Tuesday, January 12. 2010
Vie privée : le point de vue des petits cons
Nombreux sont ceux qui pensent que les jeunes internautes ont perdu toute notion de vie privée. Impudiques, voire exhibitionnistes, ils ne feraient plus la différence entre vie publique et vie privée. Et si, a contrario, ils ne faisaient qu’appliquer à l’internet ce que leurs grands-parents ont conquis, en terme de libertés, dans la société ?
Dans “La vie privée, un problème de vieux cons ?“, je dressais un parallèle entre la façon désinhibée qu’ont les jeunes internautes de se dévoiler sur le Net et la révolution sexuelle, et me demandais si ceux qui sont gênés par cette façon décomplexée de s’exprimer ne seraient pas un peu coincés.
Au-delà des problèmes d’inhibition des “vieux cons“, il est difficile d’aborder la question sans essayer de regarder de plus près comment, et pourquoi, les jeunes qui ont grandi avec le Net évoquent ainsi leurs vies privées dans des espaces publics. Une démarche somme toute… “rock’n roll” que n’auraient peut-être pas renié nos (grands) parents, en moins rebelle cependant.
Pour Josh Freed, célèbre éditorialiste canadien, c’est la plus importante fracture générationelle depuis des décennies, qu’il résume ainsi : d’un côté, nous avons la “génération des parents“, de l’autre, la “génération des transparents” :
L’une cherche à protéger sa vie privée de manière quasi-obsessionnelle, l’autre sait à peine ce qu’est la “vie privée“.
La génération des transparents a passé toute sa vie sur scène, depuis que leurs embryons ont été filmés par une échographie alors qu’ils n’avaient que huit semaines… de gestation. Ils adorent partager leurs expériences avec la planète entière sur MySpace, Facebook ou Twitter et pour eux, Big Brother est un reality show.
La génération des parents voit cette transparence comme un cauchemar. Elle a grandi à l’ombre de Mac Carthy et des espions de la CIA, et est plutôt paranoïaque dès qu’il s’agit de partager des données personnelles, de passer à la banque en ligne ou même d’acheter un livre sur Amazon.
Josh Freed raconte ainsi qu’à peine rentré de vacances, son fils mit en ligne toutes les photos de famille, en maillot de bain, avant que sa mère, l’apprenant, ne les en retire “plus rapidement qu’un censeur du gouvernement chinois“.
Comme le souligne Elizabeth Denham, commissaire adjointe à la protection de la vie privée du Canada, habitués à être regardés, filmés, et photographiés, avant même que d’être nés, les jeunes se retrouvent aujourd’hui à “se demander si les choses se passent réellement quand personne ne les regarde“.
En 2006 déjà, danah boyd, l’une des plus fines observatrices de ce que font les jeunes sur le Net, remarquait elle aussi que les adolescents étaient d’autant plus “blasés” par la notion de vie privée, et qu’ils avaient d’autant plus de mal à percevoir les risques posés par la “société de surveillance“, qu’ils ont eux-mêmes grandi en étant constamment surveillés par ceux qui, parents et enseignants notamment, affectent, dirigent ou contrôlent directement leur vie privée ? :
Leur panoptique personnel (administré par des personnes qu’ils connaissent et voient quotidiennement) est bien plus intrusif, menaçant, direct et traumatique que ne pourraient l’être des panoptiques gouvernementaux ou contrôlés par des entreprises privées.
L’érosion de la vie privée commence à la maison, pas au niveau gouvernemental ou marchand. Et tant que nous ne trouverons pas un moyen d’offrir plus de vie privée à ces jeunes, dans leur vie intime, ils n’aspireront pas à plus de vie privée dans leurs vies publiques.
La vie privée ? Une course à l’armement
Citant Jürgen Habermas et son essai sur L’espace public : archéologie de la publicité comme dimension constitutive de la société bourgeoise, ainsi que la notion de “contre-publics” (regroupements sociaux formés en opposition aux discours et aux intérêts de la sphère publique officielle) du théoricien du mouvement queer et des questions de genre Michael Warner, danah boyd rappelle que la vie privée est un privilège acquis il n’y a pas si longtemps que cela, et partagé essentiellement par les hétérosexuels blancs de sexe masculin…
Et si la déclaration universelle des droits de l’homme affirme bien, dans son article 12, que “nul ne sera l’objet d’immixtions arbitraires dans sa vie privée, sa famille, son domicile ou sa correspondance, ni d’atteintes à son honneur et à sa réputation“, force est de constater qu’il ne s’applique guère aux mineurs :
Votre enfant a peut-être sa propre chambre dotée d’une porte qui ferme à clef, et de son propre ordinateur. Mais il n’a pas d’espace privé.
Et c’est pour cela que les enfants se ruent dans l’arène publique pour se libérer de la façon qu’ont leurs parents et administrations scolaires de leur dicter leur façon de se mouvoir et de communiquer.
Dans l’arène publique, ou via une interface technique. Le New York Times raconte ainsi l’étonnement du président de Walt Disney qui, convoyant sa fille et deux de ses amies en voiture, s’étonnait de ne pas les entendre parler, mais de la voir taper des SMS :
“- Tes amies sont là, ça ne se fait pas !
- Mais papa, nous sommes en train de nous écrire, je ne veux pas que tu entendes ce que j’ai à leur dire !”
danah boyd, pour qui la notion de vie privée renvoie à ces moments où l’on a le sentiment de contrôler la façon -et le moment- où l’on peut communiquer avec quelqu’un en particulier, qualifie ainsi d’espaces interstitiels ces moments “volés” dont ils profitent pour communiquer, en toute confidentialité.
Pour elle, la parentalité a, ces dernières années, été de plus en plus associée au fait de surveiller ses enfants. Au point qu’on assisterait à une “course à l’armement entre la surveillance parentale et l’utilisation des technologies pour protéger sa vie privée” :
“Les parents surveillent l’ordinateur de leurs enfants ? Les enfants s’envoient des textos. Et après, on fait quoi ? Combien de temps faudra-t-il attendre avant que les parents ne réclament aux opérateurs de télécommunication la transcription de tout ce qu’ils font et partagent ?
Nous sommes au beau milieu d’une guerre à la vie privée qui va bien plus loin que l’opposition entre “où est ma vie privée ?” et “les enfants sont tellement impudiques“. La distinction même entre vie publique et vie privée s’en trouve bousculée.
Alors que les enfants cherchent à se rendre invisibles de ceux qui disposent d’un pouvoir direct sur eux (parents, enseignants, etc.), ils s’exposent joyeusement auprès de leurs pairs.”
danah boyd note d’ailleurs dans sa thèse, Sortie du contexte : la sociabilité des adolescents américains dans les espaces publics en réseaux (.pdf), que lorsqu’on les interroge, les adolescents déclarent systématiquement qu’ils préféreraient des espaces physiques plutôt que virtuels de socialisation, mais sans contrôle parental…
Au final, et alors que les adultes doivent réapprendre à se comporter en public, du fait des changements indus par les technologies, les ados, eux, apprennent à se comporter en public grâce aux (et avec les) technologies.
Contrairement à ce que l’on entend souvent, ils n’ont pas particulièrement pour autant de facilités “naturelles” vis-à-vis des technologies, mais c’est effectivement souvent par leur truchement qu’ils apprennent, dans un monde d’adultes, à vivre ensemble, entre eux, et à être un peu seuls, tout simplement. Ce qui leur offre de nombreuses (et nouvelles) libertés mais aussi, et invariablement, angoisse leurs parents en particulier, et les adultes en général.
Une génération “rock’n roll”…
En 2007, la journaliste Emily Nussbaum (compagne de Clive Thompson, dont nous avions déjà évoqué le Nouveau Monde de l’intimité numérique) avait tiré un magnifique portrait de ces enfants du numérique, qui ont grandi de concert avec la numérisation de la société, et qui ont une toute autre approche de la vie privée.
Son article, intitulé “Say everything” (tout dire, en VF), et paru en février 2007 dans le New York Magazine, devrait être inscrit au programme de formation continue de tous les enseignants (et, bien évidemment, des parents). Le début est volontairement caricatural, la suite nettement plus stimulante :
“Les enfants d’aujourd’hui n’ont aucune pudeur, sentiment de honte, ni de vie privée. Ce sont des frimeurs, des putains de la célébrité, de petits vauriens pornographiques qui mettent en ligne leurs journaux intimes, numéros de téléphone, poésies stupides et photos cochonnes.
Ils ont plus d’amis virtuels que d’amis réels. Ils se parlent par messages instantanés et illettrés. Ils ne s’intéressent qu’à l’attention qu’ils peuvent engendrer, et pourtant, ils sont au degré zéro de la concentration, comme des colibris voletant d’une scène virtuelle à l’autre.”
Pour mieux comprendre ce dont il retourne, elle a été voir Clay Shirky, qui observe ce phénomène depuis qu’il a découvert le Net, en 1993, et qui enseigne le “climat social” au programme des télécommunications interactives de la New York University. Sa théorie a tout de la querelle des anciens et des modernes, et repose sur le postulat que nos comportements relèvent moins de la moralité que de la chronologie :
“Chaque fois que les jeunes sont autorisés à se livrer à des activités qui échappent aux anciens, ces derniers s’en trouvent amers. Qu’avions-nous ? Des centres commerciaux et des parkings ? Ce n’est rien en comparaison de ce à quoi ils ont accès, et nous en sommes malades.
Au-delà d’un certain âge, mettons 30 ans, il apparaît toujours surprenant que des pans entiers de notre vie puissent se retrouver en ligne. Mais ce n’est pas quelque chose que ceux qui ont moins de 30 ans ont à désapprendre. Si nous n’agissions pas comme eux, c’est parce que nous n’en avions pas la possibilité.”
Vers la créolisation des médias
Si, pour les ados, il peut sembler plus important d’être vu que d’avoir du talent, on aurait tort, pour autant, de croire que leur horizon se limite à la télé-réalité et à la “peoplisation“, souligne Emily Nussbaum :
“Nous discutons de quelque chose de plus radical parce que plus ordinaire : nous sommes au centre d’une vaste expérimentation psychologique, qui commence à peine à produire des résultats.
Un nombre considérable de jeunes gens partagent publiquement plus de données personnelles qu’aucune personne plus âgée ne l’a jamais fait, et ils semblent pourtant mystérieusement en bonne santé et normaux, et dotés d’une définition totalement différente de la vie privée.
De leur point de vue, le narcissisme, c’est la prudence extrême de l’ancienne génération. Comme le résume Kitty : oui, je suis nue sur l’Internet, mais j’ai toujours dit que je n’y mettrai jamais rien que je ne voudrais pas que ma mère puisse voir. Qu’est-ce que je risque ? Que quelqu’un retrouve ma photo dans 20 ans ? Autant faire de sorte qu’il s’agisse d’une belle photo !”
Filmés avant même que d’être nés, placés sous constante surveillance depuis par ceux qui les aiment ou sont chargés de les éduquer, ils se sont fait à l’idée que la vie privée est une illusion : vidéosurveillance, traçabilité des communications et paiements bancaires… la dématérialisation des procédures, et la numérisation de la société, font que nos traces sont dorénavant enregistrées et stockées, souvent par des entreprises privées, et généralement au nom de la loi.
“Il serait peut-être donc temps d’envisager la possibilité que ces jeunes, qui agissent comme si la vie privée n’existait pas, sont de fait des personnes saines, et que les plus aliénés ne sont pas ceux qu’on croit.
Pour quelqu’un comme moi, qui a grandi en fermant à clef mon journal intime, ça risque d’être difficile à accepter. Mais dans les circonstances actuelles, une attitude de déni consistant à garder les choses pour soi n’est peut-être pas très noble.
C’est peut-être un artefact, vieillot et naïf, comme de croire que la virginité rend les jeunes filles pures. Mais ceux qui ont grandi “en se montrant” ont aussi découvert que les bénéfices de la transparence valaient la peine d’être tentés.”
Clay Shirky décrit cette fracture générationnelle en comparant le sabir, créé par des gens apprenant à communiquer en assemblant des mots et expressions de différentes langues, et le créole, qui est la langue parlée par les enfants de ceux qui parlent le sabir, et qui y imposent des règles et structures cohérentes.
Pour lui, nous assistons aujourd’hui à la “créolisation des médias, et je ne pense pas qu’il s’agisse d’une métaphore. Je pense que cela peut aussi entraîner de réels changements neurologiques” :
“Et quid de toutes ces choses que nous racontaient nos aînés au sujet du rock’n roll ? Ils ont tout déchiré. Le métissage, les adolescents libres de faire ce qu’ils veulent, la fin du mariage !”
Un nouveau romantisme
Cherchant à mieux appréhender ce qui a changé, Emily Nussbaum observe trois principales restructurations propres à ces individus sociaux, résumées par François Guité, enseignant et spécialiste de l’internet, comme suit :
1. Ils se perçoivent comme ayant un auditoire. C’est la conséquence logique d’une génération MySpace qui ne craint pas de s’afficher en ligne et de publier ses états d’âme.
2. Ils ont archivé leur adolescence. Tout y est : textes, photos, vidéos, musique. Leur mémoire est non seulement consignée dans un album numérique, mais elle est partagée.
3. Leur carapace est plus épaisse que la nôtre. Que ce soit dans la messagerie instantanée ou les blogues (le courrier électronique est une technologie de dinosaures), ils sont habitués au flaming (engueulades et insultes en ligne, Ndlr). Cela explique sans doute le peu de cas qu’ils font de « ta gueule! » et « va chier! ».
Pour eux, il ne sert à rien d’aller à une soirée si ce n’est pas, aussi, pour en faire des photos et les partager, ce en quoi ils ne sont pas très différents des générations d’avant, qui gardaient en Super8, VHS ou en photos papier les traces de leurs histoires.
La différence est que ces documents sont souvent partagés sur des réseaux sociaux, et non gardés chez soi, pour soi. Pour autant, cette “extimité” relève moins de l’exhibitionnisme qu’elle ne dépend des outils qu’ils utilisent (il est plus simple et moins coûteux de mettre ses photos en ligne que de les développer sur support papier) mais aussi voire surtout d’une forme de romantisme qui ne relève pas que de la crise d’adolescence, comme l’explique Caitlin Oppermann, 17 ans, qui avait commencé à bloguer à l’âge de 12 ans :
“Si je ne l’efface pas, je serai toujours là. Ma génération aura accès à toute son histoire, nous pouvons documenter les choses si facilement. Je suis très sentimentale, je suis sûre que cela a quelque chose à voir avec ça.”
Son ami Jakob Lodwick, co-fondateur de Vimeo.com (qui est à YouTube ce que la DVD est au VHS, en -gros- résumé) et de CollegeHumor.com (une sorte de Groland US, en bien plus geek), partage lui aussi cette vision romantique :
“En me mettant en ligne, j’ai reçu un peu d’attention, et je me sentais bien; c’était un réel retour sur investissement (…) Je filmais ce que je voyais et ce qui résonnait en moi. Je ne leur montrais pas ce que c’était que de sortir avec moi, mais ce que c’était que d’être moi.”
Pour Jackson, note Emily Nussbaum, l’internet est un espace où le fait de se montrer les seins nus n’a pas grande importance, mais où tout un chacun peut se faire connaître, gagner de l’attention et de la réputation, en se montrant sous un jour un peu plus vulnérable. Dans le même temps, ceux qui y agissent comme des porcs seront aussi perçus comme des porcs.
Mais quid des pervers ?
Ils sont certes plus ou moins conscients que ces documents et traces pourraient leur être un jour reprochés, par un employeur notamment -sans parler de la façon qu’auront leurs propres enfants de découvrir ces souvenirs, et les quelques frasques qu’ils n’auront pas effacées.
Mais le fait de s’exposer est d’abord et avant tout, comme dans la rue ou la cour de récréation, un moyen d’entrer en contact avec les autres, ou de maintenir et prolonger ce contact, de trouver un(e) petit(e) ami(e), d’être félicité pour la qualité des photographies, voire d’être repéré par un futur employeur… pourquoi dès lors faudrait-il s’en priver et ne se focaliser que sur le (faible) risque associé ? Jusqu’à preuve du contraire, on court plus de risque en sortant de chez soi, à pied ou en voiture, qu’en allant sur Facebook ou Flickr !
Depuis qu’ils communiquent, ils sont habitués à être confrontés à ce que danah boyd qualifie d’”audiences invisibles“, à savoir tous ceux qui, sans être pour autant leurs “amis” à qui sont destinés, a priori, ce qu’ils mettent en ligne, n’en peuvent pas moins en devenir les lecteurs, critiques ou laudateurs… et donc aussi les “juger“, plutôt que seulement les lire ou les regarder.
Ils ont ainsi appris à moduler leur ton pour s’adresser à ces différents types d’auditeurs, sachant également qu’un message instantané ou un email peuvent être copiés/collés et qu’un “chat” peut être archivé : “cette façon de communiquer oblige les gens à être constamment conscient du fait que tout ce qu’ils publient pourra, et sera, retenu contre eux“.
En ce sens, les adolescents sont confrontés aux mêmes types de problèmes et précautions que les hommes politiques et les “people” : ils sont, eux aussi, devenus -au sens littéral- des personnalités publiques. A ce titre, ils ont aussi adopté les mêmes réflexes que les célébrités, et savent donc qu’il vaut mieux tenter de profiter de l’attention de ceux qui s’intéressent à vous, mais aussi devancer l’appel en contrôlant votre communication plutôt que de voir quelqu’un d’autre le faire à votre place, et donc risquer d’en faire les frais.
A l’instar des personnalités publiques, les ados doivent également apprendre à être jugés, mal compris, caricaturés, critiqués… Le sexe n’étant pas l’apanage des célébrités, certaines jeunes filles anonymes ont ainsi elles aussi droit à “leur” sex-tape, mise en ligne par leur ex-petit ami généralement, profitant du fait que 10 à 20% des jeunes reconnaissent avoir déjà envoyé des photos (ou “sextos“) d’eux, nus, sur le Net ou via leurs téléphones mobiles.
Mises à nues sur les réseaux, certaines décident de s’en déconnecter, pour ne plus risquer d’être confrontées à cette “mauvaise réputation” qui leur collerait au Net. D’autres pourraient décider d’en profiter, pour faire parler d’elles, ou gagner de l’argent, mais cela semble encore rester l’apanage des seuls “people” type Paris Hilton. D’autres enfin décident plus simplement que le plus important, c’est d’apprendre à vivre avec, comme cela se passe à l’occasion de n’importe quel autre type d’agression, et de garder sa dignité.
Il n’est pas inutile, cela dit, de rappeler que le nombre de violences sexuelles dues à l’exposition de soi sur le Net est infime en comparaison du nombre d’agressions sexuelles (notamment dans les sphères intra-familiales) auxquelles les jeunes peuvent être confrontés “IRL” (dans “leur vraie vie“, pour reprendre l’acronyme consacré sur le Net).
Par contre, elles font l’objet de toutes les attentions médiatiques, au point de devenir un nouveau “marronnier journalistique” habilement exploité par ceux qui voient d’un mauvais oeil ces nouvelles libertés que s’arrogent les jeunes ou qui, faute de savoir utiliser le Net ou d’en comprendre les tenants et aboutissants, ont peur des réseaux, tout simplement.
Emily Nussbaum note ainsi justement que la quasi-totalité des personnes de plus de 40 ans, dès lors qu’on leur parle de l’internet, sont littéralement obsédés par le fait qu’il serait infesté de pédophiles, et qu’elles n’ont qu’une idée en tête : “Mais quid des pervers ?“… Les adolescents sont habitués à cette vision particulièrement anxiogène et caricaturale de l’univers dans lequel ils vivent, et préfèrent généralement en rigoler, ce qui ne les empêche aucunement de penser que ceux qui caricaturent ainsi le Net, et donc leur vie, ne sont jamais que des “vieux cons“…
Au-delà de cette diabolisation qui ne fait qu’entraver ou retarder le fait d’entrer de plain-pied dans la société de l’information, danah boyd souligne que cette peur de l’espace public qu’est le Net, et ce désir de contrôler la vie des adolescents, empêchent les parents de donner à leurs enfants les outils susceptibles de les aider à aborder leur transition vers le monde des adultes, et peut s’avérer contre-productif : “les restrictions et mesures de contrôle maximum infantilisent les adolescents, les rendant plus dépendants, voire haineux, des adultes et de leur monde“.
Il faut savoir choisir son camp
GenderIT.org, site créé par le réseau féministe de l’Association pour le progrès des communications (APC) (voir Prohibition 2.0 : qu’est-ce qu’un contenu préjudiciable ?), s’en est largement fait l’écho à l’occasion de sa couverture du Forum de la gouvernance Internet (IGF) des Nations Unies qui s’est tenu à Sharm El Sheikh en novembre 2009.
On aurait pu attendre de la table ronde consacrée à la protection et la sécurité des enfants sur l’internet qu’elle mette en avant, classiquement, mesures de filtrage gouvernemental, et contrôle parental.
A contrario, Dorothy Attwood, vice-présidente des politiques publiques et responsable des questions de vie privée chez AT&T, y déclara que la maltraitance des enfants et la violation de la vie privée avaient ceci de similaires qu’elles ne peuvent pas être réglées par un contrôle accru des flux d’information : “bloquer et contrôler l’information ne sont que des moyens fractionnés de traiter le problème, la solution ne peut pas consister à ajouter de nouveaux contrôles parentaux“.
Pour elle, apprendre à gérer ses données et à “orienter” son identité en ligne sont des compétences essentielles que les enfants doivent apprendre dès qu’ils abordent l’internet : “nous devons tous connaître nos responsabilités et nos droits dans les espaces en ligne“. Et pour cela, mieux vaut être créatif plutôt que menaçant, proposer aux enfants des jeux et usages tirant les technologies (et leurs usages) vers le haut, plutôt que de les menacer, leur faire peur, ou chercher à les contrôler.
Alors que les médias agitent régulièrement le chiffon rouge du “sexting” (voir “Le sexting, c’est (nor)mal“), un autre intervenant déclarait, lui, que “les jeunes en sont vraiment blasés“, témoignant bien du décalage existant entre la perception fantasmatique des “adultes” et la réalité de ce que vivent les jeunes sur l’Internet, comme l’écrit Maya Ganesh, jeune journaliste de GenderIT :
“Pourquoi les responsables n’écoutent-ils pas les enfants au lieu de se contenter d’en parler ? Pourquoi n’a-t-on pas entendu la perspective des jeunes et pourquoi n’y avait-il pas de représentants des jeunes à ce panel ?
Si les jeunes sont effectivement blasés au sujet du sexting ou excités par les possibilités sexuelles en ligne (les jeunes de chaque génération se sont-ils pas excités par ces possibilités ?), pourquoi les adultes ne peuvent-ils pas le comprendre plutôt que de donner une image générale de victimisation à la sexualité des enfants ?
Alors que la pornographie en ligne peut faire courir un danger aux enfants, le risque le plus important n’est-il pas celui des abus sexuels à la maison par des adultes connus ? Ne risque t-on pas de jeter le bébé avec l’eau du bain en créant ce genre de binarisation ? Pourquoi les risques en ligne et hors ligne sont-ils séparés ?”
Wieke Vink, 18 ans, membre de la Youth Coalition, une ONG internationale réunissant des jeunes de 15 à 29 ans militant pour le droit à la sexualité et à la reproduction des jeunes, ne cache pas, elle non plus, sa consternation devant tant d’infantilisation :
“Quand il y a un problème de connexion internet à la maison, ce ne sont pas mes grands-parents qui le réparent, pas plus que mon père ni ma mère. C’est mon petit ami. Ce sont mes frères. C’est moi. Nous sommes la première génération à avoir grandi à l’ère numérique, dans un vaste monde en réseau (”world wide web” en VO) où Wikipedia est notre bibliothèque, et Skype notre téléphone.
En matière d’Internet, ce ne sont pas nécessairement les parents qui éduquent leurs enfants, mais nous qui leur expliquons ce qu’est YouTube ou Facebook. Nous devons reconnaître que l’Internet est un endroit où les gens se réunissent, partagent et se connectent – et les jeunes sont à l’avant-garde de tout cela.
J’étais donc ravi de voir que l’IGF consacraient nombre de ses panels aux questions relatives aux enfants et aux jeunes, jusqu’à ce que je découvre que les ateliers sur la protection des droits des enfants n’évoquaient quasi-exclusivement que les problèmes tels que les abus sexuels, et que les panelistes avaient tous plus de 50 ans.
Comment se fait-il que la majeure partie des débats au sujet de l’internet et de la sexualité sont empreints de négativité, truffés de mots tels que “filtrage, pédo-pornographie et contenus obscènes” ?
Les jeunes, tout comme n’importe quels autres êtres humains, sont curieux dès qu’il s’agit de sexualité. Et laissez-moi vous dire qu’il y a beaucoup de sexe sur le Net -tout comme il y avait probablement un exemplaire de Playboy sous le lit de mon père. Et c’est très bien. C’est normal. C’est naturel. C’est sain.”
Relatant deux autres tables rondes de l’IGF, sur la vie privée et la gouvernance de l’Internet, Jac SM Kee, artiste et féministe malaysienne responsable de TakeBackTheTech (”Réapproprie-toi la technologie!“), campagne de l’APC incitant “à prendre le contrôle de la technologie pour mettre fin à la violence à l’égard des femmes“, note ainsi que la situation pourrait bien s’inverser :
“Où est le problème? Un exemple a été donné lors de la séance d’hier au sujet d’une enseignante stagiaire qui a placé sur un site de réseautage social une photo d’elle-même tenant une tasse en plastique avec la légende « pirate ivre ». Par la suite, elle n’a pas pu trouver un emploi comme enseignante car, surprise, ils ont tapé son nom sur Google, ont trouvé la photo et ont porté un jugement. Le dernier point est important, car comme l’a fait remarquer Wolfgang Kleinwaechter (professeur à l’université d’Aarhus au Danemark, et expert reconnu des questions de régulation de l’internet, ndlr), les normes changent.
Ceux qui prendront les décisions à l’avenir seront des gens élevés avec les plateformes de réseautage social. Ils penseront peut-être que le fait de ne pas avoir une photo de vous quelque part lorsque vous étiez jeune est une bonne raison de ne pas vous engager. Il ne faut donc pas prendre ces leçons trop au pied de la lettre.
J’ai bien aimé cet argument car il complique une hypothèse en reconnaissant que les enfants ont une responsabilité et un pouvoir – ils sont plus que des victimes sans défense qui ont besoin de protection ou « d’éducation ».
Wolfgang a parlé du fait que les données personnelles constituent une identité et que chacun a la responsabilité de gérer sa propre identité. C’est un bien qui nous appartient et ne peut pas appartenir à quelqu’un d’autre, même si ce bien est stocké ou situé ailleurs. Il incombe donc à chacun de décider de ce qu’il faut faire de son identité, qui ne peut pas être déléguée à quelqu’un d’autre, comme l’État (par la régulation) ou une entité privée (par des contrats ou l’application de solutions technologiques). (…)
La capacité d’exercer autant de contrôle que possible sur mes données personnelles est l’aspect le plus fondamental des approches qui seront adoptées pour protéger la vie privée. Si je ne peux pas contrôler ce qui arrive à mon corps, je n’ai pas de « droit à la vie privée ».”
Tout comme on ne peut empêcher les adolescents d’avoir leur propre sexualité, il est vain de chercher à vouloir les empêcher de s’ébattre sur le Net. Et de même que les cours d’éducation sexuelle ne se limitent pas à l’évocation des MST, du sida, des agressions sexuelles et des grossesses non désirées, il serait bon de commencer à envisager la possibilité de ne plus ni diaboliser le Net, ni d’infantiliser les internautes adolescents (d’autant qu’ils en savent souvent bien plus que les adultes).
La question de savoir à quoi le Net peut bien servir ne se pose pas pour eux : leurs amis sont connectés, c’est plutôt marrant, il y a plein de choses à y faire et à y apprendre qu’on ne trouve pas ailleurs, ou qu’on ne peut pas faire autrement, c’est du spectacle, mais aussi de la vie en société, voire en communauté, on peut s’y exprimer librement, et être entendu, écouté, commenté…
D’ailleurs, pour Emily Nussbaum, la question est moins de savoir s’ils ont raison, ou non : “bien sûr, tous les changements sociaux entraînent des dommages collatéraux. Mais la vraie question est, comme avec toute révolution, de savoir choisir son camp.”
Monday, January 04. 2010
Response to 'Secrecy, Privacy, Publicy' Post
A large surge of interest in the ideas driving yesterday's 'Secrecy, Privacy, Publicy' post (see below). Erick Shonfeld of Techcrunch jumped right in:
It used to be that we lived in private and chose to make parts of our lives public. Now that is being turned on its head. We live in public, like the movie says
(except via micro-signals not 24-7 video self-surveillance), and choose what parts of our lives to keep private. Public is the new default.
Stowe Boyd, along with others before him
, calls this new state of exposure “publicy” (as opposed to privacy or secrecy). He writes:
The idea of publicy is no more than this: rather than concealing things, and limiting access to those explicitly invited, tools based on publicy default to things being open and with open access.
I don’t particularly care for the neologism, but the idea behind it is spot on. This change represents a major shift in the social fabric, and it is only now just getting started. If you thought there was a lot of hair-pulling over privacy in 2009, just wait until 2010. Facebook’s new privacy policies which favor more public sharing, will be a big driver of this shift, as will the continued adoption of Twitter, which by its very design makes personal utterances public. Then there are startups like Blippy that go even further by turning every single purchase into a public statement.
It takes some getting used to the idea of living in public. As I discussed several hours ago with Andrew Keen
, in public on Twitter
, instead of making the private public, we will make the public private.” When public is the default, you deliberately select what to keep private instead of the other way around.
It’s not that privacy disappears. But it becomes more a matter of emphasis and a conscious decision. Boyd points out:
Some people are the web equivalent of nudists: they live very open lives on the web, revealing the intimate details of their relationships, what they think of friends and co-workers, their interactions with family and authorities. But . . . even these apparently wide open web denizens may keep some things private, or secret.
via Erick Schonfeld www.techcrunch.com
Turns out that Schonfeld and Andrew Keen were involved in a discussion about 'the death of privacy' when my post broke. Keen has had a long series of tweets since, including these (reverse choronology)
@jobsworth is the Calcutta model of an absence of privacy preferable to Anglo-American model of guarding individual autonomy? 6 minutes ago from TweetDeck in reply to jobsworthend of privacy as a "major change in the social fabric" http://bit.ly/63bvlb (by @erickschonfeld). actually a major threat to social fabric. 9 minutes ago from TweetDeck
Privacy overated? RT @jblossom: Yet "publicy" enables communities to form effectively. Privacy has its place, but it's overrated as a virtue 18 minutes ago from TweetDeck
can one build privacy? http://bit.ly/sUZgL if your identity is publicly displayed, then the private self may be chimerical. 23 minutes ago from TweetDeck
21st century "public" sphere is an individualized version of mass public space RT @kevinmarks: @nitin @zephoria HTTP://bit.ly/publics about 17 hours ago from TweetDeckbtw: i'm not against shrouding oneself under the veil of transparency. It's the political dress of the 21st century. about 18 hours ago from TweetDeck
is the new privacy the "plausible me"? http://bit.ly/sUZgL personally, my own goal is implausibility. about 18 hours ago from TweetDeckthe more one uses the word "transparent". the more opaque one is likely to be (Obama, Google etc etc) about 18 hours ago from TweetDeck
if the "masses" is 19th century word & "celebrity" a 20th century one, what is a 21st century word? (perhaps "publicy" http://bit.ly/5w1hlb) about 18 hours ago from TweetDeckone thing is for sure: transparency is ideology. about 18 hours ago from TweetDeck
Hegelcrunch RT @erickschonfeld: Instead of making the private public, we will make the public private about 18 hours ago from TweetDeckWell worth reading: "secrecy, privacy, publicy" by @stoweboyd (via @erickschonfeld) about 18 hours ago from TweetDeck@arrington I'm trying to think through the implications of your assertion that privacy is dead. about 19 hours ago from TweetDeck in reply to arrington
so what is 21st century word to describe people formerly known as the masses? RT @yelvington: "The masses" ... such a 19th-century concept. about 19 hours ago from TweetDeckI suspect that privilege in the digital 21st century will buy privacy. Celebrity is being commodified. Wealth will buy anonymity. about 19 hours ago from TweetDeck
have the masses always lived in public? RT @DonLinn: Um, I don't think there's anything new there. The masses have always lived in public. about 19 hours ago from TweetDeck21st century default is living in public, privacy will be the new scarcity. The privileged will have access to privacy; the masses won't. about 19 hours ago from TweetDeck
RT @gsiemens: I disagree - no one will have access to privacy. That's been amply clear this year (pick a crisis or celebrity of your choice) about 19 hours ago from TweetDeckprivacy: key scarcity of future RT @daveowhite: if privacy becomes scarce we will just have to use it more efficiently, Victorian style. about 19 hours ago from TweetDeck
is Erick right? Will the idea of personal privacy wither away in 21st century? RT @erickschonfeld: yes, we all live in public about 19 hours ago from TweetDeck
All semi-out of context, since I am not displaying the replies from others, but it shows the line that Keen is developing. I look forward to something more substantial from Andrew in the near term.
My good friend Euan Semple jumps in:
No, it's not a typo, nor the prettiest word, but having just read Stowe Boyd's post about "publicy" I like it. He defines it thus:
The idea of publicy is no more than this: rather than concealing things, and limiting access to those explicitly invited, tools based on publicy default to things being open and with open access.
Needless too say I am a fan of "publicy" and live more of my life, more openly than most, but it is not easy. Not everything is appropriate to make public and the expectation of being public can become an inhibitor as I have written before.
via The Obvious?
I will update this post as more responses come online.
-----
Via /Message
Personal comment:
La vie "publique", par défaut?
Secrecy, Privacy, Publicy
Gabriel García Márquez once wrote, "Everyone has three lives: a public life, a private life, and a secret life," a line that seems to resonate with how we live our lives today, and perhaps how we have lived since the start of human society.
In everyday speech, we have terms that relate to keeping information private or secret. We all have an intuitive sense for privacy and secrecy, and they are caught up in our sense of self, and our notions of intimacy.
Privacy concerns are constantly in the headlines, like today's NY Times piece about the possible use of 'full body scanners' to peer beneath our clothes as a response to the Abdulmutallab bomb attempt. There is a potentially irresolvable gap between the US Government's desire to increase security and our natural reluctance to have strangers see beneath our clothes.
There is a fundamentally Western perception of rights of privacy -- the right to seclude oneself -- as in the privacy of one's home -- and to conceal information from other people and the state. This includes the right to selectively decide what to reveal about oneself. The notion of what sorts of information may be kept private differs widely across cultures, and while some governments have established laws ensuring privacy rights, many do not. And other laws -- like tax laws -- explicitly require access to information that individuals might otherwise want to keep private.
Our ideas of privacy are not universal, and can't be translated well into languages where cultural norms vary greatly. For example, physical modesty varies greatly across cultures, ranging from nearly naked models on catwalks or the average person on a Miami beach, to women in Islamic countries covering their body, hair, arms, legs, and even the face. But even within a country like the US, bodily modesty varies enormously.
We find similar variability in people's notions of privacy online. Some people are the web equivalent of nudists: they live very open lives on the web, revealing the intimate details of their relationships, what they think of friends and co-workers, their interactions with family and authorities. But, as in the Márquez quote, even these apparently wide open web denizens may keep some things private, or secret.
Secrecy carries connotations beyond those linked to privacy. Secrets are often shared, and as such are social objects that link those sharing the secrets together, and excluding others. Secrecy also may imply shame, or the likelihood of repercussions if the secret is revealed. This dimension of secrecy does overlap with some of the deeper motivations for personal privacy. Lastly, corporations and governments have and keep secrets, like the Coca Cola formula or cell phone recordings of prisoners at Guantanamo. And of course, repressive governments may attempt to conceal large parts of what is going on elsewhere from their citizens, like the the way that China is selectively blocking access to the web.
Obviously secrecy and privacy are critically important aspects of what is happening on the web, and much of the design of social tools is based on certain premises about privacy and secrecy, and the role that they play in social interactions.
Consider the core premises of pre-web and Web 1.0 era collaborative tools, which are still the major form of enterprise software. These are based on the premise that an individual's rights and responsibilities are based on group membership, and the role that individuals play within these groups.
For example, if I am an employee of XYZ Inc, I might be invited to work on a Basecamp project entitled 'Johnson Widgets' and the owner of the Basecamp account gives me the capability to comment on posts, upload files, and so on, but not to delete or edits other people's contributions. Once I made privy to the Johnson project, information defaults to being available to all participants, but the project and all it's contents are secrets concealed to those outside the group.
Members of the Johnson company -- XYZ's clients -- may also be invited to work in the project. Basecamp and other collaborative tools allow users to make certain posts 'private' -- meaning concealed from certain group members. For example, I could post something and make it visible only to XZY staff and not visible to Johnson staff.
My point is not some analysis of the specifics of Basecamp. Instead, my interest is privacy and secrecy in our web interactions. Web 1.0 and earlier collaborative tools are strongly biased toward secrecy and privacy. Web 2.0 tools are a mixed-up blending of privacy and secrecy principles with the mass openness of web publishing. And now, as we are moving into a new era of the web based on social tools, what will the major structuring principles be? What core aspects of social interaction will form the basis of what is coming now?
The fundamental core of social tools is that the individual comes first: our rights and responsibilities in social tools are not derived from membership in groups (in general), but are unalienable. The baseline rights are privacy-tinged -- what to include in your profile -- but in general one's stream obviates the profile. And then, the major social angle in social tools is deciding who matter: who to follow. That is a public choice, and this is the primary bond that makes a social matrix from individuals.
There is a countervailing trend away from privacy and secrecy and toward openness and transparency, both in the corporate and government sectors. And on the web, we have had several major steps forward in social tools that suggest at least the outlines of a complement, or opposite, to privacy and secrecy: publicy.
The idea of publicy is no more than this: rather than concealing things, and limiting access to those explicitly invited, tools based on publicy default to things being open and with open access.
Tumblr is a tool based on publicy. So is Twitter. Tumblr blogs and Twitter accounts default to open unless the user takes great efforts, and as a result the resulting communities are based on sharing of posts rather than membership in closed groups.
As I have said in the past the open sharing model of Twitter and Tumblr will be the dominant motif of all successful social tools of the next decade. This will be the publicy decade, where network effects are induced by growing awareness of the benefits of publicy and the negatives of privacy and secrecy-based social tools, customs, and institutions.
Don't get me wrong: I am not calling for an end to privacy or of secrets. They have their place, just as I would not want to make women into men (or vice versa) in the name of equality. What I am saying, however, is this: the basis of future web culture and the social tools that enable it to exist will be publicy, not privacy or secrecy.
Footnote: I did a search on 'publicy' when thinking about this post, and discovered that others have advanced the term. Laurent Haug wrote this:
Now that you are back in the driver seat, you have your privacy back. Just of a different kind. You have built a space that could be called “publicy”, or “the plausible me”. It is a credible space where people expect to see information about you. Whatever credible information you say in there will be taken as true by the world.
That is your new privacy. A space that is public but that you control, where you can say anything you want and have it taken as true.
This is not dissimilar to what I am getting at, although this revealing of the self angle is pretty much what privacy is about.
I also found a Wikipedia entry for publicy, citing a paper by Martijn Veldboer, a social scientist investigating immigrant response to unfamiliar public spheres. This is positioned as the opposite of privacy, but is very narrowly applied by Veldboer.
-----
Via /Message
Personal comment:
Quelques lignes ici qui pourraient servir dans le contexte d'un projet en développement (Paranoid Shelter).
Friday, July 17. 2009
The Big Smart Grid Challenges
 |
||
| Smarter meter: Possible strategies for reducing energy consumption rely on devices that can send and receive information from utilities and communicate wirelessly with appliances. Credit: Kevin Bullis, Technology Review |
||
|
Multimedia
|
The smart grid will incorporate new networking technology, including sensors and controls that make it possible to monitor electricity use in real time and make automatic changes that reduce energy waste. Furthermore, grid operators should be able to instantly detect problems that could lead to cascading outages, like the ones that cut power to the northeastern United States in 2003. And the technology ought to allow energy companies to incorporate more intermittent, renewable sources of electricity, such as wind turbines, by keeping the grid stable in the face of minute-by-minute changes in output.
For consumers, the smart grid could also mean radical changes in the way they pay for electricity. Instead of a flat rate, they could be charged much more at times of high demand, encouraging them to reduce their energy use during these periods. Companies such as GE are developing refrigerators, dryers, and other appliances that can automatically respond to signals from the utility, shutting off or reducing energy consumption to allow consumers to avoid paying the peak prices. Such strategies could allow utilities to put off building new transmission lines and generators to meet peak demand--savings that could be important as proposed regulations on carbon dioxide emissions force them to switch to more expensive sources of electricity.
But the necessary changes could prove difficult for consumers to adjust to, says Garry Brown, chairman of the New York State Public Service Commission, a utility regulator. Industrial and commercial electricity customers already have variable electricity rates that change with the time of day, but "they have the ability and expertise and wherewithal to figure out what to do with this," Brown says. "They have a manager that spends their life trying to react to it." Ordinary consumers don't have that advantage. Indeed, in the 1990s the New York state legislature blocked mandatory variable pricing amid concerns about the impact it could have on customers who couldn't avoid peak prices, such as people who must use electric-powered medical equipment around the clock. We have to be "slow and cautious," about introducing the technology, Brown says.
The grid upgrade may also face resistance from regulators because some of the benefits are difficult to measure. Regulators are responsible for ensuring that utilities make wise investments that restrain the price of electricity. But improved efficiency and reliability can't easily be quantified, says Bryan Olnick, a senior director at the major utility Florida Power and Light. He says that regulators need to start considering long-term societal benefits in addition to electricity costs. Ultimately, regulators will need proof that the systems can deliver the promised benefits, which is why there are now smart-grid demonstration projects in places including Boulder, CO; Maui; and Miami.
Beyond the challenge of measuring results, the smart grid raises questions about national security, says Bob Gilligan, GE's vice president for transmission and distribution. "We hear a lot of concerns about cyberterrorism and attacks on our energy infrastructure," he says. "As we talk about bringing more technology into the grid, providing more connections to the energy infrastructure, there are escalating concerns about protecting that infrastructure."
Gilligan adds that the technology raises serious privacy concerns as well. "The major concern is that folks don't want to be inundated with telemarketing calls associated with their usage behavior," he says. "There's also some concern about what they're doing being known minute by minute."
The massive amount of data generated by smart-grid technology could itself pose a practical problem. Right now, a utility with five million meters has about 30,000 devices for monitoring the grid. As the smart grid develops, that number could increase a thousandfold, with each device conveying a thousand times as much information as one of its counterparts does now, says Erik Udstuen, a general manager at GE Fanuc Intelligent Platforms. Though so much data may be difficult to process, it could also create opportunities for entrepreneurs to develop new monitoring applications, especially if open standards are developed.
Consumers needn't brace themselves for changes right away; it could take a decade to implement variable pricing. Meanwhile, the grid can be improved in ways that won't affect customers directly, such as reducing the amount of energy wasted in getting power from generators to consumers: 7 to 10 percent is often lost, and that figure can reach 20 or 30 percent during periods of peak demand. Meanwhile, smart meters and appliances that allow variable pricing will cost billions to develop and could take a decade to install.
Eventually, however, the smart grid could make the supply of electricity more efficient and reliable, and it could help reduce greenhouse-gas emissions by promoting renewable technologies and reducing overall power consumption. "In the long run," says James Gallagher, a senior vice president at the New York City Development Corp, "it will lead to lower rates."
Copyright Technology Review 2009.
-----
Wednesday, July 01. 2009
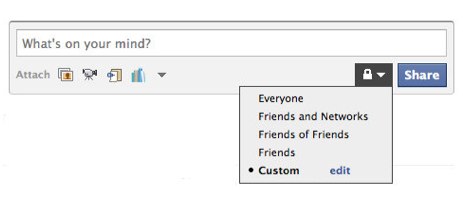
Facebook to Twannounce Twivacy Changes Twomorrow?
 Facebook is hosting a webcast for press tomorrow about “upcoming privacy changes” to the site: the announcement will likely outline Facebook’s transition toward becoming more public – some might say more Twitter-like.
Facebook is hosting a webcast for press tomorrow about “upcoming privacy changes” to the site: the announcement will likely outline Facebook’s transition toward becoming more public – some might say more Twitter-like.
We already know change is on the way: last week Facebook announced that they’re beta testing a publishing feature (with a limited number of profiles) by which your Facebook status updates can optionally be made public. In short: you’ll be able to use Facebook just like Twitter, and broadcast public updates to the world.
We also wrote about another interesting find last week: a new setting in Facebook that lets you receive an email when someone becomes a “fan” of your Facebook profile – not a friend, but actually someone who follows your personal Facebook page without you reciprocating. And a new Facebook Search is in testing too, allowing you to search updates from friends or all public publishers.
Facebook, then, is moving to a model of public updates and Twitter-like followers. The question becomes: can Facebook, which built its brand on “real names” and true friendships, also become the leader in public sharing and updates?
The MySpace Era
 The tactic is certainly in contrast to Facebook’s early years: the network went beyond MySpace and its various clones by emphasizing real relationships and extreme privacy.
The tactic is certainly in contrast to Facebook’s early years: the network went beyond MySpace and its various clones by emphasizing real relationships and extreme privacy.
Your Facebook profile was a representation of your real-life social graph, and when users tired of amassing thousands of fake MySpace friends and adding “bling” to their profiles, they flocked to Facebook’s cleaner, more controlled environment with a smaller number of high-value relationships.
Facebook even limited networks of friends to 5000 people to prevent this high-volume friend adding, which threatened to devalue the meaning of a Facebook friend. The strategy served them well; MySpace became a ghost town.
Then Twitter happened…
…and suddenly the press was in love with openness again, with our newfound ability to mine the public consciousness through Twitter search, with a new era in which there was more value to be had in sharing information than in keeping it private.
Facebook’s gated community was a lot less useful when penning a news story about the Iranian elections, or the Hudson Plane Crash, or the public reaction to Michael Jackson’s death. Less useful, too, for conscientious brands looking for customer feedback. And less valuable for finding a new, spontaneous connection with that random Twitter user who happens to discuss the same topics as you.
Twitter’s public updates – and more specifically, the mining of these updates through Twitter Search – provided a more complete database of the public consciousness than ever before, a source of untold insights.

So what do you do when you’re all about privacy, and your upstart competitor is doing the complete opposite? By making a complete about-face, Facebook would lose the faith of its 200 million+ users who value the privacy of the site most of all: it’s what the core userbase was sold on from the start.
So Facebook is trying to find a middle road whereby privacy is maintained and public sharing is an optional extra. Over time, they surely hope, the number of Facebook “public” users will exceed the total number of Twitter users. At that point, Facebook would be a more valuable resource; it would become the larger hivemind.
Who will win the race is anybody’s guess: Twitter has a singular focus and the right DNA. It has a culture of public sharing that was present from the start. Facebook has scale on its side, and would only need to convert some of its users to public sharing to maintain its lead.
It’s a race that will define social networking for months and possibly years to come. And tomorrow Facebook will likely twannounce its next step.
-----
Vis Mashable
Personal comment:
Facebook vs Twitter vs Myspace: interesting strategies regarding "real time", privacy and networked status. We can definitely see where this all thing is going.
Friday, June 12. 2009
Social Networks Keep Privacy in the Closet
 |
| Credit: Technology Review |
This situation encourages social networks to bury the privacy settings that they build, according to research that will be presented later this month at the Eighth Workshop on the Economics of Information Security, in London, U.K. Social networks are under pressure from privacy-rights groups and activists to build in ways for users to control their information, the researchers say, but it's also in their interest to keep those settings off users' minds.
"To the social network, your value increases the more data you share on the site," says Joseph Bonneau, one of two University of Cambridge researchers who worked on the project. More user data means better targeted advertising, and more of a feeling of community, he says. "Their goal is to create a very free-flowing environment where everybody is constantly sharing everything and seeing all this data on other people," he says. "The best way to achieve that is to not bring up the concept of privacy."
To arrive at their conclusions, the researchers evaluated 45 social-networking sites from all over the world, looking at more than 200 criteria related to privacy policies and privacy controls. Although social-networking sites have often been criticized as a group for their privacy practices, the researchers say that they found a lot of variation in quality. Using criteria such as the amount of data collected during sign up, the default privacy settings, and whether information is routinely shared with third parties, the researchers judged Bebo, LinkedIn, and GaiaOnline to have the best privacy practices of all, and Badoo, CouchSurfing, and MyLife to have the weakest. Ironically, sites that made privacy a selling point tended to have lower-quality privacy controls. Facebook and MySpace ranked toward the middle, but the researchers note that these sites also offer users more features, making privacy harder to maintain.
In general, more popular social-networking sites did better with privacy, which the researchers put down to these sites having more resources to devote to the problem, as well as to being under more pressure to protect user data.
Bonneau believes that revealing the privacy practices of all sites could help put pressure on major sites to add further protections for users. For example, the researchers found one site, the business network Xing, that encrypts all interactions to protect personal information against eavesdroppers. This shows what kinds of features are possible, Bonneau says.
Sören Preibusch, another researcher who worked on the project, says that establishing industry standards for privacy settings might help users understand and control what's happening to their information. Murky policies, confusing settings, and incentives to share all their information tend to distract users from the realities of what will happen to their data, he says. "Even though consumers report they are concerned about privacy, they forget their concerns when offered some rewards," Preibusch says. "Even small rewards such as chocolate bars or pennies will convince users to reveal personal information."
Vitaly Shmatikov, a professor of computer science at the University of Texas at Austin, who studies privacy in social networks, says that the implications of the new study will become increasingly important as sites develop better ways to make money from users' data. "I expect that there will be a significant tension between monetization and privacy," he says.
Incidents such as Facebook's Beacon fiasco--the site's controversial attempt to broadcast a user's offline shopping activities through Facebook--highlight the potential for conflict, Shmatikov says. However, he thinks that worse will come when social networks begin focusing less on attracting new users and more on making money from the ones they have.
By their very nature, social-networking sites are designed to "promote the open flow of personal information," says Michael Zimmer, an assistant professor at the School of Information Studies at the University of Wisconsin-Milwaukee. As a result, he says, they're "reluctant to heavily promote their privacy settings," adding, "Facebook has some of the most robust privacy settings out there but offers little to no help on how to use them."
One way to remedy this situation is by finding ways to assist users in navigating privacy settings, Zimmer says. He has, for example, posted a cheat sheet on his site that walks users through the process of configuring the privacy settings on Facebook.
Preibusch says that social-networking sites often leave user profiles almost 100 percent public by default. "Users should be aware that they still have the possibility of taking action by setting their privacy settings inside the network, and not sticking with the permissive defaults," he says.
"The safe way to use the network is to assume that everything you post will eventually be public," adds Bonneau.
Copyright Technology Review 2009.
-----
Related Links:
Personal comment:
La dernière phrase est intéressante: "The safe way to use the network is to assume that everything you post will eventually be public". Considérer les réseaux sociaux comme une place publique! Oui, mais il faut alors d'un autre côté que le design et les fonctions proposées laisse entendre que la place est publique... (alors que la tendance serait plutôt à laisser croire à une semi privacité) et que les données collectées sont elles-mêmes publique (alors qu'elles appartiennent à une société privée)! Ouvertes et exploitables par tous... Grosso modo, le deal actuel non formulé est: vos données contre notre service, dès lors gratuit.
Cela me rappelle encore une fois les enjeux développés dans notre projet "Knowscape mobile" en 2003-2005.
Tuesday, May 05. 2009
Google Latitude Lets You Share Your Location With the Masses
 For those that value their privacy, this feature isn’t for you. But if you want to share your current physical location with everyone, Google Latitude will now let you do it, with a new widget you can embed on your own website, plus an option to update your Google Talk status with your coordinates as well.
For those that value their privacy, this feature isn’t for you. But if you want to share your current physical location with everyone, Google Latitude will now let you do it, with a new widget you can embed on your own website, plus an option to update your Google Talk status with your coordinates as well.
Before today, your Latitude location was only viewable to people that you became friends with on the fledgling location-based network. But according to Google, “one frequent request was to allow you to share your location with even more people and not just your Latitude friends.” The badge can be grabbed from here, while you can enable location-sharing in Google Talk by signing into Latitude.

Although I certainly wasn’t one of the people requesting this feature, it’s not as potentially scary as it sounds. For example, the Google Talk feature only shows your current city, while the embeddable widget lets you specify the level of location you’d like to share (best available location or city).
Nonetheless, assuming some people do go ahead and enable the feature, it’s great exposure for Latitude. Other applications – like BrightKite and Plazes – already enable public location sharing, but Latitude has the advantage of already having millions of users through Google Talk that can now use this feature.
In other news, while I was impressed with Google Latitude at launch, I’m not actively using it today. Part of the reason is privacy – I’m not super stoked about sharing my location all of the time, and don’t want the hassle of turning the app on and off. Another issue is that I don’t feel like building a separate contact network, and would rather Facebook and/or Twitter simply build location-aware features.
-----
Via Mashable
Related Links:
Personal comment:
Possibilité d'être encore plus transparent ou de lâcher un peu de sa privacité vie Google Latitude!
C'est le problème de la géolocalisation: une service intéressant ouvrant de multiples possibilités, mais qui lorsque couplé à des applications et/ou des téléphones portables, ouvre le champ à la perte de la privacité (contrairement ici à un pur gps qui ne fait que recevoir des données).
Wednesday, February 18. 2009
Facebook Reverts to Previous Terms of Service
 That was quick. A day after trying to defend changes to its Terms of Use, Facebook has pulled a 180 and decided to revert to its previous terms.
That was quick. A day after trying to defend changes to its Terms of Use, Facebook has pulled a 180 and decided to revert to its previous terms.
Earlier today, the company began polling its users about the controversial changes, with only 6 percent supporting them and 56 percent opposing (the other 38 percent simply responded “don’t know”). We posted the same poll on Mashable and the results were far more decisive – 88 percent voting to revert, 7 percent to keep, and 5 percent indifferent (as of 11pm PT).
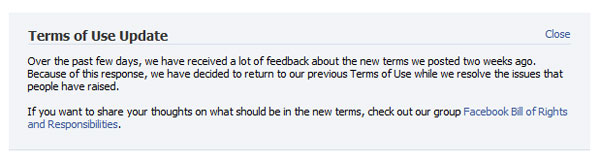
Once again, CEO Mark Zuckerberg is the one breaking the news. In a blog post, he writes, “Going forward, we’ve decided to take a new approach towards developing our terms. We concluded that returning to our previous terms was the right thing for now. As I said yesterday, we think that a lot of the language in our terms is overly formal and protective so we don’t plan to leave it there for long.”
In a smart response to what I’ve previously characterized as a breakdown in communication more than anything else, the company has also established a Facebook Bill of Rights and Responsibilities group, where members are encouraged to “give input and suggestions on Facebook’s Terms of Use.”
Smart move, Facebook. Unlike the breakdown over Beacon, which lasted for weeks, Facebook has diffused this crisis in a matter of days. Of course, it could’ve been prevented in the first place by clearly explaining the changes before posting them, but it appears Facebook has taken steps to ensure that this issue doesn’t plague the social network in the future.
---
Related Articles at Mashable | All That's New on the Web:
56 Percent of Facebook Users Want the Old ToS Back
AT&T Changing its Questionable ToS
Facebook Search in Your Inbox
Facebook Music?
Facebook Responds to Concerns Over Terms of Service
Scoble Caught Hacking Facebook
What Happened on Friday, May 30th of 2008?
-----
Via Mashable
Tuesday, February 17. 2009
Facebook Responds to Concerns Over Terms of Service
 Today’s hoopla over changes to the Facebook Terms of Service have prompted a rare blog post from Facebook founder and CEO Mark Zuckerberg. In the post, Zuckerberg falls short of apologizing for the changes, but rather, uses the opportunity to explain why Facebook more or less keeps your content indefinitely.
Today’s hoopla over changes to the Facebook Terms of Service have prompted a rare blog post from Facebook founder and CEO Mark Zuckerberg. In the post, Zuckerberg falls short of apologizing for the changes, but rather, uses the opportunity to explain why Facebook more or less keeps your content indefinitely.
He writes, “When a person shares information on Facebook, they first need to grant Facebook a license to use that information so that we can show it to the other people they’ve asked us to share it with. Without this license, we couldn’t help people share that information.” This is true – without making this part of the Terms of Service, someone could technically claim they didn’t know anyone would see their Status Updates, as silly as that may sound.
Continuing, Zuckerberg explains why the site keeps content indefinitely. “When a person shares something like a message with a friend, two copies of that information are created—one in the person’s sent messages box and the other in their friend’s inbox. Even if the person deactivates their account, their friend still has a copy of that message. We think this is the right way for Facebook to work, and it is consistent with how other services like email work.”
That makes sense as well, but I don’t think it gets to the heart of the issue that has people so concerned about Facebook’s terms of service, as the company fails to answer the question of why this piece of the TOS was removed: “You may remove your User Content from the Site at any time. If you choose to remove your User Content, the license granted above will automatically expire, however you acknowledge that the Company may retain archived copies of your User Content.”
Ultimately, Facebook’s stance can be summarized as “trust us, we won’t do anything bad.” Zuckerberg writes, “In reality, we wouldn’t share your information in a way you wouldn’t want. The trust you place in us as a safe place to share information is the most important part of what makes Facebook work.”
In the end, this fiasco isn’t going to change the way I use Facebook, and I imagine it won’t do much to alter other user’s plans either. Their terms of service, like those of any other company operating on the Web, are designed to put their interests first, and eliminate just about any potential legal risk that their lawyers can think up.
Once again though - like with Beacon and the Facebook re-design revolt - Facebook has done a poor job of communicating the changes, leaving Zuckerberg on the defense instead of proactively keeping users informed on potentially controversial moves the company is making.
Chances are Facebook won’t abuse the privileges they are granted under their TOS. The backlash over doing something insane like using member photos without permission would be enormous and Facebook is smart enough not to do it. But as a user, it’s another reminder that what you do on the Internet is probably permanent, and much of it, probably outside your control.
---
Related Articles at Mashable | All That's New on the Web:
The Daily Poll: Will Facebook Cave to Beacon Critics?
Rest Assured, Facebook Looks Out For the Children
Twitter Updates Now Connected to Facebook Status
Facebook Deleting Accounts, Profiting from Tragedy
The Daily Poll: Are You a Fan of Facebook Pages?
Facebook to Offer Block Out Options for Advertisers
Fuser’s MySpace Killer Just Got Meaner
-----
Via Mashable
Personal comment:
Mais quand même, le "terms of service" de Facebook stipule donc dorénavant que les données ne sont pas effacées lorsque l'on ferme son compte et que, surtout, tout le contenu déposé sur le site de Facebook lui appartient, "pour toujours"! On ne pourra pas se plaindre de ne pas avoir été mis au courant chers "friends"...
Facebook: All Your Stuff is Ours, Even if You Quit
 The Consumerist has noticed a seemingly slight but very important (and disturbing) change in Facebook’s terms of service, regarding user-generated content.
The Consumerist has noticed a seemingly slight but very important (and disturbing) change in Facebook’s terms of service, regarding user-generated content.
In short, all of the content you’ve ever uploaded on Facebook can be used, modified or even sublicensed by Facebook in every possible way - even if you quit the service.
The TOS says the following:
You hereby grant Facebook an irrevocable, perpetual, non-exclusive, transferable, fully paid, worldwide license (with the right to sublicense) to (a) use, copy, publish, stream, store, retain, publicly perform or display, transmit, scan, reformat, modify, edit, frame, translate, excerpt, adapt, create derivative works and distribute (through multiple tiers), any User Content you (i) Post on or in connection with the Facebook Service or the promotion thereof subject only to your privacy settings or (ii) enable a user to Post, including by offering a Share Link on your website and (b) to use your name, likeness and image for any purpose, including commercial or advertising, each of (a) and (b) on or in connection with the Facebook Service or the promotion thereof.
It also used to contain another bit that is now missing.
You may remove your User Content from the Site at any time. If you choose to remove your User Content, the license granted above will automatically expire, however you acknowledge that the Company may retain archived copies of your User Content.
This is also reinforced by the “Termination” section:
The following sections will survive any termination of your use of the Facebook Service: Prohibited Conduct, User Content, Your Privacy Practices, Gift Credits, Ownership; Proprietary Rights, Licenses, Submissions, User Disputes; Complaints, Indemnity, General Disclaimers, Limitation on Liability, Termination and Changes to the Facebook Service, Arbitration, Governing Law; Venue and Jurisdiction and Other.
Sure, most users don’t really care (or think they don’t care) about all this, but the idea that you now cannot stop Facebook from using your content should you ever want to is frightening to say the least.
Is Facebook Connect the reason?
Commenter OrtensiaCadmium on Consumerist finds a probable reason for this change in Facebook TOS.
“That’s fairly common language in terms for various sites such as Facebook. While it gives Facebook some far-reaching and scary possibilities, the basic idea is that things you upload may end up residing on servers outside of Facebook’s direct control. These broad rights make it so that you can’t sue Facebook for some cached content on some other server…”
Yes, with Facebook Connect in place, it’s likely that Facebook simply must do this in order to avoid possible lawsuits over content that isn’t even stored by them anymore. However, the same commenter rightfully notices that “…yes, it also means they can sell your photos or use them in advertising with no recompense to you.”
It’s not just your stuff, it’s everyone’s stuff
The possible implications of this TOS change go beyond these concerns. Sure, you can choose not to use Facebook at all, but that doesn’t mean a thing. Someone can still take your photo, slap it on Facebook, and now neither you nor the author of the photo can stop Facebook from using the photo in whichever way they please.
Looking at it globally, millions of people are uploading bits of information on everyone and everything, to a huge online database, and by doing so they’re automatically giving away the rights to use or modify this information to a private corporation. And not only that; they now also waiver the right to ever take it back from it.
Facebook should take a long, deep look into how it treats its users. Until now, users had options with regards to how the data they generated on Facebook was used. Now, they have no options whatsoever, rather than quit the service altogether. It’s a major difference; I’m not going to take it lightly, and neither should you.
---
Related Articles at Mashable | All That's New on the Web:
Facebook Pimps Privacy, Calls in CIA
Google To Microsoft: We’re Serious About Privacy
Facebook Opening Their App Directory To The Web
Facebook Beacon Collects Data on Non-Users Too
Facebook Updates Privacy and Planning to Add Chat
Facebook Profiles Will Appear in Google Results Next Month
Facebook Mobile Bug Compromises Account Privacy Settings
-----
Via Mashable
Personal comment:
Wow! Assez gros, fallait oser... Ca va chauffer sur FB, c'est certain! Un/Des groupe/s a/ont bien entendu été créé sur FB pour contrer cette modification du TOS (c'est une attitude assez légere tout de même --et une très mauvaise communication--, puisqu'elle est de facto imposée aux personnes déjà membres du site et qui s'étaient inscrites sous d'autres "terms of service"...)
Autant donc dorénavant considérer FB comme un espace public... et de s'y comporter comme tel. Nous avions avancé une telle idée dans nos projets Knowscape et Knowscape mobile il y a 6 ans de cela. A la différence près que les données en question étaient certes publiques, mais également open source (n'appartenant donc pas à une société privée, mais à tout le monde!).
fabric | rblg
This blog is the survey website of fabric | ch - studio for architecture, interaction and research.
We curate and reblog articles, researches, writings, exhibitions and projects that we notice and find interesting during our everyday practice and readings.
Most articles concern the intertwined fields of architecture, territory, art, interaction design, thinking and science. From time to time, we also publish documentation about our own work and research, immersed among these related resources and inspirations.
This website is used by fabric | ch as archive, references and resources. It is shared with all those interested in the same topics as we are, in the hope that they will also find valuable references and content in it.
Quicksearch
Categories
Calendar
|
|
April '24 | |||||
| Mon | Tue | Wed | Thu | Fri | Sat | Sun |
| 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| 8 | 9 | 10 | 11 | 12 | 13 | 14 |
| 15 | 16 | 17 | 18 | 19 | 20 | 21 |
| 22 | 23 | 24 | 25 | 26 | 27 | 28 |
| 29 | 30 | |||||

