Friday, January 24. 2014
Bracket [takes action] | #call
A new call by the very interesting Bracket magazine/books!
Via Bracket
-----
Bracket [takes action]
“When humans assemble, spatial conflicts arise. Spatial planning is often considered the management of spatial conflicts.” —Markus Miessen
Hannah Arendt’s 1958 treatise The Human Condition cites “action” as one of the three tenants, along with labor and work, of the vita active (active life). Action, she writes, is a necessary catalyst for the human condition of plurality, which is an expression of both the common public and distinct individuals. This reading of action requires unique and free individuals to act toward a collective project and is therefore simultaneously ‘bottom-up’ and ‘top-down’. In the more than fifty years since Arendt’s claims, the public realm in which action materializes, and the means by which action is expressed, has dramatically transformed. Further, spatial practice’s role in anticipating, planning, or absorbing action(s) has been challenged, yielding difficulty in the design of the ‘space of appearance,’ Arendt’s public realm.
Our young century has already seen contested claims of design’s role in the public realm by George Baird, Lieven De Cauter, Markus Meissen, Jan Gehl, among others. Perhaps we could characterize these tensions as a ‘design deficit’, or a sense that design does not incite ‘action’, in the Arendtian sense. Amongst other things, this feeling is linked to the rise of neo-liberal pluralism, which marks the transition from public to publics, making a collective agenda in the public realm often illegible. Bracket [takes action] explores the complex relationship between spatial design, and the public(s) as well as action(s) it contains. How can design catalyze a public and incite platforms for action?
Consider two images indicative of contemporary action within the public realm of our present century: (i) the June 2009 opening of the High Line Park in New York City, and (ii) the January 2011 occupation of Tahrir Square in Cairo. These two spaces and their respective contemporary publics embody the range within today’s space of appearance. At the High Line, the urban public is now choreographed in a top-down manner along a designed, former infrastructure with an endless supply of vistas into an urban private realm. In Tahrir Square, an assembled swirling public occupies, and therefore re-designs, an infrastructural plaza overwhelming a government and communication networks. This example reveals a bottom-up, self-assembling public. But what role did spatial practice play in each of these scenarios and who were the spatial practitioners and public(s)? The contrast of two positions on action in a public realm offers an opening for wider investigations into spatial practice’s role and impact on today’s public(s) and their action(s).
Bracket [takes action] asks: What are the collective projects in the public realm to act on? How have recent design projects incited political or social action? How can design catalyze a public, as well as forums for that public to act? What is the role of spatial practice to instigate or resist public actions? Bracket 4 provokes spatial practice’s potential to incite and respond to action today.
The fourth edition of Bracket invites design work and papers that offer contemporary models of spatial design that are conscious of their public intent and actively engaged in socio-political conditions. It is encouraged, although not mandatory, that submissions documenting projects be realized. Positional papers should be projective and speculative or revelatory, if historical. Suggested subthemes include:
Participatory ACTION – interactive, crowd-sourced, scripted
Disputed PUBLICS – inconsistent, erratic, agonized
Deviant ACTION – subversive, loopholes, reactive
Distributed PUBLICS – broadcasted, networked, diffused
Occupy ACTION – defiant, resistant, upheaval
Mob PUBLICS – temporary, forceful, performative
Market ACTION – abandoning, asserting, selecting
The editorial board and jury for Bracket 4 includes Pier Vittorio Aureli, Vishaan Chakrabarti, Adam Greenfield, Belinda Tato, Yoshiharu Tsukamoto as well as co-editors Neeraj Bhatia and Mason White.
Deadline for Submissions: February 28, 2014
Please visit www.brkt.org for more info.
Related Links:
Friday, January 17. 2014
Sync Your Files without Trusting the Cloud | #data #cloud
-----
The company behind the Bittorrent protocol is working on software that can replicate most features of file-syncing services without handing your data to cloud servers.
By Tom Simonite on January 17, 2014

Data dump: New software from Bittorrent can synchronize files between computers and mobile devices without ever storing them in a data center like this one.
The debate over how much we should trust cloud companies with our data (see “NSA Spying Is Making Us Less Safe”) was reawakened last year after revelations that the National Security Agency routinely harvests data from Internet companies including Google, Microsoft, Yahoo, and Facebook.
Bittorrent, the company behind the sometimes controversial file-sharing protocol of the same name, is hoping that this debate will drive adoption of its new file-syncing technology this year. Called Bittorrent Sync, it synchronizes folders and files on different computers and mobile devices in a way that’s similar to what services like Dropbox offer, but without ever copying data to a central cloud server.
Cloud-based file-syncing services like Dropbox and Microsoft’s SkyDrive route all data via their own servers and keep a copy of it there. The Bittorrent software instead has devices contact one another directly over the Internet to update files as they are added or changed.
That difference in design means that people using Bittorrent Sync don’t have to worry about whether the cloud company hosting their data is properly securing it against rogue employees or other threats.
Forgoing the cloud also means that data shared using Bittorrent Sync could be harvested by the NSA or another agency only by going directly to the person or company controlling the synced devices. Synced data does travel over the public Internet, where it might be intercepted by a surveillance agency such as the NSA, which is known to collect data directly from the Internet backbone, but it travels in a strongly encrypted form. One drawback of Bittorrent Sync’s design is that two devices must both be online at the same time for them to synchronize, since there’s no intermediary server to act as an always-on source.
Bittorrent Sync is available now as a free download for PCs and mobile devices, but in a beta version that lacks the polish and ease of use of many consumer applications. Bittorrent CEO Eric Klinker says the next version, due this spring, will feature major upgrades to the interface that will make the software more user friendly and in line with its established cloud-based competitors.
Klinker says Bittorrent Sync shows how popular applications of the Internet can be designed in a way that gives people control of their own data, despite prevailing trends. “Pick any app on the Web today, it could be Twitter, e-mail, search, and it has been developed in a very centralized way—those businesses are built around centralizing information on their servers,” he says. “I’m trying to put more power in the hands of the end user and less in the hands of these companies and other centralizing authorities.”
Anonymous data sent back to Bittorrent by its software indicates that more than two million people are already using it each month. Some of those people have found uses that go beyond just managing files. For example, the company says one author in Beijing uses Bittorrent Sync to distribute blog posts on topics sensitive with Chinese authorities. And one U.S. programmer built a secure, decentralized messaging system on top of the software.
Klinker says that companies are also starting to use Bittorrent Sync to keep data inside their own systems or to avoid the costs of cloud-based solutions. He plans to eventually make Bittorrent Sync pay for itself by finding a way to sell extra services to corporate users of the software.
Given its emphasis on transparency and data ownership, Bittorrent has been criticized by some for not releasing the source code for its application. Some in the tech- and privacy-savvy crowd attracted by Bittorrent Sync’s decentralized design say this step is necessary if people are to be sure that no privacy-compromising bugs or backdoors are hiding in the software.
Klinker says he understands those concerns and may yet decide to release the source code for the software. “It’s a fair point, and we understand that transparency is good, but it opens up vulnerabilities, too,” he says. For now the company prefers to keep the code private and perform security audits behind closed doors, says Klinker.
Jacob Williams, a digital forensic scientist with CSR Group, says that stance is defensible, although he generally considers open-source programs to be more secure than those that aren’t. “Open source is a double-edged sword,” says Williams, because finding subtly placed vulnerabilities is very challenging, and because open-source projects can be split off into different versions, which dilutes the number of people looking at any one version.
Williams’s own research has shown how Dropbox and similar services could be used to slip malicious software through corporate firewalls because they are configured to use the same route as Web traffic, which usually gets a free pass (see “Dropbox Can Sync Malware”). Bittorrent Sync is configured slightly differently, he says, and so likely doesn’t automatically open up an open channel to the Internet. However, “Bittorrent Sync will likely require changes to the firewall in any moderately secure network,” he notes.
Wednesday, January 15. 2014
Intel Edison: A Computer in an SD Card | #computing #everyware
Via Make
-----

Intel’s new single board computer, Edison, takes on a familiar form factor. Jammed into an SD card, the 400MHz Quark processor on board has two cores, flash memory, and includes Wi-Fi and Bluetooth Low Energy for communication. It runs Linux on one core and a real time operating system on the other. You can program Edison by inserting the board into the SD card reader of your computer. The pins on the bottom of the board are capable of GPIO, UART, I2C, SPI, and PWM. “It can be designed to work with most any device—not just computers, phones, or tablets, but chairs, coffeemakers, and even coffee cups,” according to Intel’s press release. “The possibilities are endless for entrepreneurs and inventors of all kinds.” At first glance, I think this could be a good board for makers as well.
Check out the video below for more about Intel’s newest dev board including some test implementations from Thomas Lipoma, the founder of Rest Devices, the makers of the Mimo baby monitor.
Does humanitys tightening grip on the fate of nature portend new sources of global conflict? | #climate #geoengineering
-----
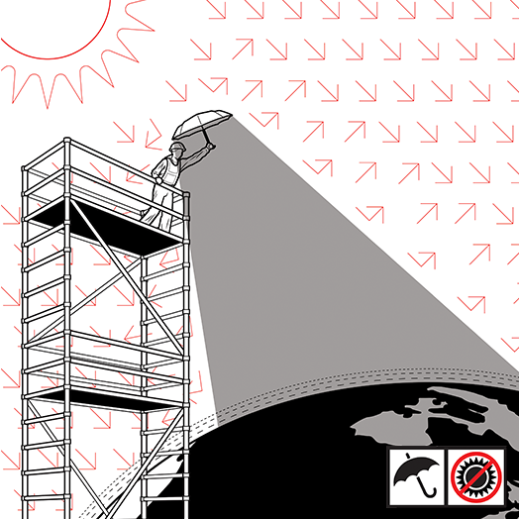
Illustration by McKibillo
More than a decade ago, Paul Crutzen, who won the 1995 Nobel Prize in chemistry for his research on the destruction of stratospheric ozone, popularized the term “Anthropocene” for Earth’s current geologic state. One of the more radical extensions of his idea—that human activity now dominates the planet’s forests, oceans, freshwater networks, and ecosystems—is the controversial concept of geoengineering, deliberately tinkering with the climate to counteract global warming. The logic is straightforward: if humans control the fate of natural systems, shouldn’t we use our technology to help save them from the risks of climate change, given that there’s little hope of cutting emissions enough to stop the warming trend?
In recent years a number of scientists—including Crutzen himself in 2006—have called for preliminary research into geoengineering techniques such as using sulfur particles to reflect some of the sun’s light back into space. With the publication of A Case for Climate Engineering, David Keith, a Harvard physicist and energy policy expert, goes one step further. He lays out arguments—albeit hedged with caveats—for actually deploying geoengineering. He says that releasing sun-blocking aerosol particles in the stratosphere (see “A Cheap and Easy Plan to Stop Global Warming,” March/April 2013) “is doable in the narrow technocratic sense.”
Indeed, Keith is steadfastly confident about the technical details. He says a program to cool the planet with sulfate aerosols—solar geoengineering—could probably begin by 2020, using a small fleet of planes flying regular aerosol-spraying missions at high altitudes. Since sunlight drives precipitation, could reducing it lead to droughts? Not if geoengineering was used sparingly, he concludes.
Australian ethicist Clive Hamilton calls the book “chilling” in its technocratic confidence. But Keith and Hamilton do agree on one thing: solar geoengineering could be a major geopolitical issue in the 21st century, akin to nuclear weapons during the 20th—and the politics could, if anything, be even trickier and less predictable. The reason is that compared with acquiring nuclear weapons, the technology is relatively easy to deploy. “Almost any nation could afford to alter the Earth’s climate,” Keith writes. That fact, he says, “may accelerate the shifting balance of global power, raising security concerns that could, in the worst case, lead to war.”
Thing reviewed
A Case for Climate Engineering
David Keith MIT Press, 2013
The potential sources of conflict are myriad. Who will control Earth’s thermostat? What if one country blames geoengineering for famine-inducing droughts or devastating hurricanes? No treaties ban climate engineering explicitly. And it’s not clear how such a treaty would operate.
Keith professes ambivalence about whether humans are truly able to wield such powerful technology wisely. Yet he feels that the more information scientists uncover about the risks of geoengineering, the lower the chances the technology will be used recklessly. Though his book leaves unanswered many of the questions that arise over how to govern geoengineering, a policy paper that he published in Science last year goes further to address them: he and a coauthor proposed government authority over research and a moratorium on large-scale geoengineering but said there should be no treaties regulating small-scale experiments.
Hamilton says this approach would lead nations on a path toward the conflict that he thinks would inevitably surround geoengineering. Allowing lightly regulated small experiments, he suggests, could undermine the urgency of political efforts toward cutting emissions. This, in turn, increases the possibility that geoengineering will be used, since failing to restrain emissions will leave temperatures rising. Hamilton accuses Keith of seeking a “naïve … cocoon of scientific neutrality” and says researchers cannot “absolve themselves of responsibility for how their schemes might be used or misused in the future.”
That may be true, but Keith deserves credit for directing attention to ideas he knows are dangerous. Accepting the concept of the Anthropocene means accepting that humans have the responsibility to find technological fixes for disasters they have created. But little progress has been made toward a process for rationally supervising such activity on a global scale. We need a more open discussion about a seemingly outlandish but real geopolitical risk: war over climate engineering.
Personal comment:
"Who will control Earths thermostat?" Oh well, following yesterday's news, I would suggest Google, they have "smart" technology ...
By the way, will we also reach some "climate neutrality quash" one day (compared to "net neutrality quashed" by a federal court), once global weather will definitely be an artifact and a product?
Nice organisms finish first: Why cooperators always win in the long run | #selfish #evolution
Via phys.org
-----
"We found evolution will punish you if you're selfish and mean," said lead author Christoph Adami, MSU professor of microbiology and molecular genetics. "For a short time and against a specific set of opponents, some selfish organisms may come out ahead. But selfishness isn't evolutionarily sustainable."
The paper "Evolutionary instability of Zero Determinant strategies demonstrates that winning isn't everything," is co-authored by Arend Hintze, molecular and microbiology research associate, and published in the Aug. 1, 2013 issue of Nature Communications.
Game theory is used in biology, economics, political science and other disciplines. Much of the last 30 years of research has focused on how cooperation came to be, since it's found in many forms of life, from single-cell organisms to people.
Researchers use the prisoner's dilemma game as a model to study cooperation. In it, two people have committed a crime and are arrested. Police offer each person a deal: snitch on your friend and go free while the friend spends six months in jail. If both prisoners snitch, they both get three months in jail. If they both stay silent, they both get one month in jail for a lesser offense. If the two prisoners get a chance to talk to each other, they can establish trust and are usually more likely to cooperate because then both of them only spend one month in jail. But if they're not allowed to communicate, the best strategy is to snitch because it guarantees the snitcher doesn't get the longer jail term.
The game allows scientists to study a basic question faced by individuals competing for limited resources: do I act selfishly or do I cooperate? Cooperating would do the most good for the most individuals, but it might be tempting to be selfish and freeload, letting others do the work and take the risks.
In May 2012, two leading physicists published a paper showing their newly discovered strategy – called zero-determinant—gave selfish players a guaranteed way to beat cooperative players.
"The paper caused quite a stir," said Adami. "The main result appeared to be completely new, despite 30 years of intense research in this area."
Adami and Hintze had their doubts about whether following a zero determinant strategy (ZD) would essentially eliminate cooperation and create a world full of selfish beings. So they used high-powered computing to run hundreds of thousands of games and found ZD strategies can never be the product of evolution. While ZD strategies offer advantages when they're used against non-ZD opponents, they don't work well against other ZD opponents.
"In an evolutionary setting, with populations of strategies, you need extra information to distinguish each other," Adami explained.
So ZD strategies only worked if players knew who their opponents were and adapted their strategies accordingly. A ZD player would play one way against another ZD player and a different way against a cooperative player.
"The only way ZD strategists could survive would be if they could recognize their opponents," Hintze added. "And even if ZD strategists kept winning so that only ZD strategists were left, in the long run they would have to evolve away from being ZD and become more cooperative. So they wouldn't be ZD strategists anymore."
Both Adami and Hintze are members of the BEACON Center for the Study of Evolution in Action, a National Science Foundation Center that brings together biologists, computer scientists, engineers and researchers from other disciplines to study evolution as it happens.
The research also makes that case that communication and information are necessary for cooperation to take place.
"Standard game theory doesn't take communication into account because it's so complicated to do the math for the expected payoffs," Adami explained. "But just because the math doesn't exist and the general formula may never be solved, it doesn't mean we can't explore the idea using agent-based modeling. Communication is critical for cooperation; we think communication is the reason cooperation occurs. It's generally believed that there are five independent mechanisms that foster cooperation. But these mechanisms are really just ways to ensure that cooperators play mostly with other cooperators and avoid all others. Communication is a universal way to achieve that. We plan to test the idea directly in yeast cells."
Provided by Michigan State University
fabric | rblg
This blog is the survey website of fabric | ch - studio for architecture, interaction and research.
We curate and reblog articles, researches, writings, exhibitions and projects that we notice and find interesting during our everyday practice and readings.
Most articles concern the intertwined fields of architecture, territory, art, interaction design, thinking and science. From time to time, we also publish documentation about our own work and research, immersed among these related resources and inspirations.
This website is used by fabric | ch as archive, references and resources. It is shared with all those interested in the same topics as we are, in the hope that they will also find valuable references and content in it.
