but he worries that the tool goes against "the general migration of data and functionality to the cloud." Many services, such as Facebook, now store information in the cloud, and RePriv wouldn't be able to get at data there—an omission that could hobble the system, he points out.
Juels is also concerned that most people would be permissive about the information they allow RePriv to release, and he believes many sites would exploit this. And he points out that websites with a substantial competitive advantage in the huge consumer-preference databases they maintain would likely resist such technology. "RePriv levels the playing field," he says. "This may be good for privacy, but it will leave service providers hungry." Therefore, he thinks, big players will be reluctant to cooperate with a system like this.
Livshits argues that some companies could use these characteristics of RePriv to their advantage. He says the system could appeal to new services, which struggle to give users a personalized experience the first time they visit a site. And larger sites might welcome the opportunity to get user data from across a person's browsing experience, rather than only from when the user visits their site. Livshits believes they might be willing to use the system and protect user privacy in exchange.
Copyright Technology Review 2011.
|